Experience the roller coaster of the
gaming world
Latest on Blog
![Alabaster Dawn Planned to Have 30-60 Hours of Playtime, Demo Launching in Early 2025 Alabaster Dawn Planned to Have 30-60 Hours of Playtime, Demo Launching in Early 2025]() News
Alabaster Dawn Planned to Have 30-60 Hours of Playtime, Demo Launching in Early 2025
Radical Fish Games has made an exciting announcement regarding their upcoming action RPG, Alabaster Dawn, which is set to enter early access in 2025. In the recent Steam listing, the developer shared that players can expect a gameplay duration ranging from 30 to 60 hours, mirroring the experience offered in their previous title, Crosscode.
The game will feature seven distinct regions and introduce new mechanics, including the ability to reconstruct settlements and establish trade routes. This dynamic will allow settlements to grow and evolve, ultimately leading to the opening of "new paths and opportunities." Players can also look forward to uncovering numerous secrets along their journey.
In anticipation of the release, a public demo will debut in early 2025. The studio mentioned that a vertical slice of the game has been under development throughout the year, showcasing a variety of scripted cutscenes, two challenging bosses, and an intriguing dungeon. The initial one to two hours is reported to be "almost fully playable," with the pace of development expected to accelerate as more systems are integrated. The forthcoming demonstration will showcase this specific segment, allowing players to sample what lies ahead.
The decision for early access aims to gather ongoing feedback from a broader audience, ultimately enhancing the gaming experience while also ensuring financial backing. Although CrossCode had a similar early access phase prior to its release, Radical Fish Games hopes that the timeline for Alabaster Dawn will be shorter.
Representatives and attendees of Gamescom will have an opportunity to explore the latest Alabaster Dawn build at the developer's booth.
News
Alabaster Dawn Planned to Have 30-60 Hours of Playtime, Demo Launching in Early 2025
Radical Fish Games has made an exciting announcement regarding their upcoming action RPG, Alabaster Dawn, which is set to enter early access in 2025. In the recent Steam listing, the developer shared that players can expect a gameplay duration ranging from 30 to 60 hours, mirroring the experience offered in their previous title, Crosscode.
The game will feature seven distinct regions and introduce new mechanics, including the ability to reconstruct settlements and establish trade routes. This dynamic will allow settlements to grow and evolve, ultimately leading to the opening of "new paths and opportunities." Players can also look forward to uncovering numerous secrets along their journey.
In anticipation of the release, a public demo will debut in early 2025. The studio mentioned that a vertical slice of the game has been under development throughout the year, showcasing a variety of scripted cutscenes, two challenging bosses, and an intriguing dungeon. The initial one to two hours is reported to be "almost fully playable," with the pace of development expected to accelerate as more systems are integrated. The forthcoming demonstration will showcase this specific segment, allowing players to sample what lies ahead.
The decision for early access aims to gather ongoing feedback from a broader audience, ultimately enhancing the gaming experience while also ensuring financial backing. Although CrossCode had a similar early access phase prior to its release, Radical Fish Games hopes that the timeline for Alabaster Dawn will be shorter.
Representatives and attendees of Gamescom will have an opportunity to explore the latest Alabaster Dawn build at the developer's booth.
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-08-13
Ethan Blackstone
2024-08-13
-
![CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025 CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025]() News
CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025
In 2021, Radical Fish Games initially introduced a new action RPG titled Project Terra. Now, they have officially named it Alabaster Dawn and announced that it will be available in Steam Early Access in late 2025.
The narrative centers around Juno, referred to as the “Outcast Chosen.” She awakens to find herself in a devastated world and embarks on a quest to revive humanity while confronting the enigmatic Nyx, who seems to be linked to the calamity that has befallen civilization. Fans of CrossCode will recognize familiar elements in the combat mechanics, world layout, and platforming aspects. The traditional four elemental forces return, but players now have access to eight distinct weapons.
Each of the four elements corresponds to two different weapons, allowing for a flexible combat experience. Additionally, the game will feature Combat Arts, which offers a range of techniques to use in battles, along with brand-new Divine Arts. Participants will be able to explore the expansive terrain, collect an assortment of precious Stones, obtain resources for upgrades, and discover culinary formulas that enable them to create dishes providing short-term advantages.
While Alabaster Dawn does not have a specific release date set yet, it has been confirmed for future availability on consoles and PC, creating excitement within the gaming community.
News
CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025
In 2021, Radical Fish Games initially introduced a new action RPG titled Project Terra. Now, they have officially named it Alabaster Dawn and announced that it will be available in Steam Early Access in late 2025.
The narrative centers around Juno, referred to as the “Outcast Chosen.” She awakens to find herself in a devastated world and embarks on a quest to revive humanity while confronting the enigmatic Nyx, who seems to be linked to the calamity that has befallen civilization. Fans of CrossCode will recognize familiar elements in the combat mechanics, world layout, and platforming aspects. The traditional four elemental forces return, but players now have access to eight distinct weapons.
Each of the four elements corresponds to two different weapons, allowing for a flexible combat experience. Additionally, the game will feature Combat Arts, which offers a range of techniques to use in battles, along with brand-new Divine Arts. Participants will be able to explore the expansive terrain, collect an assortment of precious Stones, obtain resources for upgrades, and discover culinary formulas that enable them to create dishes providing short-term advantages.
While Alabaster Dawn does not have a specific release date set yet, it has been confirmed for future availability on consoles and PC, creating excitement within the gaming community.
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-08-12
Ethan Blackstone
2024-08-12
-
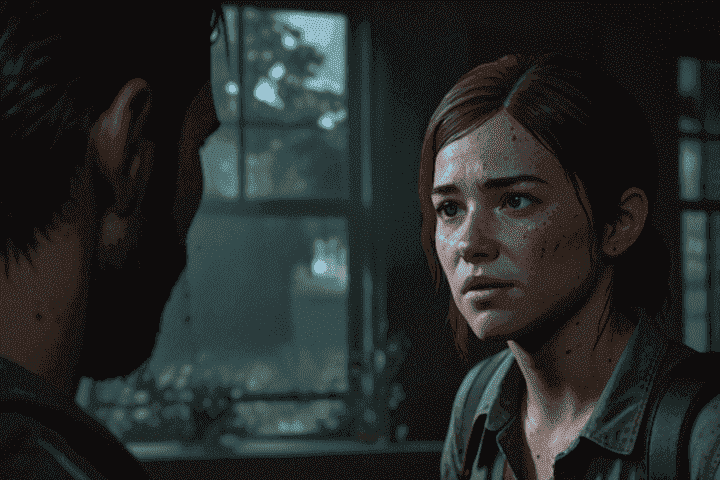
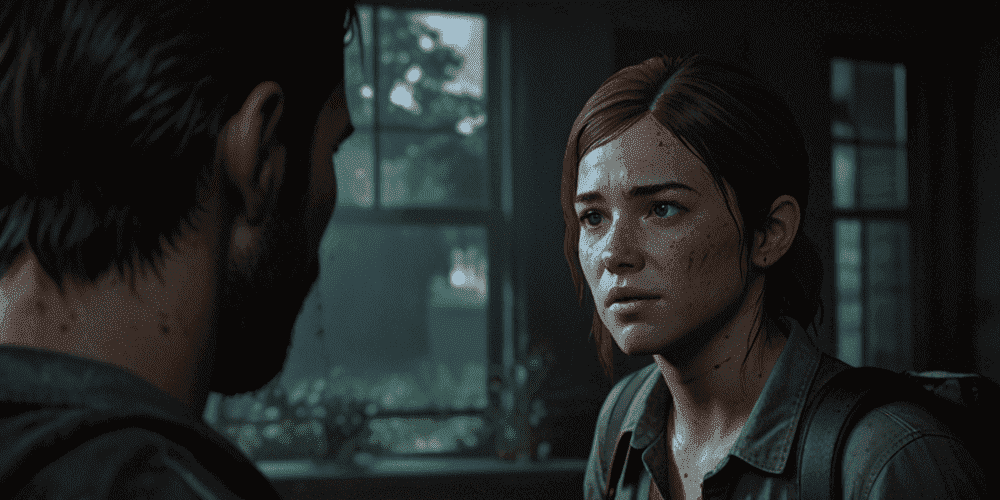
![The Last of Us Part II: In-Depth Character Analysis and Storyline Exploration The Last of Us Part II: In-Depth Character Analysis and Storyline Exploration]() Editor’s Choice
The Last of Us Part II: In-Depth Character Analysis and Storyline Exploration
The Last of Us Part II is an action-adventure video game that has gained significant popularity since its inception. Developed with immense creative prowess by Naughty Dog and published by the renowned Sony Interactive Entertainment, this video game has managed to carve a niche for itself in the competitive world of gaming. The distinct element that elevates this game's renown is its remarkable gameplay that enthralls both veteran game enthusiasts and fledgling players in equal measure.
The gaming encounter takes place in a world devastated by a catastrophic event, creating an enthralling canvas for the gameplay. However, it's not just the high-octane action sequences that make this game stand out. The heart of The Last of Us Part II lies in its deep storytelling, which proves to be just as, if not more, gripping as its action.
The depth of the characters in this game is truly commendable. The creators focused on building characters that are both relatable and complex, thereby ensuring the gamers' emotional investment in the plot. Alongside the main characters, the minor characters have also been carefully crafted, resulting in a realistic and immersive gaming experience.
Another important aspect that elevates The Last of Us Part II to a new level is its intricately woven plot. The complexity and layers of the story intrigue gamers, prompting them to delve deeper into the game's universe. It is this combination of deep characters and a well-crafted plot that provides the game its unique brand of strength and appeal.
In this article, we aim to delve further into the game's universe. We will be exploring the game's main characters, their development throughout the story, and the nuanced storyline that keeps the players hooked. By understanding these aspects in more depth, we can appreciate the ingenuity and hard work behind this successful game.
Main Characters and Character Development
The Last of Us Part II centers its narrative largely around two characters, Ellie and Abby. These individuals aren't mere characters in the gaming world, but rather, they are the backbone of this sequel, playing integral roles in driving the game's complex storyline. Their well-crafted persona and emotional depth bring a level of realness to the game that is rare to find, offering players the opportunity to delve deeper into their motives, thoughts, and actions.
Breaking away from the traditional approach of its predecessor, The Last of Us Part II takes a bold step in storytelling by providing a dual perspective in its narrative. This unique spin allows the players to experience the story from both Ellie's and Abby's points of view, lending much-needed depth to the storyline. It also highlights the subjectivity of human perception and experience as the same event unfolds differently in each character's gameplay, hence leaving the players with a broader outlook and understanding of the story.
The characters, Ellie and Abby, undergo elaborate character arcs throughout the game. They evolve tremendously; their growth is evident in their changing ideologies, decisions, and varying responses to the challenges they confront. By focusing on their character development, the game manages to convey the profound impacts of their life experiences and challenges faced in the post-apocalyptic world on their personalities.
Lastly, the game navigates through the complexities of Ellie and Abby's actions and emotions. It unearths the reasons behind their decisions, their conflicting emotions, and their struggle with their past and present. This exploration of complexity drives home the point that the characters aren't merely heroes or villains but complex individuals caught in a world where survival takes precedence over everything else.
Ellie: The Haunted Protagonist
Ellie, a nineteen-year-old survivor, sets out on a journey of retribution when a tragedy befalls her peaceful life in the post-apocalyptic world. Her character undergoes layers of transformation, moving from a carefree teenager to a revenge-driven individual. Her decisions, guided by pain and rage, paint a heart-wrenching picture of human vulnerability and resilience.
Abby: The Conflicted Antagonist
Abby's character challenges conventional villain templates. She evolves from a character initially perceived as ruthless to revealing her humane side shadowed by her past. Abby's quest for redemption, contrasted with her violent actions, incites conflicting emotions among players, thus enriching the narrative.
Secondary Characters: Their Impact and Role
Several secondary characters play crucial roles across the game, aiding and influencing the main characters' journey in profound ways. Key characters include Joel, Dina, and Isaac.
Joel: The Lingering Spirit
While the game starts with Joel's brutal end, his influence persists throughout the narrative. His actions in the prequel lay the groundwork for the events in The Last of Us Part II, leaving Ellie and Abby to suffer the repercussions of his choices.
Dina: Ellie's Anchor
Dina, a key ally and love interest of Ellie, provides solace and helps Ellie retain her humanity. Her character demonstrates the power of love and friendship in extreme circumstances and the consequences of their loss.
Isaac: The Cold Strategist
Isaac, the strategic leader of the Washington Liberation Front, plays an essential role in the war between factions. He illustrates the dehumanizing effects of long-term conflict and the cost of dogmatism.
Plot Analysis: The Multifaceted Storyline
The Last of Us Part II weaves an intricate tale revolving around both its hero and villain, probing profound undertones of existence, vengeance, affection, and atonement.
Survival and Revenge
The gaming narrative portrays the brutal truths of a world that has undergone an apocalypse, wherein the battle for survival is an unending challenge. Revenge emerges as a driving force, coloring the decisions and actions of the main characters while underlining the damaging effects of this dangerous pursuit.
Love and Redemption
Balancing the bleak aspects of the storyline are themes of love and redemption. These themes explore how love can act as a stabilizing influence and how redemption might be possible even in the most despairing circumstances. They add emotional depth and intricacy to the narrative.
Controversial Storytelling and Player Interpretations
The Last of Us Part II has incited polarizing reactions among players due to its unconventional storytelling and character development. Contemporary thematic exploration and unexpected character arcs have led to various interpretations and theories among the fanbase.
Conclusion: Assessing the Narrative Impact
The Last of Us Part II offers a highly immersive experience through compelling characters and a thought-provoking storyline. Its characters challenge traditional boundaries, growing and evolving through personal losses and wins. The multifaceted narrative blends elements of survival, revenge, love, and redemption, invoking strong emotions and prompting players to delve deeper. Despite its polarizing reception, the game ultimately solidifies its standing as a profound exploration of human nature in extreme circumstances.
Editor’s Choice
The Last of Us Part II: In-Depth Character Analysis and Storyline Exploration
The Last of Us Part II is an action-adventure video game that has gained significant popularity since its inception. Developed with immense creative prowess by Naughty Dog and published by the renowned Sony Interactive Entertainment, this video game has managed to carve a niche for itself in the competitive world of gaming. The distinct element that elevates this game's renown is its remarkable gameplay that enthralls both veteran game enthusiasts and fledgling players in equal measure.
The gaming encounter takes place in a world devastated by a catastrophic event, creating an enthralling canvas for the gameplay. However, it's not just the high-octane action sequences that make this game stand out. The heart of The Last of Us Part II lies in its deep storytelling, which proves to be just as, if not more, gripping as its action.
The depth of the characters in this game is truly commendable. The creators focused on building characters that are both relatable and complex, thereby ensuring the gamers' emotional investment in the plot. Alongside the main characters, the minor characters have also been carefully crafted, resulting in a realistic and immersive gaming experience.
Another important aspect that elevates The Last of Us Part II to a new level is its intricately woven plot. The complexity and layers of the story intrigue gamers, prompting them to delve deeper into the game's universe. It is this combination of deep characters and a well-crafted plot that provides the game its unique brand of strength and appeal.
In this article, we aim to delve further into the game's universe. We will be exploring the game's main characters, their development throughout the story, and the nuanced storyline that keeps the players hooked. By understanding these aspects in more depth, we can appreciate the ingenuity and hard work behind this successful game.
Main Characters and Character Development
The Last of Us Part II centers its narrative largely around two characters, Ellie and Abby. These individuals aren't mere characters in the gaming world, but rather, they are the backbone of this sequel, playing integral roles in driving the game's complex storyline. Their well-crafted persona and emotional depth bring a level of realness to the game that is rare to find, offering players the opportunity to delve deeper into their motives, thoughts, and actions.
Breaking away from the traditional approach of its predecessor, The Last of Us Part II takes a bold step in storytelling by providing a dual perspective in its narrative. This unique spin allows the players to experience the story from both Ellie's and Abby's points of view, lending much-needed depth to the storyline. It also highlights the subjectivity of human perception and experience as the same event unfolds differently in each character's gameplay, hence leaving the players with a broader outlook and understanding of the story.
The characters, Ellie and Abby, undergo elaborate character arcs throughout the game. They evolve tremendously; their growth is evident in their changing ideologies, decisions, and varying responses to the challenges they confront. By focusing on their character development, the game manages to convey the profound impacts of their life experiences and challenges faced in the post-apocalyptic world on their personalities.
Lastly, the game navigates through the complexities of Ellie and Abby's actions and emotions. It unearths the reasons behind their decisions, their conflicting emotions, and their struggle with their past and present. This exploration of complexity drives home the point that the characters aren't merely heroes or villains but complex individuals caught in a world where survival takes precedence over everything else.
Ellie: The Haunted Protagonist
Ellie, a nineteen-year-old survivor, sets out on a journey of retribution when a tragedy befalls her peaceful life in the post-apocalyptic world. Her character undergoes layers of transformation, moving from a carefree teenager to a revenge-driven individual. Her decisions, guided by pain and rage, paint a heart-wrenching picture of human vulnerability and resilience.
Abby: The Conflicted Antagonist
Abby's character challenges conventional villain templates. She evolves from a character initially perceived as ruthless to revealing her humane side shadowed by her past. Abby's quest for redemption, contrasted with her violent actions, incites conflicting emotions among players, thus enriching the narrative.
Secondary Characters: Their Impact and Role
Several secondary characters play crucial roles across the game, aiding and influencing the main characters' journey in profound ways. Key characters include Joel, Dina, and Isaac.
Joel: The Lingering Spirit
While the game starts with Joel's brutal end, his influence persists throughout the narrative. His actions in the prequel lay the groundwork for the events in The Last of Us Part II, leaving Ellie and Abby to suffer the repercussions of his choices.
Dina: Ellie's Anchor
Dina, a key ally and love interest of Ellie, provides solace and helps Ellie retain her humanity. Her character demonstrates the power of love and friendship in extreme circumstances and the consequences of their loss.
Isaac: The Cold Strategist
Isaac, the strategic leader of the Washington Liberation Front, plays an essential role in the war between factions. He illustrates the dehumanizing effects of long-term conflict and the cost of dogmatism.
Plot Analysis: The Multifaceted Storyline
The Last of Us Part II weaves an intricate tale revolving around both its hero and villain, probing profound undertones of existence, vengeance, affection, and atonement.
Survival and Revenge
The gaming narrative portrays the brutal truths of a world that has undergone an apocalypse, wherein the battle for survival is an unending challenge. Revenge emerges as a driving force, coloring the decisions and actions of the main characters while underlining the damaging effects of this dangerous pursuit.
Love and Redemption
Balancing the bleak aspects of the storyline are themes of love and redemption. These themes explore how love can act as a stabilizing influence and how redemption might be possible even in the most despairing circumstances. They add emotional depth and intricacy to the narrative.
Controversial Storytelling and Player Interpretations
The Last of Us Part II has incited polarizing reactions among players due to its unconventional storytelling and character development. Contemporary thematic exploration and unexpected character arcs have led to various interpretations and theories among the fanbase.
Conclusion: Assessing the Narrative Impact
The Last of Us Part II offers a highly immersive experience through compelling characters and a thought-provoking storyline. Its characters challenge traditional boundaries, growing and evolving through personal losses and wins. The multifaceted narrative blends elements of survival, revenge, love, and redemption, invoking strong emotions and prompting players to delve deeper. Despite its polarizing reception, the game ultimately solidifies its standing as a profound exploration of human nature in extreme circumstances.
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-08-11
Ethan Blackstone
2024-08-11
-
![Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO]() News
Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO
Despite its lackluster reception, Battlefield 2042 hasn't deterred EA from its commitment to the franchise. The company is channeling considerable resources into the next installment, with several of its studios collaborating on the project. Although specific details remain sparse, EA's CEO Andrew Wilson recently shared insights about what lies ahead for the Battlefield series.
During a quarterly earnings call, Wilson characterized the forthcoming game as one of EA’s most ambitious endeavors to date. He expressed confidence in the development team, stating that their goal is to create an immersive Battlefield experience that excites the player community. The enthusiasm around the project, according to Wilson, signals strong support for the team’s direction.
An array of studios is contributing to the Battlefield effort. Lead developer DICE is at the forefront, while Criterion Games is set to handle the single-player campaign after the dissolution of Ridgeline Games earlier this year. Additionally, the acclaimed Motive Studio is assembling a new team to support the game's development.
According to earlier reports, the upcoming Battlefield title is on track for release in October 2025. Meanwhile, Ripple Effect Studios is believed to be crafting a separate free-to-play battle royale experience within the franchise, further expanding its offerings.
News
Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO
Despite its lackluster reception, Battlefield 2042 hasn't deterred EA from its commitment to the franchise. The company is channeling considerable resources into the next installment, with several of its studios collaborating on the project. Although specific details remain sparse, EA's CEO Andrew Wilson recently shared insights about what lies ahead for the Battlefield series.
During a quarterly earnings call, Wilson characterized the forthcoming game as one of EA’s most ambitious endeavors to date. He expressed confidence in the development team, stating that their goal is to create an immersive Battlefield experience that excites the player community. The enthusiasm around the project, according to Wilson, signals strong support for the team’s direction.
An array of studios is contributing to the Battlefield effort. Lead developer DICE is at the forefront, while Criterion Games is set to handle the single-player campaign after the dissolution of Ridgeline Games earlier this year. Additionally, the acclaimed Motive Studio is assembling a new team to support the game's development.
According to earlier reports, the upcoming Battlefield title is on track for release in October 2025. Meanwhile, Ripple Effect Studios is believed to be crafting a separate free-to-play battle royale experience within the franchise, further expanding its offerings.
![Ava Reynolds Ava Reynolds]() Ava Reynolds
2024-08-07
Ava Reynolds
2024-08-07
-
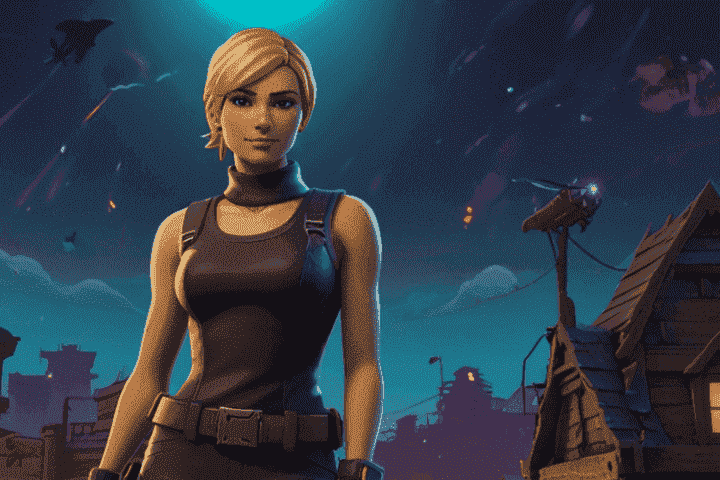
![Fortnite: Building Techniques for Winning More Battles Fortnite: Building Techniques for Winning More Battles]() Tips & Guides
Fortnite: Building Techniques for Winning More Battles
Fortnite Battle Royale stands out from the crowd of online multiplayer games due to its distinctive building mechanics. This wildly popular game has captivated players worldwide, offering a unique blend of shooter and builder gameplay styles. Instead of simply relying on finding the perfect weapon to take out your opponents, Fortnite adds an extra layer of strategy by enabling players to construct various structures in the gaming landscape.
Building in Fortnite serves several tactical purposes: it can provide defenses to shield you from enemy attacks, form offensive platforms from which to stage your assaults, and aid in quick movements across the map. A simple wooden wall or towering fortress can mean the difference between victory and defeat. This game element goes far beyond mere survival; It takes on a crucial part in orchestrating your comprehensive combat tactics.
At first glance, the art of building in Fortnite might seem straightforward - you just need to select the right materials and start constructing, right? However, the intricacies lie in the execution. Effective building requires a keen sense of timing, a high degree of precision, and, most importantly, strategic thinking. The layout structure, the choice of materials, and even the decision of when and where to build - these are all factors that contribute to your overall gameplay.
By refining your building techniques, you can significantly improve your survival chances in the game. A player skilled in building can quickly create structures to outmaneuver opponents, gaining the upper hand in firefights and increasing their odds of emerging victorious. Mastering diverse building strategies allows you to adapt to any situation you encounter, turning potential threats into opportunities for victory.
In the proceeding paragraphs, we shall delve into six advanced building methods to improve your gameplay. By implementing these techniques, you can elevate your Fortnite skills to the next level, ensuring that you always have a few tricks up your sleeve for your next battle.
1. Quick Fort Building
The art of building in Fortnite commences with understanding the nuts and bolts of constructing a simple 1x1 fort. As a straightforward and basic building technique, quick fort building serves as your entry point into the realm of Fortnite construction strategies. Its objective is to provide players with a swift and easy solution to defend against enemy fire and gain an advantageous position in battle.
As the name suggests, the 1x1 fort is a compact structure, serving as a protective shell against enemy attacks. The beauty of this quick fort lies in its simplicity and efficiency. When you find yourself in the thick of battle with bullets flying around, this structure can provide you with the much-needed protection to shield yourself from direct hits.
The 1x1 fort is not just about defense; it provides an excellent vantage point to observe the battlefield and spot adversaries. From the safety of your fort, you can gather crucial information about the enemy's location and game plan. Your fort situates you higher than ground level, giving you an overview of the unfolding battle and the positions of your competitors.
Building a quick fort is a straightforward process but requires speed and precision. The first step is laying down four walls, forming a closed square around you. Then, inside this box, you need to add stairs. The stairs elevate you, enhancing your viewing range and offering a platform to return fire. To cap it off, do not forget to add a roof on top to secure yourself from attacks from above.
It is essential to practice this technique under low-pressure conditions. Doing so will allow you to enhance your building speed, reducing the time it takes to create a fort when you're in the heart of the battle. Your goal should be to construct the fort so swiftly that it becomes second nature. The quick fort, given its utility and ease of construction, can be your reliable ally in the unpredictable and volatile world of Fortnite.
2. Ramp Rush
Ramp rushing is an offensive building technique employed to close the gap between you and your enemy. It involves building ramp structures towards the enemy; the height advantage can help you gain better aim. However, it's crucial to reinforce your ramps with walls to prevent the enemy from shooting down your structure. Remember, building with wooden materials may be quicker but also less durable than stone or metal, so choose your materials wisely depending on the situation.
3. Double Ramping
Double ramping takes ramp rushing to the next level by adding an extra layer of protection. This implies building two ramps parallel to each other, reinforced by walls for better defense. This strategy allows you to gain both height and pressure on your opponents while minimizing your own risks. Double ramping can consume more materials compared to a single ramp rush, but the additional safety it provides is often worth the expenditure.
4. Waterfalling
Waterfalling is a crucial skill when you need to descend from great heights quickly and safely. This technique involves building ramps or floors beneath you as you fall, mitigating fall damage. Beginners may struggle with this technique as it requires precise timing and fast reactions. However, mastering waterfalling can be a literal lifesaver in many Fortnite engagements.
5. Pyramid and Cone Jumps
Pyramid or cone jumps provide a sneaky way of outsmarting and outrunning your opponents by confusing them with unexpected moves. A cone jump involves creating a pyramid structure over your ramp and then jumping on the pyramid, hence breaking the linear direction of your ramp rush. This tactic is extremely useful when you want to shift direction quickly without sacrificing safety or height advantage.
6. High Ground Retake
High Ground Retake is the art of stealing the high-ground advantage from your opponent through strategic building. This technique involves several steps, including building ramps above you, boxing yourself in, and constructing a staircase to ascend further. This technique may seem complex at first, but mastering it can provide a significant advantage, especially in late-game build fights.
Conclusion
Advanced building techniques in Fortnite Battle Royale are game-changing skills that separate average players from pros. Implementing these methods into your gaming strategy can elevate your attack and defense skills. This will always keep you one pace ahead of your competitors. Bear in mind that to excel as a professional architect in Fortnite, continuous practice, endurance, and tactical cognition are essential. Enjoy assembling and conquering!
Tips & Guides
Fortnite: Building Techniques for Winning More Battles
Fortnite Battle Royale stands out from the crowd of online multiplayer games due to its distinctive building mechanics. This wildly popular game has captivated players worldwide, offering a unique blend of shooter and builder gameplay styles. Instead of simply relying on finding the perfect weapon to take out your opponents, Fortnite adds an extra layer of strategy by enabling players to construct various structures in the gaming landscape.
Building in Fortnite serves several tactical purposes: it can provide defenses to shield you from enemy attacks, form offensive platforms from which to stage your assaults, and aid in quick movements across the map. A simple wooden wall or towering fortress can mean the difference between victory and defeat. This game element goes far beyond mere survival; It takes on a crucial part in orchestrating your comprehensive combat tactics.
At first glance, the art of building in Fortnite might seem straightforward - you just need to select the right materials and start constructing, right? However, the intricacies lie in the execution. Effective building requires a keen sense of timing, a high degree of precision, and, most importantly, strategic thinking. The layout structure, the choice of materials, and even the decision of when and where to build - these are all factors that contribute to your overall gameplay.
By refining your building techniques, you can significantly improve your survival chances in the game. A player skilled in building can quickly create structures to outmaneuver opponents, gaining the upper hand in firefights and increasing their odds of emerging victorious. Mastering diverse building strategies allows you to adapt to any situation you encounter, turning potential threats into opportunities for victory.
In the proceeding paragraphs, we shall delve into six advanced building methods to improve your gameplay. By implementing these techniques, you can elevate your Fortnite skills to the next level, ensuring that you always have a few tricks up your sleeve for your next battle.
1. Quick Fort Building
The art of building in Fortnite commences with understanding the nuts and bolts of constructing a simple 1x1 fort. As a straightforward and basic building technique, quick fort building serves as your entry point into the realm of Fortnite construction strategies. Its objective is to provide players with a swift and easy solution to defend against enemy fire and gain an advantageous position in battle.
As the name suggests, the 1x1 fort is a compact structure, serving as a protective shell against enemy attacks. The beauty of this quick fort lies in its simplicity and efficiency. When you find yourself in the thick of battle with bullets flying around, this structure can provide you with the much-needed protection to shield yourself from direct hits.
The 1x1 fort is not just about defense; it provides an excellent vantage point to observe the battlefield and spot adversaries. From the safety of your fort, you can gather crucial information about the enemy's location and game plan. Your fort situates you higher than ground level, giving you an overview of the unfolding battle and the positions of your competitors.
Building a quick fort is a straightforward process but requires speed and precision. The first step is laying down four walls, forming a closed square around you. Then, inside this box, you need to add stairs. The stairs elevate you, enhancing your viewing range and offering a platform to return fire. To cap it off, do not forget to add a roof on top to secure yourself from attacks from above.
It is essential to practice this technique under low-pressure conditions. Doing so will allow you to enhance your building speed, reducing the time it takes to create a fort when you're in the heart of the battle. Your goal should be to construct the fort so swiftly that it becomes second nature. The quick fort, given its utility and ease of construction, can be your reliable ally in the unpredictable and volatile world of Fortnite.
2. Ramp Rush
Ramp rushing is an offensive building technique employed to close the gap between you and your enemy. It involves building ramp structures towards the enemy; the height advantage can help you gain better aim. However, it's crucial to reinforce your ramps with walls to prevent the enemy from shooting down your structure. Remember, building with wooden materials may be quicker but also less durable than stone or metal, so choose your materials wisely depending on the situation.
3. Double Ramping
Double ramping takes ramp rushing to the next level by adding an extra layer of protection. This implies building two ramps parallel to each other, reinforced by walls for better defense. This strategy allows you to gain both height and pressure on your opponents while minimizing your own risks. Double ramping can consume more materials compared to a single ramp rush, but the additional safety it provides is often worth the expenditure.
4. Waterfalling
Waterfalling is a crucial skill when you need to descend from great heights quickly and safely. This technique involves building ramps or floors beneath you as you fall, mitigating fall damage. Beginners may struggle with this technique as it requires precise timing and fast reactions. However, mastering waterfalling can be a literal lifesaver in many Fortnite engagements.
5. Pyramid and Cone Jumps
Pyramid or cone jumps provide a sneaky way of outsmarting and outrunning your opponents by confusing them with unexpected moves. A cone jump involves creating a pyramid structure over your ramp and then jumping on the pyramid, hence breaking the linear direction of your ramp rush. This tactic is extremely useful when you want to shift direction quickly without sacrificing safety or height advantage.
6. High Ground Retake
High Ground Retake is the art of stealing the high-ground advantage from your opponent through strategic building. This technique involves several steps, including building ramps above you, boxing yourself in, and constructing a staircase to ascend further. This technique may seem complex at first, but mastering it can provide a significant advantage, especially in late-game build fights.
Conclusion
Advanced building techniques in Fortnite Battle Royale are game-changing skills that separate average players from pros. Implementing these methods into your gaming strategy can elevate your attack and defense skills. This will always keep you one pace ahead of your competitors. Bear in mind that to excel as a professional architect in Fortnite, continuous practice, endurance, and tactical cognition are essential. Enjoy assembling and conquering!
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-08-06
Ethan Blackstone
2024-08-06
-
![Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges” Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges”]() News
Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges”
Marvel Rivals is shaping up to be an exciting entry into the hero shooter genre, thanks in part to its well-established branding and the unique capabilities it brings to the table. The game boasts an impressive lineup of playable characters, each equipped with diverse moves and skills. However, this variety has presented some hurdles for the development team at NetEase Games.
In a recent discussion with GamingBolt, the developers revealed that balancing the experience while ensuring every character feels distinct has been a significant challenge—especially concerning melee-heavy heroes like Thor, Spider-Man, and the Incredible Hulk. If not properly handled, the dynamic of close-quarters combat could lead to chaotic gameplay that might detract from the enjoyment.
The developers articulated their struggle, emphasizing that crafting a diverse set of melee combatants was a top priority. They noted that mishandling these characters could result in battles lacking substance, ultimately compromising the gaming experience.
Yet, the unique abilities of the Marvel roster also presented exciting opportunities for the developers. They explained how the Hulk's impressive leaping ability was designed to impact aerial foes, adding an interesting layer to his play style. Venom's symbiotic traits were expanded to allow for mid-range attacks, while Spider-Man’s agility enables fluid transitions between melee and ranged encounters.
By focusing on each hero's strengths, the team aims to create a captivating gameplay experience that highlights each character’s unique mechanics.
Marvel Rivals is currently under development for PS5, Xbox Series X/S, and PC, with no confirmed release date available at this time.
News
Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges”
Marvel Rivals is shaping up to be an exciting entry into the hero shooter genre, thanks in part to its well-established branding and the unique capabilities it brings to the table. The game boasts an impressive lineup of playable characters, each equipped with diverse moves and skills. However, this variety has presented some hurdles for the development team at NetEase Games.
In a recent discussion with GamingBolt, the developers revealed that balancing the experience while ensuring every character feels distinct has been a significant challenge—especially concerning melee-heavy heroes like Thor, Spider-Man, and the Incredible Hulk. If not properly handled, the dynamic of close-quarters combat could lead to chaotic gameplay that might detract from the enjoyment.
The developers articulated their struggle, emphasizing that crafting a diverse set of melee combatants was a top priority. They noted that mishandling these characters could result in battles lacking substance, ultimately compromising the gaming experience.
Yet, the unique abilities of the Marvel roster also presented exciting opportunities for the developers. They explained how the Hulk's impressive leaping ability was designed to impact aerial foes, adding an interesting layer to his play style. Venom's symbiotic traits were expanded to allow for mid-range attacks, while Spider-Man’s agility enables fluid transitions between melee and ranged encounters.
By focusing on each hero's strengths, the team aims to create a captivating gameplay experience that highlights each character’s unique mechanics.
Marvel Rivals is currently under development for PS5, Xbox Series X/S, and PC, with no confirmed release date available at this time.
![Latanskiy Nick Latanskiy Nick]() Latanskiy Nick
2024-08-05
Latanskiy Nick
2024-08-05
-
![Character Guide: Exploring the Champions of League of Legends Character Guide: Exploring the Champions of League of Legends]() Tips & Guides
Character Guide: Exploring the Champions of League of Legends
The world of gaming is brimming with numerous enthralling experiences, but few can hold a candle to the captivating scenarios laid out in the landscape of League of Legends (LoL). Its widespread acceptance among gaming enthusiasts worldwide and the electrifying gameplay that keeps players on the edge of their seats are largely attributed to its diverse lineup of champions.
From their distinctive abilities to their individual strategic significance, each champion in LoL adds a new dimension to the gameplay. They each possess unique abilities that can be wielded in the game, laying the foundation for an endlessly versatile variety of dynamics in each battle. With each of them fulfilling unique roles that they're tailored for, champions bring specific tactics and strategies to the table, making the gameplay ever-engrossing.
As you get accustomed to the thrilling realm of LoL, an in-depth knowledge of the champions becomes indispensable. This comprehensive guide is designed to provide you with a deeper understanding of the champions, shedding light on their unique abilities, roles, and tactical uses. Furthermore, we'll delve into the various categories champions fall into and the strategic value each holds in the game.
But awareness cannot replace skill. The actual challenge lies in mastering these champions. Every champion requires a different approach and strategy, and understanding alone won't quite cut it. So, we intend to provide tips on mastering them as well, ensuring you can take full advantage of the potential each champion holds.
Understanding the Unique Abilities of Champions
In the exhilarating world of League of Legends, each champion brings a unique personality to the battlefield. And the key factor defining this personality is the distinct set of abilities that each champion possesses. It's these special abilities that carve out the champion's playstyle, laying the groundwork for their approach and tactics when venturing into the battlefield.
The abilities of champions demonstrate a diverse range, each serving different purposes in the match. They are typically categorized as 'Passive,' 'Q,' 'W,' 'E,' and 'Ultimate.' Understanding these categories is critical to comprehending a champion's capabilities and knowing how to strategize effectively during the game.
The 'Passive' ability is a champion's fundamental attribute, which is inherently enabled during the game. It does not require any command to activate and remains operational, emphasizing the inherent nature or the core strength of the champion throughout.
The 'Q,' 'W,' and 'E' signify the basic abilities that every champion possesses. These abilities play a significant role during the fiercely fought battles. Choose the right moments to deploy and upgrade these abilities, for they hold the potential to shift the balance of the game. The upgrade of these abilities happens during the course of the match, progressively increasing the champion's power and tactics.
Above all, we have the 'Ultimate' ability - the ace up the champion's sleeve. This ability is the champion's strongest asset and, thus, is available only after reaching a particular level. Unleashing the Ultimate ability can turn the tide of the match, making it a valuable weapon to wield at the right moment.
Roles of Champions in Gameplay
While each champion in League of Legends brings unique abilities to the table, they are also defined by the roles they play within the gaming environment. These roles, distinguished by a versatile range of objectives and skills, are crucial to understanding and utilizing the champions to their fullest potential. The primary roles we encounter within the game are 'Attack Damage Carry (ADC),' 'Support,' 'Mid,' 'Top,' and 'Jungle.'
The ADC, or 'Attack Damage Carry,' embodies a powerful figure in the gaming field. Often paired with the Support, their task is to deal notable damage, especially as the game reaches its later stages. Their power grows gradually through the game, and they are the cornerstone of the team's offensive strategies when they reach their peak power level at the end of the game.
The 'Support' champions, as the name aptly suggests, are the team's backbone. Their primary objective is to assist the team in a multitude of ways, but often, their prime responsibility lies in safeguarding the ADC. They contain and mitigate threats to the ADC, enabling them to wreak havoc upon opposing teams unhindered.
'Mid' champions take charge of the mid-lane, a position characterized by independent gameplay. They typically involve champions capable of handling themselves solo, holding the lane steady. The mid-champions can often shift the dynamics of the game through their individual performance in the mid-lane.
'Top' champions, akin to the stalwart defenders in a team, operate largely in isolation from the team. The characteristic feature of their gameplay is their gritty resilience and the ability to soak up damage. Their hardiness allows them to withstand substantial onslaughts, making them formidable opponents in their own right.
Last but hardly least, 'Jungle' champions, much like wildcards in a set, operate without being tied down to a particular lane. They wander the areas between lanes, aptly known as the "jungle," rendering assistance where needed. Their role is fluid and often involves counteracting enemy strategies, providing Support, and seizing opportunities across the game map.
Classification of Champions
Further, champions are classified based on their specific strengths and playing style. The classifications are 'Tank,' 'Mage,' 'Fighter,' 'Assassin,' 'Marksman,' and 'Support.' Tank champions have high durability and crowd control abilities, mages are magic damage dealers, and fighters are versatile champions who can both deal and take damage. Assassins specialize in damaging specific targets, marksman champions deal consistent damage from a range, and support champions have abilities to protect and enhance their team.
Getting to Grips with Strategizing
Understanding the facets of champions is not enough; knowing how to use them strategically is key to mastering League of Legends. Each champion is unique, and mastering them requires understanding their strengths and weaknesses. Players have to customize their gameplay according to the champion they use and adapt to their chosen champion's abilities. A strategic approach to each champion's abilities will significantly enhance your game.
Tips to Master Champions
Mastering a champion requires understanding their abilities and also their roles in the game. Start with understanding the champion's abilities and how you can use them during gameplay. Use tutorials and guides to understand how to play the champion efficiently. Practice using the abilities of the champion in various situations during the game. Try to learn one champion at a time and understand all loopholes and gameplay strategies with that champion before moving to the next.
Final Words
League of Legends champions, with their diverse abilities and roles, add significant strategic depth to the gameplay. Regardless if you are an experienced gamer wanting to boost your skills or a beginner eager to dip your toes, grasping the complexities and variety of these champions will prove valuable. Remember, the key to mastering any champion is through understanding, strategic gameplay, and practice. So, dive into the captivating world of LoL and embrace the exciting diversity offered by its champions!
Tips & Guides
Character Guide: Exploring the Champions of League of Legends
The world of gaming is brimming with numerous enthralling experiences, but few can hold a candle to the captivating scenarios laid out in the landscape of League of Legends (LoL). Its widespread acceptance among gaming enthusiasts worldwide and the electrifying gameplay that keeps players on the edge of their seats are largely attributed to its diverse lineup of champions.
From their distinctive abilities to their individual strategic significance, each champion in LoL adds a new dimension to the gameplay. They each possess unique abilities that can be wielded in the game, laying the foundation for an endlessly versatile variety of dynamics in each battle. With each of them fulfilling unique roles that they're tailored for, champions bring specific tactics and strategies to the table, making the gameplay ever-engrossing.
As you get accustomed to the thrilling realm of LoL, an in-depth knowledge of the champions becomes indispensable. This comprehensive guide is designed to provide you with a deeper understanding of the champions, shedding light on their unique abilities, roles, and tactical uses. Furthermore, we'll delve into the various categories champions fall into and the strategic value each holds in the game.
But awareness cannot replace skill. The actual challenge lies in mastering these champions. Every champion requires a different approach and strategy, and understanding alone won't quite cut it. So, we intend to provide tips on mastering them as well, ensuring you can take full advantage of the potential each champion holds.
Understanding the Unique Abilities of Champions
In the exhilarating world of League of Legends, each champion brings a unique personality to the battlefield. And the key factor defining this personality is the distinct set of abilities that each champion possesses. It's these special abilities that carve out the champion's playstyle, laying the groundwork for their approach and tactics when venturing into the battlefield.
The abilities of champions demonstrate a diverse range, each serving different purposes in the match. They are typically categorized as 'Passive,' 'Q,' 'W,' 'E,' and 'Ultimate.' Understanding these categories is critical to comprehending a champion's capabilities and knowing how to strategize effectively during the game.
The 'Passive' ability is a champion's fundamental attribute, which is inherently enabled during the game. It does not require any command to activate and remains operational, emphasizing the inherent nature or the core strength of the champion throughout.
The 'Q,' 'W,' and 'E' signify the basic abilities that every champion possesses. These abilities play a significant role during the fiercely fought battles. Choose the right moments to deploy and upgrade these abilities, for they hold the potential to shift the balance of the game. The upgrade of these abilities happens during the course of the match, progressively increasing the champion's power and tactics.
Above all, we have the 'Ultimate' ability - the ace up the champion's sleeve. This ability is the champion's strongest asset and, thus, is available only after reaching a particular level. Unleashing the Ultimate ability can turn the tide of the match, making it a valuable weapon to wield at the right moment.
Roles of Champions in Gameplay
While each champion in League of Legends brings unique abilities to the table, they are also defined by the roles they play within the gaming environment. These roles, distinguished by a versatile range of objectives and skills, are crucial to understanding and utilizing the champions to their fullest potential. The primary roles we encounter within the game are 'Attack Damage Carry (ADC),' 'Support,' 'Mid,' 'Top,' and 'Jungle.'
The ADC, or 'Attack Damage Carry,' embodies a powerful figure in the gaming field. Often paired with the Support, their task is to deal notable damage, especially as the game reaches its later stages. Their power grows gradually through the game, and they are the cornerstone of the team's offensive strategies when they reach their peak power level at the end of the game.
The 'Support' champions, as the name aptly suggests, are the team's backbone. Their primary objective is to assist the team in a multitude of ways, but often, their prime responsibility lies in safeguarding the ADC. They contain and mitigate threats to the ADC, enabling them to wreak havoc upon opposing teams unhindered.
'Mid' champions take charge of the mid-lane, a position characterized by independent gameplay. They typically involve champions capable of handling themselves solo, holding the lane steady. The mid-champions can often shift the dynamics of the game through their individual performance in the mid-lane.
'Top' champions, akin to the stalwart defenders in a team, operate largely in isolation from the team. The characteristic feature of their gameplay is their gritty resilience and the ability to soak up damage. Their hardiness allows them to withstand substantial onslaughts, making them formidable opponents in their own right.
Last but hardly least, 'Jungle' champions, much like wildcards in a set, operate without being tied down to a particular lane. They wander the areas between lanes, aptly known as the "jungle," rendering assistance where needed. Their role is fluid and often involves counteracting enemy strategies, providing Support, and seizing opportunities across the game map.
Classification of Champions
Further, champions are classified based on their specific strengths and playing style. The classifications are 'Tank,' 'Mage,' 'Fighter,' 'Assassin,' 'Marksman,' and 'Support.' Tank champions have high durability and crowd control abilities, mages are magic damage dealers, and fighters are versatile champions who can both deal and take damage. Assassins specialize in damaging specific targets, marksman champions deal consistent damage from a range, and support champions have abilities to protect and enhance their team.
Getting to Grips with Strategizing
Understanding the facets of champions is not enough; knowing how to use them strategically is key to mastering League of Legends. Each champion is unique, and mastering them requires understanding their strengths and weaknesses. Players have to customize their gameplay according to the champion they use and adapt to their chosen champion's abilities. A strategic approach to each champion's abilities will significantly enhance your game.
Tips to Master Champions
Mastering a champion requires understanding their abilities and also their roles in the game. Start with understanding the champion's abilities and how you can use them during gameplay. Use tutorials and guides to understand how to play the champion efficiently. Practice using the abilities of the champion in various situations during the game. Try to learn one champion at a time and understand all loopholes and gameplay strategies with that champion before moving to the next.
Final Words
League of Legends champions, with their diverse abilities and roles, add significant strategic depth to the gameplay. Regardless if you are an experienced gamer wanting to boost your skills or a beginner eager to dip your toes, grasping the complexities and variety of these champions will prove valuable. Remember, the key to mastering any champion is through understanding, strategic gameplay, and practice. So, dive into the captivating world of LoL and embrace the exciting diversity offered by its champions!
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-07-23
Ethan Blackstone
2024-07-23
Latest Reviews
![Minecraft Minecraft]() arcade
Minecraft
Minecraft, a game that has transcended beyond its PC origins, has carved its niche in the mobile gaming sphere with its Pocket Edition. It's not just a game; it's a canvas for creativity, a universe of endless possibilities where imagination runs wild. This edition, though initially pared down, has evolved, bringing the essence of its PC counterpart to the small screen.
The World at Your Fingertips
At the heart of Minecraft: Pocket Edition lies a procedurally generated world, brimming with opportunities and devoid of any predefined paths or objectives. This sandbox environment is the game's playground, where players harvest resources, craft structures, and let their architectural dreams take flight. Whether it's crafting a modest shelter or a sprawling castle, the game morphs into whatever the player desires it to be.
Gameplay Dynamics and Features
Diving into the gameplay, Minecraft: Pocket Edition splits into two distinct modes, each offering a unique experience. The survival mode introduces a layer of challenge, compelling players to gather resources and maintain their health. For those who prefer a serene creative experience, there's a mode that unlocks unlimited resources, allowing for unfettered artistic expression. Recent updates have enriched the game further, introducing elements that fans of the original have come to love, including the much-anticipated crafting and mining mechanics.
The Learning Curve
Minecraft: Pocket Edition, however, is not without its hurdles. The game's open-ended nature can be bewildering, leaving newcomers adrift without a clear direction. The absence of a tutorial or a defined objective might deter the less patient players. Yet, this complexity is what makes Minecraft a treasure trove for those willing to explore its depths, with numerous online guides standing ready to illuminate the path.
Encouraging Creativity Beyond the Screen
Minecraft's influence extends beyond digital play. It acts as a bridge to real-world creativity, encouraging players to replicate their in-game creations with tangible blocks or LEGO bricks. Playing alongside children, parents have a unique opportunity to engage and foster imagination, turning gameplay into a collaborative and educational experience.
Minecraft: Pocket Edition is a testament to the power of creativity and exploration. While it challenges players with its steep learning curve, it rewards tenacity with a world that's endlessly malleable. It's more than a game; it's a journey of discovery, limited only by one's imagination.
2026-05-02
Read full review
arcade
Minecraft
Minecraft, a game that has transcended beyond its PC origins, has carved its niche in the mobile gaming sphere with its Pocket Edition. It's not just a game; it's a canvas for creativity, a universe of endless possibilities where imagination runs wild. This edition, though initially pared down, has evolved, bringing the essence of its PC counterpart to the small screen.
The World at Your Fingertips
At the heart of Minecraft: Pocket Edition lies a procedurally generated world, brimming with opportunities and devoid of any predefined paths or objectives. This sandbox environment is the game's playground, where players harvest resources, craft structures, and let their architectural dreams take flight. Whether it's crafting a modest shelter or a sprawling castle, the game morphs into whatever the player desires it to be.
Gameplay Dynamics and Features
Diving into the gameplay, Minecraft: Pocket Edition splits into two distinct modes, each offering a unique experience. The survival mode introduces a layer of challenge, compelling players to gather resources and maintain their health. For those who prefer a serene creative experience, there's a mode that unlocks unlimited resources, allowing for unfettered artistic expression. Recent updates have enriched the game further, introducing elements that fans of the original have come to love, including the much-anticipated crafting and mining mechanics.
The Learning Curve
Minecraft: Pocket Edition, however, is not without its hurdles. The game's open-ended nature can be bewildering, leaving newcomers adrift without a clear direction. The absence of a tutorial or a defined objective might deter the less patient players. Yet, this complexity is what makes Minecraft a treasure trove for those willing to explore its depths, with numerous online guides standing ready to illuminate the path.
Encouraging Creativity Beyond the Screen
Minecraft's influence extends beyond digital play. It acts as a bridge to real-world creativity, encouraging players to replicate their in-game creations with tangible blocks or LEGO bricks. Playing alongside children, parents have a unique opportunity to engage and foster imagination, turning gameplay into a collaborative and educational experience.
Minecraft: Pocket Edition is a testament to the power of creativity and exploration. While it challenges players with its steep learning curve, it rewards tenacity with a world that's endlessly malleable. It's more than a game; it's a journey of discovery, limited only by one's imagination.
2026-05-02
Read full review
![Cookie Jam Cookie Jam]() puzzle
Cookie Jam
In an era where mobile games promise to offer an escape from reality, few manage to deliver an experience as engaging and delightful as Cookie Jam by Jam City. This gem stands out in the crowded field of puzzle games, offering a fresh twist on the classic Tetris style of play. Let's delve into the delicious world of Cookie Jam, examining its gameplay, graphics, features, and more, to understand why it's become such a beloved pastime for many.
A Puzzle Game With a Delicious Twist
Cookie Jam elevates the familiar "match three" puzzle format by incorporating unique challenges and objectives that keep players on their toes. Unlike its predecessors, the game quickly moves beyond simple matching tasks. Players find themselves breaking waffle cones, assembling cookie sandwiches, and racing against gingerbread men—all in a bid to prevent them from reaching the top of the screen. With each new level, the game introduces fresh puzzles, ensuring that the gameplay never becomes monotonous.
Strategy Meets Sweetness
As players progress through Cookie Jam, they'll discover that success requires more than just quick fingers; it demands strategic thinking. The game offers a variety of power-ups, which can be crucial for conquering particularly tricky levels. However, these power-ups aren't unlimited, prompting players to use them judiciously, especially before tackling the levels flagged as "Hard Level." This strategic component enhances the complexity of the game, making triumphs significantly more rewarding.
A Fair Play in a Free Game
One of the most commendable aspects of Cookie Jam is its approach to in-app purchases. While players have the option to buy advantages, the game is designed in such a way that spending money isn't necessary for progress. Lives do deplete, but they regenerate after a short twenty-minute wait, offering a balanced and fair gameplay experience without hidden costs.
Engaging Extras and Adorable Assistance
Cookie Jam keeps the excitement alive with daily challenges that offer rewards and a chance to climb the leaderboard. Additionally, players can choose a pet to assist them in their pastry adventures. These furry friends not only add a layer of cuteness to the game but also provide tangible help by clearing cookies from the board.
A Recipe for Fun
After spending considerable time with Cookie Jam, it's hard to pinpoint any significant faults. The game combines engaging puzzles, strategic gameplay, and a fair approach to in-app purchases to create an experience that's as sweet as the pastries it features. Whether you're looking for a way to pass the time or a new challenge to master, Cookie Jam is a delightful choice that's sure to satisfy your gaming cravings.
2026-05-02
Read full review
puzzle
Cookie Jam
In an era where mobile games promise to offer an escape from reality, few manage to deliver an experience as engaging and delightful as Cookie Jam by Jam City. This gem stands out in the crowded field of puzzle games, offering a fresh twist on the classic Tetris style of play. Let's delve into the delicious world of Cookie Jam, examining its gameplay, graphics, features, and more, to understand why it's become such a beloved pastime for many.
A Puzzle Game With a Delicious Twist
Cookie Jam elevates the familiar "match three" puzzle format by incorporating unique challenges and objectives that keep players on their toes. Unlike its predecessors, the game quickly moves beyond simple matching tasks. Players find themselves breaking waffle cones, assembling cookie sandwiches, and racing against gingerbread men—all in a bid to prevent them from reaching the top of the screen. With each new level, the game introduces fresh puzzles, ensuring that the gameplay never becomes monotonous.
Strategy Meets Sweetness
As players progress through Cookie Jam, they'll discover that success requires more than just quick fingers; it demands strategic thinking. The game offers a variety of power-ups, which can be crucial for conquering particularly tricky levels. However, these power-ups aren't unlimited, prompting players to use them judiciously, especially before tackling the levels flagged as "Hard Level." This strategic component enhances the complexity of the game, making triumphs significantly more rewarding.
A Fair Play in a Free Game
One of the most commendable aspects of Cookie Jam is its approach to in-app purchases. While players have the option to buy advantages, the game is designed in such a way that spending money isn't necessary for progress. Lives do deplete, but they regenerate after a short twenty-minute wait, offering a balanced and fair gameplay experience without hidden costs.
Engaging Extras and Adorable Assistance
Cookie Jam keeps the excitement alive with daily challenges that offer rewards and a chance to climb the leaderboard. Additionally, players can choose a pet to assist them in their pastry adventures. These furry friends not only add a layer of cuteness to the game but also provide tangible help by clearing cookies from the board.
A Recipe for Fun
After spending considerable time with Cookie Jam, it's hard to pinpoint any significant faults. The game combines engaging puzzles, strategic gameplay, and a fair approach to in-app purchases to create an experience that's as sweet as the pastries it features. Whether you're looking for a way to pass the time or a new challenge to master, Cookie Jam is a delightful choice that's sure to satisfy your gaming cravings.
2026-05-02
Read full review
![Temple Run Temple Run]() arcade
Temple Run
Temple Run has been described as "the most popular, and highest-grossing game in the history of mobile gaming." It is a mobile game that is played on iOS and Android devices. Though the game was initially released in 2011, it has been made available for Windows Phone and Windows 8. Temple Run is the newest game from Disney's gaming studio, Imangi Studios. The game is an endless runner, meaning that the player has an infinite number of lives and the game is not over until the player crashes into an obstacle or falls off the path. Temple Run is available on iOS and Android.
Gameplay
The gameplay consists of running automatically forward. The player runs by swiping or tilting his device to turn left or right, and uses a virtual joystick to jump, slide under obstacles, and perform other moves to avoid obstacles and to collect coins. The player is able to collect power-ups during gameplay. In Temple Run, the player starts with three lives and has to keep running the length of the course, which changes depending on the level. The player has to collect coins and avoid obstacles such as trees and cacti, which slow the player down. The player can also tap on the screen to jump over anything in the way. The player can also collect power-ups that make running faster and increase the size of the player's character.
Graphics
The graphics are cartoon-like and consist of a brown-orange color scheme. The graphics are colorful and bright. They are cartoony and have a very Disney-esque feel to them.
Pros
It's fun
It doesn't require Internet access
It's colorful and cartoony
It's easy to restart the game if you die
It's addictive
It doesn't require a lot of attention
It's free
Cons
It's only available for iOS and Android
It's not very user-friendly
2026-05-02
Read full review
arcade
Temple Run
Temple Run has been described as "the most popular, and highest-grossing game in the history of mobile gaming." It is a mobile game that is played on iOS and Android devices. Though the game was initially released in 2011, it has been made available for Windows Phone and Windows 8. Temple Run is the newest game from Disney's gaming studio, Imangi Studios. The game is an endless runner, meaning that the player has an infinite number of lives and the game is not over until the player crashes into an obstacle or falls off the path. Temple Run is available on iOS and Android.
Gameplay
The gameplay consists of running automatically forward. The player runs by swiping or tilting his device to turn left or right, and uses a virtual joystick to jump, slide under obstacles, and perform other moves to avoid obstacles and to collect coins. The player is able to collect power-ups during gameplay. In Temple Run, the player starts with three lives and has to keep running the length of the course, which changes depending on the level. The player has to collect coins and avoid obstacles such as trees and cacti, which slow the player down. The player can also tap on the screen to jump over anything in the way. The player can also collect power-ups that make running faster and increase the size of the player's character.
Graphics
The graphics are cartoon-like and consist of a brown-orange color scheme. The graphics are colorful and bright. They are cartoony and have a very Disney-esque feel to them.
Pros
It's fun
It doesn't require Internet access
It's colorful and cartoony
It's easy to restart the game if you die
It's addictive
It doesn't require a lot of attention
It's free
Cons
It's only available for iOS and Android
It's not very user-friendly
2026-05-02
Read full review
![Call of Duty®: Warzone™ 2.0 Call of Duty®: Warzone™ 2.0]() action
Call of Duty®: Warzone™ 2.0
In a saturated market of battle royale games, each aiming to attract gamers with unique features and immersive experiences, Activision's latest release, Call of Duty®: Warzone™ 2.0, aims to redefine the genre. With the original Warzone setting a significant benchmark in the competitive gaming arena, the sequel promises to build on its predecessor's foundation. Warzone 2.0 is not just a mere update but a complete overhaul designed to captivate both old fans and new recruits. The latest installment of the Call of Duty® series invites players into a well-crafted environment that requires tactical thinking, proficiency, and flexibility to navigate its constantly changing combat landscape.
Warzone 2.0: A Mixed Bag of Innovation and Frustration
Warzone 2.0's ambitions are as vast as its new map, Al Mazrah, boasting enhanced graphics, improved audio, and a multitude of gameplay tweaks that aim to escalate the battle royale experience. The integration of AI combatants and Strongholds introduces a fresh dynamic to the loot progression, testing players' resolve against challenging adversaries. The addition of vehicular combat and the strategic value of waterways add layers of complexity to navigation and skirmishes. However, the path to perfection is marred by technical shortcomings. Users have reported issues with the game's stability, including stuttering during critical moments of play, which can disrupt the high-stakes action Warzone is known for. Moreover, the user interface has been a point of contention, with many players finding inventory management clunky and unintuitive and the minimap difficult to decipher amidst the heat of battle.
Community Verdict: Warzone 2.0's Rocky Start and Promising Future
Despite its ambitious overhaul and introduction of engrossing new features, Call of Duty®: Warzone™ 2.0 has been met with a mix of admiration and critique. The community has been vocal about their experiences, praising the game's direction in offering a more intense and immersive combat experience while simultaneously pointing out the technical hiccups that hinder gameplay. These issues, ranging from performance dips to interface complexities, have not gone unnoticed by the developers, who are seemingly committed to ironing out these kinks as the game progresses. The general consensus among players is that Warzone 2.0, with its expansive and dynamic map of Al Mazrah, has laid the groundwork for what could be the most exhilarating battle royale experience to date. As patches and updates continue to refine the experience, there is a palpable sense of optimism that Warzone 2.0 will overcome its initial troubles to emerge as a flagship title in the genre.
2026-05-02
Read full review
action
Call of Duty®: Warzone™ 2.0
In a saturated market of battle royale games, each aiming to attract gamers with unique features and immersive experiences, Activision's latest release, Call of Duty®: Warzone™ 2.0, aims to redefine the genre. With the original Warzone setting a significant benchmark in the competitive gaming arena, the sequel promises to build on its predecessor's foundation. Warzone 2.0 is not just a mere update but a complete overhaul designed to captivate both old fans and new recruits. The latest installment of the Call of Duty® series invites players into a well-crafted environment that requires tactical thinking, proficiency, and flexibility to navigate its constantly changing combat landscape.
Warzone 2.0: A Mixed Bag of Innovation and Frustration
Warzone 2.0's ambitions are as vast as its new map, Al Mazrah, boasting enhanced graphics, improved audio, and a multitude of gameplay tweaks that aim to escalate the battle royale experience. The integration of AI combatants and Strongholds introduces a fresh dynamic to the loot progression, testing players' resolve against challenging adversaries. The addition of vehicular combat and the strategic value of waterways add layers of complexity to navigation and skirmishes. However, the path to perfection is marred by technical shortcomings. Users have reported issues with the game's stability, including stuttering during critical moments of play, which can disrupt the high-stakes action Warzone is known for. Moreover, the user interface has been a point of contention, with many players finding inventory management clunky and unintuitive and the minimap difficult to decipher amidst the heat of battle.
Community Verdict: Warzone 2.0's Rocky Start and Promising Future
Despite its ambitious overhaul and introduction of engrossing new features, Call of Duty®: Warzone™ 2.0 has been met with a mix of admiration and critique. The community has been vocal about their experiences, praising the game's direction in offering a more intense and immersive combat experience while simultaneously pointing out the technical hiccups that hinder gameplay. These issues, ranging from performance dips to interface complexities, have not gone unnoticed by the developers, who are seemingly committed to ironing out these kinks as the game progresses. The general consensus among players is that Warzone 2.0, with its expansive and dynamic map of Al Mazrah, has laid the groundwork for what could be the most exhilarating battle royale experience to date. As patches and updates continue to refine the experience, there is a palpable sense of optimism that Warzone 2.0 will overcome its initial troubles to emerge as a flagship title in the genre.
2026-05-02
Read full review
![Wattpad - Read & Write Stories Wattpad - Read & Write Stories]() action
Wattpad - Read & Write Stories
Wattpad - Read & Write Stories is a popular app with a loyal following of avid readers and writers. The application provides a user-friendly interface that is straightforward to use. Users can easily find stories to read or write, and the app supports a variety of story formats. Wattpad - Read & Write Stories is a great app for readers and writers looking for a simple, user-friendly platform. The stories are well organized, and the app allows you to search for specific stories or topics. The app is also easy to navigate, and the stories are easy to read. The application is available at no cost and does not necessitate a subscription.
Interface
The interface of Wattpad - Read & Write Stories is clean and straightforward. The app's main page features a scrolling list of stories divided into categories. Users can easily find stories to read or write, and the app supports a variety of story formats. The interface is simple and effective and makes it easy to find the content you're looking for. You can browse stories by category, popularity, or recent additions. You can also search for specific stories or authors. The main page shows a list of stories, and users can easily browse through them and select the ones they want to read. The app also has a search function that makes it easy to find specific stories.
Usability
Wattpad - Read & Write Stories is a highly usable app. The interface is simple and easy to navigate, and users can easily find stories to read or write. The app supports a variety of story formats, making it easy to find the content you're looking for. The app is also highly responsive, and stories load quickly and without issue. You can customize the font size and background color to suit your preferences. You can also add stories to your favorites list for easy access later. The stories are well organized, and the app allows you to search for specific stories or topics. The app is also easy to navigate, and the stories are easy to read.
Functionality
Wattpad has a lot of different features. You can read and write stories, and you can also share them with others. The support is excellent, and there is a lot of helpful information on the website. The app offers a great selection of stories, novels, and fan fiction. You can also create and share your own stories. The app also allows you to connect with other writers and readers.
Support
Wattpad - Read & Write Stories offers excellent support. The app's main page features a scrolling list of stories, divided into categories. Users can easily find stories to read or write, and the app supports a variety of story formats. The app is also highly responsive, and stories load quickly and without issue. If you have any problems using the app, Wattpad's customer support team is quick to respond and helpful.
Pros
Wattpad is a free app that provides unlimited access to a wide range of stories and books
You can read stories offline once they have been downloaded
The app has a user-friendly interface
You can interact with other users by sharing your stories or commenting on theirs
You can customize your reading experience by changing the font size and background color
You can access Wattpad through your computer, mobile phone, or tablet
Cons
Some stories may contain mature content that is not suitable for younger readers
You may need to create a Wattpad account in order to access some features
Some stories may not be available in your country
2026-05-02
Read full review
action
Wattpad - Read & Write Stories
Wattpad - Read & Write Stories is a popular app with a loyal following of avid readers and writers. The application provides a user-friendly interface that is straightforward to use. Users can easily find stories to read or write, and the app supports a variety of story formats. Wattpad - Read & Write Stories is a great app for readers and writers looking for a simple, user-friendly platform. The stories are well organized, and the app allows you to search for specific stories or topics. The app is also easy to navigate, and the stories are easy to read. The application is available at no cost and does not necessitate a subscription.
Interface
The interface of Wattpad - Read & Write Stories is clean and straightforward. The app's main page features a scrolling list of stories divided into categories. Users can easily find stories to read or write, and the app supports a variety of story formats. The interface is simple and effective and makes it easy to find the content you're looking for. You can browse stories by category, popularity, or recent additions. You can also search for specific stories or authors. The main page shows a list of stories, and users can easily browse through them and select the ones they want to read. The app also has a search function that makes it easy to find specific stories.
Usability
Wattpad - Read & Write Stories is a highly usable app. The interface is simple and easy to navigate, and users can easily find stories to read or write. The app supports a variety of story formats, making it easy to find the content you're looking for. The app is also highly responsive, and stories load quickly and without issue. You can customize the font size and background color to suit your preferences. You can also add stories to your favorites list for easy access later. The stories are well organized, and the app allows you to search for specific stories or topics. The app is also easy to navigate, and the stories are easy to read.
Functionality
Wattpad has a lot of different features. You can read and write stories, and you can also share them with others. The support is excellent, and there is a lot of helpful information on the website. The app offers a great selection of stories, novels, and fan fiction. You can also create and share your own stories. The app also allows you to connect with other writers and readers.
Support
Wattpad - Read & Write Stories offers excellent support. The app's main page features a scrolling list of stories, divided into categories. Users can easily find stories to read or write, and the app supports a variety of story formats. The app is also highly responsive, and stories load quickly and without issue. If you have any problems using the app, Wattpad's customer support team is quick to respond and helpful.
Pros
Wattpad is a free app that provides unlimited access to a wide range of stories and books
You can read stories offline once they have been downloaded
The app has a user-friendly interface
You can interact with other users by sharing your stories or commenting on theirs
You can customize your reading experience by changing the font size and background color
You can access Wattpad through your computer, mobile phone, or tablet
Cons
Some stories may contain mature content that is not suitable for younger readers
You may need to create a Wattpad account in order to access some features
Some stories may not be available in your country
2026-05-02
Read full review
![Toca Kitchen 2 Toca Kitchen 2]() educational
Toca Kitchen 2
Toca Kitchen 2 is a game for kids, and is perfect for kids of all ages. The game is meant for the kids to imitate what they see in the game, and to learn new cooking techniques. The game is highly interactive and is fun for kids to play. Toca Kitchen 2 is a free mobile app for iOS and Android devices that offers a simple environment for players of all ages. The game offers an interactive and creative cooking experience for players of all ages, as well as a chance to learn about cooking and the tools and materials that are used.
Gameplay
In the game, the player is in control of two chefs, and they have to cook meals. The player has to make sure the food is the correct temperature, and that the condiments are in the right place. There are many different recipes the player can choose from, and the player can even create their own recipe. The gameplay for Toca Kitchen 2 is relatively simple and easy to understand. Players have access to a variety of ingredients and food, and can use those ingredients to create an endless number of dishes. Players can use tools that are available to them, such as a cutting board, knife, and pan, to prepare the food and prepare it for cooking. However, not all ingredients and tools are available to the player at the start. Players can unlock new ingredients and tools by completing new levels.
Graphics
The graphics are very child friendly, and they are colorful and creative. There are many different foods to choose from, and the player has to make sure they are the correct color. The graphics for Toca Kitchen 2 are very simple, but the simplicity is what makes the game so appealing to a wide range of audiences. The game is designed with a simplistic design and a layout that is very easy to understand. There is a lot of color in the game, and the game is very bright and inviting.
Information about replayability
The game can be played multiple times and the player will still experience new things. The player can also play the game in different ways, such as using the left hand or the right hand.
Pros
The game is interactive and the player can choose which hand to use, which is a new feature in this game
The game has many different recipes to choose from, and it is a fun game for kids to play
Cons
There is no multi-player mode, so the player can't play the game with their friends
The game is only for kids, so adults may not enjoy it
2026-05-02
Read full review
educational
Toca Kitchen 2
Toca Kitchen 2 is a game for kids, and is perfect for kids of all ages. The game is meant for the kids to imitate what they see in the game, and to learn new cooking techniques. The game is highly interactive and is fun for kids to play. Toca Kitchen 2 is a free mobile app for iOS and Android devices that offers a simple environment for players of all ages. The game offers an interactive and creative cooking experience for players of all ages, as well as a chance to learn about cooking and the tools and materials that are used.
Gameplay
In the game, the player is in control of two chefs, and they have to cook meals. The player has to make sure the food is the correct temperature, and that the condiments are in the right place. There are many different recipes the player can choose from, and the player can even create their own recipe. The gameplay for Toca Kitchen 2 is relatively simple and easy to understand. Players have access to a variety of ingredients and food, and can use those ingredients to create an endless number of dishes. Players can use tools that are available to them, such as a cutting board, knife, and pan, to prepare the food and prepare it for cooking. However, not all ingredients and tools are available to the player at the start. Players can unlock new ingredients and tools by completing new levels.
Graphics
The graphics are very child friendly, and they are colorful and creative. There are many different foods to choose from, and the player has to make sure they are the correct color. The graphics for Toca Kitchen 2 are very simple, but the simplicity is what makes the game so appealing to a wide range of audiences. The game is designed with a simplistic design and a layout that is very easy to understand. There is a lot of color in the game, and the game is very bright and inviting.
Information about replayability
The game can be played multiple times and the player will still experience new things. The player can also play the game in different ways, such as using the left hand or the right hand.
Pros
The game is interactive and the player can choose which hand to use, which is a new feature in this game
The game has many different recipes to choose from, and it is a fun game for kids to play
Cons
There is no multi-player mode, so the player can't play the game with their friends
The game is only for kids, so adults may not enjoy it
2026-05-02
Read full review
![footer-decor]()
Expert blog
![EA Sports College Football 25 Had 2.8 Million Players Before Worldwide Launch EA Sports College Football 25 Had 2.8 Million Players Before Worldwide Launch]() News
EA Sports College Football 25 Had 2.8 Million Players Before Worldwide Launch
The global launch of EA Sports College Football 25 has certainly created a stir in the gaming world, boasting a whopping 2.8 million players served during its early access period. This figure includes 2.2 million unique players who bought the Deluxe and MVP Editions and an additional 600,000 players who entered the gaming arena via EA Play.
The enthusiasm around this launch is tremendous, considering that its predecessor, NCAA Football 14, saw the light of day more than a decade ago. Daryl Holt, SVP and group GM for EA Sports, expressed his team's delight over the robust response from sports fans, athletes, creators, celebrities, and their core community. He emphasized that the game, designed with ardent college football enthusiasts in mind, is loaded with authentic experiences.
Promising a highly realistic gaming experience, EA Sports College Football 25 employs a novel gameplay system named CampusIQ. This involves selecting the brightest stars for your lineup and keeping track of player fatigue and the effects of varied impacts and hits. It offers a suite of Physical and Mental Abilities to twist the game dynamics and introduces the concept of Homefield Advantage.
With a treasure of modes like Dynasty, Road to Glory, and College Football Ultimate Team, EA Sports College Football 25 presents a spectrum of exciting prospects for seasoned fans. The game is compatible with PS5 and Xbox Series X/S platforms.
News
EA Sports College Football 25 Had 2.8 Million Players Before Worldwide Launch
The global launch of EA Sports College Football 25 has certainly created a stir in the gaming world, boasting a whopping 2.8 million players served during its early access period. This figure includes 2.2 million unique players who bought the Deluxe and MVP Editions and an additional 600,000 players who entered the gaming arena via EA Play.
The enthusiasm around this launch is tremendous, considering that its predecessor, NCAA Football 14, saw the light of day more than a decade ago. Daryl Holt, SVP and group GM for EA Sports, expressed his team's delight over the robust response from sports fans, athletes, creators, celebrities, and their core community. He emphasized that the game, designed with ardent college football enthusiasts in mind, is loaded with authentic experiences.
Promising a highly realistic gaming experience, EA Sports College Football 25 employs a novel gameplay system named CampusIQ. This involves selecting the brightest stars for your lineup and keeping track of player fatigue and the effects of varied impacts and hits. It offers a suite of Physical and Mental Abilities to twist the game dynamics and introduces the concept of Homefield Advantage.
With a treasure of modes like Dynasty, Road to Glory, and College Football Ultimate Team, EA Sports College Football 25 presents a spectrum of exciting prospects for seasoned fans. The game is compatible with PS5 and Xbox Series X/S platforms.
![Ava Reynolds Ava Reynolds]() Ava Reynolds
2024-07-20
Ava Reynolds
2024-07-20
News
![Alabaster Dawn Planned to Have 30-60 Hours of Playtime, Demo Launching in Early 2025 Alabaster Dawn Planned to Have 30-60 Hours of Playtime, Demo Launching in Early 2025]() News
Alabaster Dawn Planned to Have 30-60 Hours of Playtime, Demo Launching in Early 2025
Radical Fish Games has made an exciting announcement regarding their upcoming action RPG, Alabaster Dawn, which is set to enter early access in 2025. In the recent Steam listing, the developer shared that players can expect a gameplay duration ranging from 30 to 60 hours, mirroring the experience offered in their previous title, Crosscode.
The game will feature seven distinct regions and introduce new mechanics, including the ability to reconstruct settlements and establish trade routes. This dynamic will allow settlements to grow and evolve, ultimately leading to the opening of "new paths and opportunities." Players can also look forward to uncovering numerous secrets along their journey.
In anticipation of the release, a public demo will debut in early 2025. The studio mentioned that a vertical slice of the game has been under development throughout the year, showcasing a variety of scripted cutscenes, two challenging bosses, and an intriguing dungeon. The initial one to two hours is reported to be "almost fully playable," with the pace of development expected to accelerate as more systems are integrated. The forthcoming demonstration will showcase this specific segment, allowing players to sample what lies ahead.
The decision for early access aims to gather ongoing feedback from a broader audience, ultimately enhancing the gaming experience while also ensuring financial backing. Although CrossCode had a similar early access phase prior to its release, Radical Fish Games hopes that the timeline for Alabaster Dawn will be shorter.
Representatives and attendees of Gamescom will have an opportunity to explore the latest Alabaster Dawn build at the developer's booth.
News
Alabaster Dawn Planned to Have 30-60 Hours of Playtime, Demo Launching in Early 2025
Radical Fish Games has made an exciting announcement regarding their upcoming action RPG, Alabaster Dawn, which is set to enter early access in 2025. In the recent Steam listing, the developer shared that players can expect a gameplay duration ranging from 30 to 60 hours, mirroring the experience offered in their previous title, Crosscode.
The game will feature seven distinct regions and introduce new mechanics, including the ability to reconstruct settlements and establish trade routes. This dynamic will allow settlements to grow and evolve, ultimately leading to the opening of "new paths and opportunities." Players can also look forward to uncovering numerous secrets along their journey.
In anticipation of the release, a public demo will debut in early 2025. The studio mentioned that a vertical slice of the game has been under development throughout the year, showcasing a variety of scripted cutscenes, two challenging bosses, and an intriguing dungeon. The initial one to two hours is reported to be "almost fully playable," with the pace of development expected to accelerate as more systems are integrated. The forthcoming demonstration will showcase this specific segment, allowing players to sample what lies ahead.
The decision for early access aims to gather ongoing feedback from a broader audience, ultimately enhancing the gaming experience while also ensuring financial backing. Although CrossCode had a similar early access phase prior to its release, Radical Fish Games hopes that the timeline for Alabaster Dawn will be shorter.
Representatives and attendees of Gamescom will have an opportunity to explore the latest Alabaster Dawn build at the developer's booth.
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-08-13
Ethan Blackstone
2024-08-13
-
![CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025 CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025]() News
CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025
In 2021, Radical Fish Games initially introduced a new action RPG titled Project Terra. Now, they have officially named it Alabaster Dawn and announced that it will be available in Steam Early Access in late 2025.
The narrative centers around Juno, referred to as the “Outcast Chosen.” She awakens to find herself in a devastated world and embarks on a quest to revive humanity while confronting the enigmatic Nyx, who seems to be linked to the calamity that has befallen civilization. Fans of CrossCode will recognize familiar elements in the combat mechanics, world layout, and platforming aspects. The traditional four elemental forces return, but players now have access to eight distinct weapons.
Each of the four elements corresponds to two different weapons, allowing for a flexible combat experience. Additionally, the game will feature Combat Arts, which offers a range of techniques to use in battles, along with brand-new Divine Arts. Participants will be able to explore the expansive terrain, collect an assortment of precious Stones, obtain resources for upgrades, and discover culinary formulas that enable them to create dishes providing short-term advantages.
While Alabaster Dawn does not have a specific release date set yet, it has been confirmed for future availability on consoles and PC, creating excitement within the gaming community.
News
CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025
In 2021, Radical Fish Games initially introduced a new action RPG titled Project Terra. Now, they have officially named it Alabaster Dawn and announced that it will be available in Steam Early Access in late 2025.
The narrative centers around Juno, referred to as the “Outcast Chosen.” She awakens to find herself in a devastated world and embarks on a quest to revive humanity while confronting the enigmatic Nyx, who seems to be linked to the calamity that has befallen civilization. Fans of CrossCode will recognize familiar elements in the combat mechanics, world layout, and platforming aspects. The traditional four elemental forces return, but players now have access to eight distinct weapons.
Each of the four elements corresponds to two different weapons, allowing for a flexible combat experience. Additionally, the game will feature Combat Arts, which offers a range of techniques to use in battles, along with brand-new Divine Arts. Participants will be able to explore the expansive terrain, collect an assortment of precious Stones, obtain resources for upgrades, and discover culinary formulas that enable them to create dishes providing short-term advantages.
While Alabaster Dawn does not have a specific release date set yet, it has been confirmed for future availability on consoles and PC, creating excitement within the gaming community.
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-08-12
Ethan Blackstone
2024-08-12
-
![Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO]() News
Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO
Despite its lackluster reception, Battlefield 2042 hasn't deterred EA from its commitment to the franchise. The company is channeling considerable resources into the next installment, with several of its studios collaborating on the project. Although specific details remain sparse, EA's CEO Andrew Wilson recently shared insights about what lies ahead for the Battlefield series.
During a quarterly earnings call, Wilson characterized the forthcoming game as one of EA’s most ambitious endeavors to date. He expressed confidence in the development team, stating that their goal is to create an immersive Battlefield experience that excites the player community. The enthusiasm around the project, according to Wilson, signals strong support for the team’s direction.
An array of studios is contributing to the Battlefield effort. Lead developer DICE is at the forefront, while Criterion Games is set to handle the single-player campaign after the dissolution of Ridgeline Games earlier this year. Additionally, the acclaimed Motive Studio is assembling a new team to support the game's development.
According to earlier reports, the upcoming Battlefield title is on track for release in October 2025. Meanwhile, Ripple Effect Studios is believed to be crafting a separate free-to-play battle royale experience within the franchise, further expanding its offerings.
News
Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO
Despite its lackluster reception, Battlefield 2042 hasn't deterred EA from its commitment to the franchise. The company is channeling considerable resources into the next installment, with several of its studios collaborating on the project. Although specific details remain sparse, EA's CEO Andrew Wilson recently shared insights about what lies ahead for the Battlefield series.
During a quarterly earnings call, Wilson characterized the forthcoming game as one of EA’s most ambitious endeavors to date. He expressed confidence in the development team, stating that their goal is to create an immersive Battlefield experience that excites the player community. The enthusiasm around the project, according to Wilson, signals strong support for the team’s direction.
An array of studios is contributing to the Battlefield effort. Lead developer DICE is at the forefront, while Criterion Games is set to handle the single-player campaign after the dissolution of Ridgeline Games earlier this year. Additionally, the acclaimed Motive Studio is assembling a new team to support the game's development.
According to earlier reports, the upcoming Battlefield title is on track for release in October 2025. Meanwhile, Ripple Effect Studios is believed to be crafting a separate free-to-play battle royale experience within the franchise, further expanding its offerings.
![Ava Reynolds Ava Reynolds]() Ava Reynolds
2024-08-07
Ava Reynolds
2024-08-07
-
![Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges” Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges”]() News
Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges”
Marvel Rivals is shaping up to be an exciting entry into the hero shooter genre, thanks in part to its well-established branding and the unique capabilities it brings to the table. The game boasts an impressive lineup of playable characters, each equipped with diverse moves and skills. However, this variety has presented some hurdles for the development team at NetEase Games.
In a recent discussion with GamingBolt, the developers revealed that balancing the experience while ensuring every character feels distinct has been a significant challenge—especially concerning melee-heavy heroes like Thor, Spider-Man, and the Incredible Hulk. If not properly handled, the dynamic of close-quarters combat could lead to chaotic gameplay that might detract from the enjoyment.
The developers articulated their struggle, emphasizing that crafting a diverse set of melee combatants was a top priority. They noted that mishandling these characters could result in battles lacking substance, ultimately compromising the gaming experience.
Yet, the unique abilities of the Marvel roster also presented exciting opportunities for the developers. They explained how the Hulk's impressive leaping ability was designed to impact aerial foes, adding an interesting layer to his play style. Venom's symbiotic traits were expanded to allow for mid-range attacks, while Spider-Man’s agility enables fluid transitions between melee and ranged encounters.
By focusing on each hero's strengths, the team aims to create a captivating gameplay experience that highlights each character’s unique mechanics.
Marvel Rivals is currently under development for PS5, Xbox Series X/S, and PC, with no confirmed release date available at this time.
News
Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges”
Marvel Rivals is shaping up to be an exciting entry into the hero shooter genre, thanks in part to its well-established branding and the unique capabilities it brings to the table. The game boasts an impressive lineup of playable characters, each equipped with diverse moves and skills. However, this variety has presented some hurdles for the development team at NetEase Games.
In a recent discussion with GamingBolt, the developers revealed that balancing the experience while ensuring every character feels distinct has been a significant challenge—especially concerning melee-heavy heroes like Thor, Spider-Man, and the Incredible Hulk. If not properly handled, the dynamic of close-quarters combat could lead to chaotic gameplay that might detract from the enjoyment.
The developers articulated their struggle, emphasizing that crafting a diverse set of melee combatants was a top priority. They noted that mishandling these characters could result in battles lacking substance, ultimately compromising the gaming experience.
Yet, the unique abilities of the Marvel roster also presented exciting opportunities for the developers. They explained how the Hulk's impressive leaping ability was designed to impact aerial foes, adding an interesting layer to his play style. Venom's symbiotic traits were expanded to allow for mid-range attacks, while Spider-Man’s agility enables fluid transitions between melee and ranged encounters.
By focusing on each hero's strengths, the team aims to create a captivating gameplay experience that highlights each character’s unique mechanics.
Marvel Rivals is currently under development for PS5, Xbox Series X/S, and PC, with no confirmed release date available at this time.
![Latanskiy Nick Latanskiy Nick]() Latanskiy Nick
2024-08-05
Latanskiy Nick
2024-08-05
![footer-decor]()
Editor's Choice
![The Last of Us Part II: In-Depth Character Analysis and Storyline Exploration The Last of Us Part II: In-Depth Character Analysis and Storyline Exploration]() Editor’s Choice
The Last of Us Part II: In-Depth Character Analysis and Storyline Exploration
The Last of Us Part II is an action-adventure video game that has gained significant popularity since its inception. Developed with immense creative prowess by Naughty Dog and published by the renowned Sony Interactive Entertainment, this video game has managed to carve a niche for itself in the competitive world of gaming. The distinct element that elevates this game's renown is its remarkable gameplay that enthralls both veteran game enthusiasts and fledgling players in equal measure.
The gaming encounter takes place in a world devastated by a catastrophic event, creating an enthralling canvas for the gameplay. However, it's not just the high-octane action sequences that make this game stand out. The heart of The Last of Us Part II lies in its deep storytelling, which proves to be just as, if not more, gripping as its action.
The depth of the characters in this game is truly commendable. The creators focused on building characters that are both relatable and complex, thereby ensuring the gamers' emotional investment in the plot. Alongside the main characters, the minor characters have also been carefully crafted, resulting in a realistic and immersive gaming experience.
Another important aspect that elevates The Last of Us Part II to a new level is its intricately woven plot. The complexity and layers of the story intrigue gamers, prompting them to delve deeper into the game's universe. It is this combination of deep characters and a well-crafted plot that provides the game its unique brand of strength and appeal.
In this article, we aim to delve further into the game's universe. We will be exploring the game's main characters, their development throughout the story, and the nuanced storyline that keeps the players hooked. By understanding these aspects in more depth, we can appreciate the ingenuity and hard work behind this successful game.
Main Characters and Character Development
The Last of Us Part II centers its narrative largely around two characters, Ellie and Abby. These individuals aren't mere characters in the gaming world, but rather, they are the backbone of this sequel, playing integral roles in driving the game's complex storyline. Their well-crafted persona and emotional depth bring a level of realness to the game that is rare to find, offering players the opportunity to delve deeper into their motives, thoughts, and actions.
Breaking away from the traditional approach of its predecessor, The Last of Us Part II takes a bold step in storytelling by providing a dual perspective in its narrative. This unique spin allows the players to experience the story from both Ellie's and Abby's points of view, lending much-needed depth to the storyline. It also highlights the subjectivity of human perception and experience as the same event unfolds differently in each character's gameplay, hence leaving the players with a broader outlook and understanding of the story.
The characters, Ellie and Abby, undergo elaborate character arcs throughout the game. They evolve tremendously; their growth is evident in their changing ideologies, decisions, and varying responses to the challenges they confront. By focusing on their character development, the game manages to convey the profound impacts of their life experiences and challenges faced in the post-apocalyptic world on their personalities.
Lastly, the game navigates through the complexities of Ellie and Abby's actions and emotions. It unearths the reasons behind their decisions, their conflicting emotions, and their struggle with their past and present. This exploration of complexity drives home the point that the characters aren't merely heroes or villains but complex individuals caught in a world where survival takes precedence over everything else.
Ellie: The Haunted Protagonist
Ellie, a nineteen-year-old survivor, sets out on a journey of retribution when a tragedy befalls her peaceful life in the post-apocalyptic world. Her character undergoes layers of transformation, moving from a carefree teenager to a revenge-driven individual. Her decisions, guided by pain and rage, paint a heart-wrenching picture of human vulnerability and resilience.
Abby: The Conflicted Antagonist
Abby's character challenges conventional villain templates. She evolves from a character initially perceived as ruthless to revealing her humane side shadowed by her past. Abby's quest for redemption, contrasted with her violent actions, incites conflicting emotions among players, thus enriching the narrative.
Secondary Characters: Their Impact and Role
Several secondary characters play crucial roles across the game, aiding and influencing the main characters' journey in profound ways. Key characters include Joel, Dina, and Isaac.
Joel: The Lingering Spirit
While the game starts with Joel's brutal end, his influence persists throughout the narrative. His actions in the prequel lay the groundwork for the events in The Last of Us Part II, leaving Ellie and Abby to suffer the repercussions of his choices.
Dina: Ellie's Anchor
Dina, a key ally and love interest of Ellie, provides solace and helps Ellie retain her humanity. Her character demonstrates the power of love and friendship in extreme circumstances and the consequences of their loss.
Isaac: The Cold Strategist
Isaac, the strategic leader of the Washington Liberation Front, plays an essential role in the war between factions. He illustrates the dehumanizing effects of long-term conflict and the cost of dogmatism.
Plot Analysis: The Multifaceted Storyline
The Last of Us Part II weaves an intricate tale revolving around both its hero and villain, probing profound undertones of existence, vengeance, affection, and atonement.
Survival and Revenge
The gaming narrative portrays the brutal truths of a world that has undergone an apocalypse, wherein the battle for survival is an unending challenge. Revenge emerges as a driving force, coloring the decisions and actions of the main characters while underlining the damaging effects of this dangerous pursuit.
Love and Redemption
Balancing the bleak aspects of the storyline are themes of love and redemption. These themes explore how love can act as a stabilizing influence and how redemption might be possible even in the most despairing circumstances. They add emotional depth and intricacy to the narrative.
Controversial Storytelling and Player Interpretations
The Last of Us Part II has incited polarizing reactions among players due to its unconventional storytelling and character development. Contemporary thematic exploration and unexpected character arcs have led to various interpretations and theories among the fanbase.
Conclusion: Assessing the Narrative Impact
The Last of Us Part II offers a highly immersive experience through compelling characters and a thought-provoking storyline. Its characters challenge traditional boundaries, growing and evolving through personal losses and wins. The multifaceted narrative blends elements of survival, revenge, love, and redemption, invoking strong emotions and prompting players to delve deeper. Despite its polarizing reception, the game ultimately solidifies its standing as a profound exploration of human nature in extreme circumstances.
Editor’s Choice
The Last of Us Part II: In-Depth Character Analysis and Storyline Exploration
The Last of Us Part II is an action-adventure video game that has gained significant popularity since its inception. Developed with immense creative prowess by Naughty Dog and published by the renowned Sony Interactive Entertainment, this video game has managed to carve a niche for itself in the competitive world of gaming. The distinct element that elevates this game's renown is its remarkable gameplay that enthralls both veteran game enthusiasts and fledgling players in equal measure.
The gaming encounter takes place in a world devastated by a catastrophic event, creating an enthralling canvas for the gameplay. However, it's not just the high-octane action sequences that make this game stand out. The heart of The Last of Us Part II lies in its deep storytelling, which proves to be just as, if not more, gripping as its action.
The depth of the characters in this game is truly commendable. The creators focused on building characters that are both relatable and complex, thereby ensuring the gamers' emotional investment in the plot. Alongside the main characters, the minor characters have also been carefully crafted, resulting in a realistic and immersive gaming experience.
Another important aspect that elevates The Last of Us Part II to a new level is its intricately woven plot. The complexity and layers of the story intrigue gamers, prompting them to delve deeper into the game's universe. It is this combination of deep characters and a well-crafted plot that provides the game its unique brand of strength and appeal.
In this article, we aim to delve further into the game's universe. We will be exploring the game's main characters, their development throughout the story, and the nuanced storyline that keeps the players hooked. By understanding these aspects in more depth, we can appreciate the ingenuity and hard work behind this successful game.
Main Characters and Character Development
The Last of Us Part II centers its narrative largely around two characters, Ellie and Abby. These individuals aren't mere characters in the gaming world, but rather, they are the backbone of this sequel, playing integral roles in driving the game's complex storyline. Their well-crafted persona and emotional depth bring a level of realness to the game that is rare to find, offering players the opportunity to delve deeper into their motives, thoughts, and actions.
Breaking away from the traditional approach of its predecessor, The Last of Us Part II takes a bold step in storytelling by providing a dual perspective in its narrative. This unique spin allows the players to experience the story from both Ellie's and Abby's points of view, lending much-needed depth to the storyline. It also highlights the subjectivity of human perception and experience as the same event unfolds differently in each character's gameplay, hence leaving the players with a broader outlook and understanding of the story.
The characters, Ellie and Abby, undergo elaborate character arcs throughout the game. They evolve tremendously; their growth is evident in their changing ideologies, decisions, and varying responses to the challenges they confront. By focusing on their character development, the game manages to convey the profound impacts of their life experiences and challenges faced in the post-apocalyptic world on their personalities.
Lastly, the game navigates through the complexities of Ellie and Abby's actions and emotions. It unearths the reasons behind their decisions, their conflicting emotions, and their struggle with their past and present. This exploration of complexity drives home the point that the characters aren't merely heroes or villains but complex individuals caught in a world where survival takes precedence over everything else.
Ellie: The Haunted Protagonist
Ellie, a nineteen-year-old survivor, sets out on a journey of retribution when a tragedy befalls her peaceful life in the post-apocalyptic world. Her character undergoes layers of transformation, moving from a carefree teenager to a revenge-driven individual. Her decisions, guided by pain and rage, paint a heart-wrenching picture of human vulnerability and resilience.
Abby: The Conflicted Antagonist
Abby's character challenges conventional villain templates. She evolves from a character initially perceived as ruthless to revealing her humane side shadowed by her past. Abby's quest for redemption, contrasted with her violent actions, incites conflicting emotions among players, thus enriching the narrative.
Secondary Characters: Their Impact and Role
Several secondary characters play crucial roles across the game, aiding and influencing the main characters' journey in profound ways. Key characters include Joel, Dina, and Isaac.
Joel: The Lingering Spirit
While the game starts with Joel's brutal end, his influence persists throughout the narrative. His actions in the prequel lay the groundwork for the events in The Last of Us Part II, leaving Ellie and Abby to suffer the repercussions of his choices.
Dina: Ellie's Anchor
Dina, a key ally and love interest of Ellie, provides solace and helps Ellie retain her humanity. Her character demonstrates the power of love and friendship in extreme circumstances and the consequences of their loss.
Isaac: The Cold Strategist
Isaac, the strategic leader of the Washington Liberation Front, plays an essential role in the war between factions. He illustrates the dehumanizing effects of long-term conflict and the cost of dogmatism.
Plot Analysis: The Multifaceted Storyline
The Last of Us Part II weaves an intricate tale revolving around both its hero and villain, probing profound undertones of existence, vengeance, affection, and atonement.
Survival and Revenge
The gaming narrative portrays the brutal truths of a world that has undergone an apocalypse, wherein the battle for survival is an unending challenge. Revenge emerges as a driving force, coloring the decisions and actions of the main characters while underlining the damaging effects of this dangerous pursuit.
Love and Redemption
Balancing the bleak aspects of the storyline are themes of love and redemption. These themes explore how love can act as a stabilizing influence and how redemption might be possible even in the most despairing circumstances. They add emotional depth and intricacy to the narrative.
Controversial Storytelling and Player Interpretations
The Last of Us Part II has incited polarizing reactions among players due to its unconventional storytelling and character development. Contemporary thematic exploration and unexpected character arcs have led to various interpretations and theories among the fanbase.
Conclusion: Assessing the Narrative Impact
The Last of Us Part II offers a highly immersive experience through compelling characters and a thought-provoking storyline. Its characters challenge traditional boundaries, growing and evolving through personal losses and wins. The multifaceted narrative blends elements of survival, revenge, love, and redemption, invoking strong emotions and prompting players to delve deeper. Despite its polarizing reception, the game ultimately solidifies its standing as a profound exploration of human nature in extreme circumstances.
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-08-11
Ethan Blackstone
2024-08-11
-
![Out of the shadows and into the light: Embracing responsible AI practices amid bias and hallucinations Out of the shadows and into the light: Embracing responsible AI practices amid bias and hallucinations]() Editor’s Choice
Out of the shadows and into the light: Embracing responsible AI practices amid bias and hallucinations
The path to widespread AI is a bumpy one. While its potential to enhance consumer experiences and streamline business operations through personalization, autonomy, and decentralized reasoning is evident, the technology comes with inherent risks. AI can produce conclusions that aren’t true, spread misinformation and in some cases, perpetuate existing biases. This -- the darker side of AI’s impact -- can leave business leaders facing financial, legal, and reputational damage.
Lost in the Digital Dream
AI is prone to hallucinations. These are instances where models draw a conclusion that while coherent, are detached from reality or from the input’s context. Similar to a human hallucination, AI can experience a digital mirage, blurring the lines between what’s real and what’s not. For instance, ChatGPT’s earlier version once responded to a neuroscientist that the Golden Gate Bridge was moved across Egypt in 2016. Such imaginative and unexpected outputs serve as a reminder that AI’s conclusions are not immune to errors or misinterpretations.
But not all AI hallucinations will be this harmless. Businesses that rely on flawed AI outputs may be left with costly errors. In critical sectors like healthcare, this can quickly become a matter of life or death. Imagine a scenario where an AI system is designed to detect heart conditions. If the AI hallucinates a heartbeat irregularity, incorrect diagnosis could occur, resulting in unnecessary medical interventions and endangering patient safety.
Bias in AI Models
Problems also arise when AI models are based on biased datasets. Previously, Amazon used an AI-based recruitment tool to help hire employees. The AI tool had been trained on a data set that reflected historical and societal inequities which may exist even if normalized by removing those factors. Rather than helping to find the best candidates, the AI inadvertently discriminated against female applicants, systematically rejecting their resumes. Far from identifying the best candidates, the tool perpetuated existing inequities. This example highlights not only the reproduction of real-world biases in AI systems, but also the amplification of those biases, potentially worsening future outcomes. The absence of comprehensive regulations around AI can exacerbate these mistakes, leaving businesses without clear directives on prevention.
As a result of hallucinations and biases, businesses can face lawsuits for negligence or discrimination, resulting in fines. Financial losses may arise from erroneous decisions and missed opportunities, while an untrustworthy AI model can drive customers away. These issues could leave organizations deeming AI as too risky, abandoning projects they had planned. In cases where uses of AI would increase productivity, these projects being dropped might leave staff with extra work.
RAG to the Rescue
Despite the inherent challenges, AI offers significant opportunities for businesses. By adopting the appropriate tools, models, and best practices, companies can effectively address potential issues and fully leverage AI's capabilities. Techniques like retrieval-augmented generation (RAG) are instrumental in tackling problems related to bias, fairness, and hallucinations. RAG models integrate retrieval mechanisms that enable access to extensive, diverse, and pertinent data. Leveraging a wide array of sources helps these models reduce the impact of biases found in smaller or more restricted datasets.
RAG models also excel at generating responses that are grounded in verifiable information. This can eliminate AI hallucinations, providing data inputs that are enriched with context-specific information and retrieved from reliable sources. This means RAG models can be fine-tuned for specific tasks or use-cases, benefiting users by providing information that is unique to their situation. This is especially useful for businesses that don’t have the time or budget to retrain AI models with domain-specific datasets.
In the recruiting example above, RAG can help inform the model with newer hiring guidelines, HR policies and equal employment opportunity laws, ensuring a broad and balanced approach for all candidates to receive fair and equal treatment.
Practical Applications of RAG
Beyond retrieving relevant information, businesses also benefit from RAG models’ ability to generate a natural response. Interactions with these models will generally be more conversational and user friendly. This is particularly useful for customer facing applications. RAG models should form a key part of a modern data approach. To enhance their effectiveness, RAG models require access to real-time data to ensure that information is as fresh and as accurate as possible. They should also be paired with an operational data store that holds information in high-dimensional mathematical vectors. Models can therefore convert a user’s query into numerical vectors when asked, allowing the AI to respond to relevant text inquiries even if they don’t precisely match the original terms or phrases.
By using real-time data and databases that operate in vectors, AI model outputs remain up-to-date, reducing the risk of outdated information leading to hallucinations.
Heading Towards a Brighter Future
As we embark on the journey towards AI’s widespread adoption, organizations must be aware of the consequences of AI gone wrong. A comprehensive approach to AI is crucial. This paves the way for ethical, fair, and secure AI systems that enhance productivity and personalization without propagating misinformation. By prioritizing responsible AI practices, such as employing RAG models, businesses ensure AI remains a positive force in society, rather than something to be feared.
Editor’s Choice
Out of the shadows and into the light: Embracing responsible AI practices amid bias and hallucinations
The path to widespread AI is a bumpy one. While its potential to enhance consumer experiences and streamline business operations through personalization, autonomy, and decentralized reasoning is evident, the technology comes with inherent risks. AI can produce conclusions that aren’t true, spread misinformation and in some cases, perpetuate existing biases. This -- the darker side of AI’s impact -- can leave business leaders facing financial, legal, and reputational damage.
Lost in the Digital Dream
AI is prone to hallucinations. These are instances where models draw a conclusion that while coherent, are detached from reality or from the input’s context. Similar to a human hallucination, AI can experience a digital mirage, blurring the lines between what’s real and what’s not. For instance, ChatGPT’s earlier version once responded to a neuroscientist that the Golden Gate Bridge was moved across Egypt in 2016. Such imaginative and unexpected outputs serve as a reminder that AI’s conclusions are not immune to errors or misinterpretations.
But not all AI hallucinations will be this harmless. Businesses that rely on flawed AI outputs may be left with costly errors. In critical sectors like healthcare, this can quickly become a matter of life or death. Imagine a scenario where an AI system is designed to detect heart conditions. If the AI hallucinates a heartbeat irregularity, incorrect diagnosis could occur, resulting in unnecessary medical interventions and endangering patient safety.
Bias in AI Models
Problems also arise when AI models are based on biased datasets. Previously, Amazon used an AI-based recruitment tool to help hire employees. The AI tool had been trained on a data set that reflected historical and societal inequities which may exist even if normalized by removing those factors. Rather than helping to find the best candidates, the AI inadvertently discriminated against female applicants, systematically rejecting their resumes. Far from identifying the best candidates, the tool perpetuated existing inequities. This example highlights not only the reproduction of real-world biases in AI systems, but also the amplification of those biases, potentially worsening future outcomes. The absence of comprehensive regulations around AI can exacerbate these mistakes, leaving businesses without clear directives on prevention.
As a result of hallucinations and biases, businesses can face lawsuits for negligence or discrimination, resulting in fines. Financial losses may arise from erroneous decisions and missed opportunities, while an untrustworthy AI model can drive customers away. These issues could leave organizations deeming AI as too risky, abandoning projects they had planned. In cases where uses of AI would increase productivity, these projects being dropped might leave staff with extra work.
RAG to the Rescue
Despite the inherent challenges, AI offers significant opportunities for businesses. By adopting the appropriate tools, models, and best practices, companies can effectively address potential issues and fully leverage AI's capabilities. Techniques like retrieval-augmented generation (RAG) are instrumental in tackling problems related to bias, fairness, and hallucinations. RAG models integrate retrieval mechanisms that enable access to extensive, diverse, and pertinent data. Leveraging a wide array of sources helps these models reduce the impact of biases found in smaller or more restricted datasets.
RAG models also excel at generating responses that are grounded in verifiable information. This can eliminate AI hallucinations, providing data inputs that are enriched with context-specific information and retrieved from reliable sources. This means RAG models can be fine-tuned for specific tasks or use-cases, benefiting users by providing information that is unique to their situation. This is especially useful for businesses that don’t have the time or budget to retrain AI models with domain-specific datasets.
In the recruiting example above, RAG can help inform the model with newer hiring guidelines, HR policies and equal employment opportunity laws, ensuring a broad and balanced approach for all candidates to receive fair and equal treatment.
Practical Applications of RAG
Beyond retrieving relevant information, businesses also benefit from RAG models’ ability to generate a natural response. Interactions with these models will generally be more conversational and user friendly. This is particularly useful for customer facing applications. RAG models should form a key part of a modern data approach. To enhance their effectiveness, RAG models require access to real-time data to ensure that information is as fresh and as accurate as possible. They should also be paired with an operational data store that holds information in high-dimensional mathematical vectors. Models can therefore convert a user’s query into numerical vectors when asked, allowing the AI to respond to relevant text inquiries even if they don’t precisely match the original terms or phrases.
By using real-time data and databases that operate in vectors, AI model outputs remain up-to-date, reducing the risk of outdated information leading to hallucinations.
Heading Towards a Brighter Future
As we embark on the journey towards AI’s widespread adoption, organizations must be aware of the consequences of AI gone wrong. A comprehensive approach to AI is crucial. This paves the way for ethical, fair, and secure AI systems that enhance productivity and personalization without propagating misinformation. By prioritizing responsible AI practices, such as employing RAG models, businesses ensure AI remains a positive force in society, rather than something to be feared.
![Latanskiy Nick Latanskiy Nick]() Latanskiy Nick
2024-05-30
Latanskiy Nick
2024-05-30
-
![Compliance and Cybersecurity in the Age of AI Compliance and Cybersecurity in the Age of AI]() Editor’s Choice
Compliance and Cybersecurity in the Age of AI
Artificial Intelligence is dramatically transforming the business landscape. It streamlines operations, provides critical insights, and empowers businesses to make data-driven decisions efficiently. Utilizing machine learning, predictive analytics, and automation, AI aids in spotting trends, projecting sales, and optimizing supply chains. This results in heightened productivity and enhanced business performance. However, it does come with certain challenges.
Ransomware Threats and AI
We discussed the impact of AI on cybersecurity with Matt Hillary, Vice President of Security and CISO at Drata. According to Hillary, AI is significantly increasing the ransomware threat. Traditional strategies for propagating ransomware rely heavily on social engineering tactics such as phishing and exploiting weaknesses in externally accessible systems like Virtual Private Network (VPN) endpoints and exposed Remote Desktop Protocol (RDP). AI is enabling cyber attackers to produce highly sophisticated deceptive messages, making them more tempting to the unaware user.
Cybercriminals are leveraging AI to improve various facets of their activities, including reconnaissance and coding, which strengthens their exploitation vectors. By using AI, threat actors can efficiently analyze extensive datasets to identify weaknesses in an organization’s external systems and create tailored exploits, whether by exploiting known vulnerabilities or uncovering new ones.
Defensive and Preventative AI Solutions
On the flip side, AI is also enhancing defensive and preventative solutions in cybersecurity. AI-driven systems can sift through extensive datasets to identify patterns that signal potential cyber threats, such as malware, phishing schemes, and irregular network behavior. Large Language Models (LLMs) can identify indicators of compromise or other threats more quickly and accurately than traditional or manual review methods, allowing for a faster response and mitigation.
AI models can also review activities to understand the normal behavior of users and systems within a network, enabling them to detect deviations that may indicate a security incident. This method is especially useful for detecting insider threats and complex attacks that manage to bypass conventional signature-based detection systems.
Automating Governance and Compliance
AI tools have the potential to significantly enhance governance and compliance with evolving regulations and industry standards. By continuously monitoring systems and detecting anomalies, AI can respond to indicators of security incidents or misconfigurations that could result in non-compliance. These tools help organizations stay current and compliant by keeping up with evolving governance regulations in real-time.
Moreover, AI algorithms can analyze vast amounts of regulatory data, reducing the risk of human error associated with manual efforts. This leads to more accurate assessments of compliance status and reduces the likelihood of regulatory violations, providing a more robust compliance framework.
Best Practices for Protecting Against AI Threats
To protect against evolving AI threats, leaders should implement several practical and best practices. Comprehensive education for cybersecurity teams is crucial to effectively secure AI used by employees and AI integrated into existing platforms or systems. This education should cover not only the application but also the underlying technology driving AI capabilities.
Organizations should deploy phishing-resistant authentication methods to safeguard against phishing attacks targeting authentication tokens used for accessing environments. Additionally, policies, training, and automated mechanisms should be established to equip team members with the knowledge to defend against social engineering attacks.
Consistently strengthening the organization’s internet-facing perimeters and internal networks is essential to diminish the effectiveness of such attacks, ensuring a more secure environment against AI-driven threats.
Ethical Considerations and Practical Safety Actions
Ethical considerations are paramount when it comes to AI. Companies should establish governance structures and processes to oversee AI development, deployment, and usage. This includes appointing individuals or committees responsible for monitoring ethical compliance and ensuring alignment with organizational values. These governance structures should be extensively documented and understood across the organization.
Transparency is also crucial. Organizations should document AI algorithms, data sources, and decision-making processes, ensuring that stakeholders understand how AI systems make decisions and their potential impacts on individuals and society. At Drata, responsible AI principles have been developed to encourage robust, trusted, ethical governance while maintaining a strong security posture.
Key principles include privacy by design, which involves using anonymized datasets to safeguard privacy with strict access control and encryption protocols, alongside synthetic data generation to simulate compliance scenarios. Fairness and inclusivity are promoted by removing inherent biases through detailed curation and continuous monitoring of models to ensure no unfair outcomes. Safety and reliability are ensured through rigorous testing and 360-degree human oversight, providing users with total confidence in AI solutions.
The Future of AI Threats
The future holds both challenges and opportunities in the realm of AI threats. With increasing accessibility and potency of AI, malicious actors will inevitably exploit it to orchestrate highly targeted, automated, and elusive cyberattacks across multiple domains. These attacks will evolve in real-time, enabling them to evade traditional detection methods.
Additionally, the rise of AI-generated deep-fakes and misinformation poses significant threats to individuals, organizations, and the democratic process. Fake visuals, audio, and text are becoming increasingly sophisticated, making it difficult to distinguish between fact and fiction.
Advanced AI-Driven Security Solutions
Despite the challenges, the future of advanced AI-driven security solutions is promising. AI will bolster cybersecurity resilience through proactive threat intelligence, predictive analytics, and adaptive security controls. By using AI to foresee and adjust to emerging threats, organizations can maintain a proactive stance against cyber criminals, mitigating the impact of attacks.
Third-party risk management is also critical in addressing AI-powered vulnerabilities. Security teams need comprehensive tools for identifying, assessing, and continuously monitoring risks, integrating them with internal risk profiles. This holistic approach ensures a unified, clear view of potential exposures across the entire organization, effectively managing third-party risks associated with AI.
Editor’s Choice
Compliance and Cybersecurity in the Age of AI
Artificial Intelligence is dramatically transforming the business landscape. It streamlines operations, provides critical insights, and empowers businesses to make data-driven decisions efficiently. Utilizing machine learning, predictive analytics, and automation, AI aids in spotting trends, projecting sales, and optimizing supply chains. This results in heightened productivity and enhanced business performance. However, it does come with certain challenges.
Ransomware Threats and AI
We discussed the impact of AI on cybersecurity with Matt Hillary, Vice President of Security and CISO at Drata. According to Hillary, AI is significantly increasing the ransomware threat. Traditional strategies for propagating ransomware rely heavily on social engineering tactics such as phishing and exploiting weaknesses in externally accessible systems like Virtual Private Network (VPN) endpoints and exposed Remote Desktop Protocol (RDP). AI is enabling cyber attackers to produce highly sophisticated deceptive messages, making them more tempting to the unaware user.
Cybercriminals are leveraging AI to improve various facets of their activities, including reconnaissance and coding, which strengthens their exploitation vectors. By using AI, threat actors can efficiently analyze extensive datasets to identify weaknesses in an organization’s external systems and create tailored exploits, whether by exploiting known vulnerabilities or uncovering new ones.
Defensive and Preventative AI Solutions
On the flip side, AI is also enhancing defensive and preventative solutions in cybersecurity. AI-driven systems can sift through extensive datasets to identify patterns that signal potential cyber threats, such as malware, phishing schemes, and irregular network behavior. Large Language Models (LLMs) can identify indicators of compromise or other threats more quickly and accurately than traditional or manual review methods, allowing for a faster response and mitigation.
AI models can also review activities to understand the normal behavior of users and systems within a network, enabling them to detect deviations that may indicate a security incident. This method is especially useful for detecting insider threats and complex attacks that manage to bypass conventional signature-based detection systems.
Automating Governance and Compliance
AI tools have the potential to significantly enhance governance and compliance with evolving regulations and industry standards. By continuously monitoring systems and detecting anomalies, AI can respond to indicators of security incidents or misconfigurations that could result in non-compliance. These tools help organizations stay current and compliant by keeping up with evolving governance regulations in real-time.
Moreover, AI algorithms can analyze vast amounts of regulatory data, reducing the risk of human error associated with manual efforts. This leads to more accurate assessments of compliance status and reduces the likelihood of regulatory violations, providing a more robust compliance framework.
Best Practices for Protecting Against AI Threats
To protect against evolving AI threats, leaders should implement several practical and best practices. Comprehensive education for cybersecurity teams is crucial to effectively secure AI used by employees and AI integrated into existing platforms or systems. This education should cover not only the application but also the underlying technology driving AI capabilities.
Organizations should deploy phishing-resistant authentication methods to safeguard against phishing attacks targeting authentication tokens used for accessing environments. Additionally, policies, training, and automated mechanisms should be established to equip team members with the knowledge to defend against social engineering attacks.
Consistently strengthening the organization’s internet-facing perimeters and internal networks is essential to diminish the effectiveness of such attacks, ensuring a more secure environment against AI-driven threats.
Ethical Considerations and Practical Safety Actions
Ethical considerations are paramount when it comes to AI. Companies should establish governance structures and processes to oversee AI development, deployment, and usage. This includes appointing individuals or committees responsible for monitoring ethical compliance and ensuring alignment with organizational values. These governance structures should be extensively documented and understood across the organization.
Transparency is also crucial. Organizations should document AI algorithms, data sources, and decision-making processes, ensuring that stakeholders understand how AI systems make decisions and their potential impacts on individuals and society. At Drata, responsible AI principles have been developed to encourage robust, trusted, ethical governance while maintaining a strong security posture.
Key principles include privacy by design, which involves using anonymized datasets to safeguard privacy with strict access control and encryption protocols, alongside synthetic data generation to simulate compliance scenarios. Fairness and inclusivity are promoted by removing inherent biases through detailed curation and continuous monitoring of models to ensure no unfair outcomes. Safety and reliability are ensured through rigorous testing and 360-degree human oversight, providing users with total confidence in AI solutions.
The Future of AI Threats
The future holds both challenges and opportunities in the realm of AI threats. With increasing accessibility and potency of AI, malicious actors will inevitably exploit it to orchestrate highly targeted, automated, and elusive cyberattacks across multiple domains. These attacks will evolve in real-time, enabling them to evade traditional detection methods.
Additionally, the rise of AI-generated deep-fakes and misinformation poses significant threats to individuals, organizations, and the democratic process. Fake visuals, audio, and text are becoming increasingly sophisticated, making it difficult to distinguish between fact and fiction.
Advanced AI-Driven Security Solutions
Despite the challenges, the future of advanced AI-driven security solutions is promising. AI will bolster cybersecurity resilience through proactive threat intelligence, predictive analytics, and adaptive security controls. By using AI to foresee and adjust to emerging threats, organizations can maintain a proactive stance against cyber criminals, mitigating the impact of attacks.
Third-party risk management is also critical in addressing AI-powered vulnerabilities. Security teams need comprehensive tools for identifying, assessing, and continuously monitoring risks, integrating them with internal risk profiles. This holistic approach ensures a unified, clear view of potential exposures across the entire organization, effectively managing third-party risks associated with AI.
![Latanskiy Nick Latanskiy Nick]() Latanskiy Nick
2024-05-30
Latanskiy Nick
2024-05-30
-
![How to Fix the V Rising Authentication Error How to Fix the V Rising Authentication Error]() Editor’s Choice
How to Fix the V Rising Authentication Error
Even though V Rising was released after years of early access, players can still find errors in it. And some incredibly annoying ones can ruin your gaming experience. Therefore, we will tell you how to fix the Authentication Error in V Rising in this guide. After the full release, this error is quite rare in the game. However, if you notice it on your screen, you should not be upset, as there are several ways to get rid of it quickly.
Understanding the Authentication Error
First, you need to know that the Authentication Error in V Rising can happen for several reasons, namely problems with connecting to the server or the server being overloaded with players. As a result, all you can do is leave the game or return to the main menu. Fortunately, you can fix the Authentication Error in V Rising quickly by using one of the methods below:
Check Server Status
Like any other multiplayer game, V Rising sometimes may have server issues. To check this, you just need to visit the X page of the game. If the servers are down, you will have to wait for the developers to fix it. If there are no messages about server issues, then the problem is on your side.
Check the Server for Player Overload
Players just need to connect to another V Rising server to do this. Of course, your progress will stay in the new world. But if you can connect to it without the Authentication Error in V Rising, then you just have to wait until the number of players on your main server decreases.
Check Your Internet Connection
In rare cases, an Authentication Error may occur in V Rising due to a bad internet connection. To check this, you need to try running another online game. If no similar errors occur, move on to the following method.
Update or Reinstall V Rising
When developers release new patches, you should always update V Rising before starting the game. It will help you avoid plenty of errors and bugs. Another viable option is to reinstall the game. Even though this is a trivial and simple way, it often helps eliminate annoying problems, including Authentication Error in V Rising.
Steps to Ensure Smooth Gameplay
Ensuring smooth gameplay in V Rising involves more than just addressing the Authentication Error. Here are some additional steps to enhance your overall experience:
Optimize Game Settings
Adjusting in-game settings can significantly improve performance. Lowering the graphics quality, disabling unnecessary features, and tweaking network settings can contribute to a smoother experience. Also, regularly updating your graphics drivers can prevent crashes and errors.
Maintain a Stable Internet Connection
A stable internet connection is crucial for any online game. Ensure that your router firmware is updated, and consider using a wired connection for a more consistent network experience. Additionally, avoid bandwidth-heavy activities like streaming while gaming.
Regular System Maintenance
Regularly updating your operating system and drivers can prevent compatibility issues with V Rising. It’s also wise to perform routine system checks for malware and unnecessary background applications that may consume resources.
Community and Developer Support
Joining V Rising’s community forums and following developer updates can keep you informed about common issues and their fixes. Developers often release hotfixes and patches based on community feedback, so staying engaged can be beneficial.
When All Else Fails
If none of these methods work, all you can do is wait for the update from the developers. They still release patches with bug fixes from time to time. Patience is key, and keeping an eye on official announcements will keep you prepared for upcoming fixes.
Contacting Support
If you’ve exhausted all troubleshooting steps and still face the Authentication Error, consider reaching out to V Rising’s support team. Providing detailed information about your issue can expedite the resolution process.
Re-Evaluating Your Setup
Sometimes, persistent issues might indicate a deeper problem with your hardware or software setup. Re-evaluating your gaming setup, including hardware specifications and software configurations, might reveal underlying issues that need addressing.
Conclusion
While encountering the Authentication Error in V Rising can be frustrating, various strategies can help resolve the issue. By checking server status, ensuring a stable internet connection, updating the game, and maintaining your system, you can enhance your gaming experience. Remember, staying informed through community and developer channels is crucial for timely updates and fixes. If all else fails, reaching out to support and re-evaluating your setup may provide a solution. Happy gaming!
Editor’s Choice
How to Fix the V Rising Authentication Error
Even though V Rising was released after years of early access, players can still find errors in it. And some incredibly annoying ones can ruin your gaming experience. Therefore, we will tell you how to fix the Authentication Error in V Rising in this guide. After the full release, this error is quite rare in the game. However, if you notice it on your screen, you should not be upset, as there are several ways to get rid of it quickly.
Understanding the Authentication Error
First, you need to know that the Authentication Error in V Rising can happen for several reasons, namely problems with connecting to the server or the server being overloaded with players. As a result, all you can do is leave the game or return to the main menu. Fortunately, you can fix the Authentication Error in V Rising quickly by using one of the methods below:
Check Server Status
Like any other multiplayer game, V Rising sometimes may have server issues. To check this, you just need to visit the X page of the game. If the servers are down, you will have to wait for the developers to fix it. If there are no messages about server issues, then the problem is on your side.
Check the Server for Player Overload
Players just need to connect to another V Rising server to do this. Of course, your progress will stay in the new world. But if you can connect to it without the Authentication Error in V Rising, then you just have to wait until the number of players on your main server decreases.
Check Your Internet Connection
In rare cases, an Authentication Error may occur in V Rising due to a bad internet connection. To check this, you need to try running another online game. If no similar errors occur, move on to the following method.
Update or Reinstall V Rising
When developers release new patches, you should always update V Rising before starting the game. It will help you avoid plenty of errors and bugs. Another viable option is to reinstall the game. Even though this is a trivial and simple way, it often helps eliminate annoying problems, including Authentication Error in V Rising.
Steps to Ensure Smooth Gameplay
Ensuring smooth gameplay in V Rising involves more than just addressing the Authentication Error. Here are some additional steps to enhance your overall experience:
Optimize Game Settings
Adjusting in-game settings can significantly improve performance. Lowering the graphics quality, disabling unnecessary features, and tweaking network settings can contribute to a smoother experience. Also, regularly updating your graphics drivers can prevent crashes and errors.
Maintain a Stable Internet Connection
A stable internet connection is crucial for any online game. Ensure that your router firmware is updated, and consider using a wired connection for a more consistent network experience. Additionally, avoid bandwidth-heavy activities like streaming while gaming.
Regular System Maintenance
Regularly updating your operating system and drivers can prevent compatibility issues with V Rising. It’s also wise to perform routine system checks for malware and unnecessary background applications that may consume resources.
Community and Developer Support
Joining V Rising’s community forums and following developer updates can keep you informed about common issues and their fixes. Developers often release hotfixes and patches based on community feedback, so staying engaged can be beneficial.
When All Else Fails
If none of these methods work, all you can do is wait for the update from the developers. They still release patches with bug fixes from time to time. Patience is key, and keeping an eye on official announcements will keep you prepared for upcoming fixes.
Contacting Support
If you’ve exhausted all troubleshooting steps and still face the Authentication Error, consider reaching out to V Rising’s support team. Providing detailed information about your issue can expedite the resolution process.
Re-Evaluating Your Setup
Sometimes, persistent issues might indicate a deeper problem with your hardware or software setup. Re-evaluating your gaming setup, including hardware specifications and software configurations, might reveal underlying issues that need addressing.
Conclusion
While encountering the Authentication Error in V Rising can be frustrating, various strategies can help resolve the issue. By checking server status, ensuring a stable internet connection, updating the game, and maintaining your system, you can enhance your gaming experience. Remember, staying informed through community and developer channels is crucial for timely updates and fixes. If all else fails, reaching out to support and re-evaluating your setup may provide a solution. Happy gaming!
![Latanskiy Nick Latanskiy Nick]() Latanskiy Nick
2024-05-28
Latanskiy Nick
2024-05-28
Tips & Guides
![Fortnite: Building Techniques for Winning More Battles Fortnite: Building Techniques for Winning More Battles]() Tips & Guides
Fortnite: Building Techniques for Winning More Battles
Fortnite Battle Royale stands out from the crowd of online multiplayer games due to its distinctive building mechanics. This wildly popular game has captivated players worldwide, offering a unique blend of shooter and builder gameplay styles. Instead of simply relying on finding the perfect weapon to take out your opponents, Fortnite adds an extra layer of strategy by enabling players to construct various structures in the gaming landscape.
Building in Fortnite serves several tactical purposes: it can provide defenses to shield you from enemy attacks, form offensive platforms from which to stage your assaults, and aid in quick movements across the map. A simple wooden wall or towering fortress can mean the difference between victory and defeat. This game element goes far beyond mere survival; It takes on a crucial part in orchestrating your comprehensive combat tactics.
At first glance, the art of building in Fortnite might seem straightforward - you just need to select the right materials and start constructing, right? However, the intricacies lie in the execution. Effective building requires a keen sense of timing, a high degree of precision, and, most importantly, strategic thinking. The layout structure, the choice of materials, and even the decision of when and where to build - these are all factors that contribute to your overall gameplay.
By refining your building techniques, you can significantly improve your survival chances in the game. A player skilled in building can quickly create structures to outmaneuver opponents, gaining the upper hand in firefights and increasing their odds of emerging victorious. Mastering diverse building strategies allows you to adapt to any situation you encounter, turning potential threats into opportunities for victory.
In the proceeding paragraphs, we shall delve into six advanced building methods to improve your gameplay. By implementing these techniques, you can elevate your Fortnite skills to the next level, ensuring that you always have a few tricks up your sleeve for your next battle.
1. Quick Fort Building
The art of building in Fortnite commences with understanding the nuts and bolts of constructing a simple 1x1 fort. As a straightforward and basic building technique, quick fort building serves as your entry point into the realm of Fortnite construction strategies. Its objective is to provide players with a swift and easy solution to defend against enemy fire and gain an advantageous position in battle.
As the name suggests, the 1x1 fort is a compact structure, serving as a protective shell against enemy attacks. The beauty of this quick fort lies in its simplicity and efficiency. When you find yourself in the thick of battle with bullets flying around, this structure can provide you with the much-needed protection to shield yourself from direct hits.
The 1x1 fort is not just about defense; it provides an excellent vantage point to observe the battlefield and spot adversaries. From the safety of your fort, you can gather crucial information about the enemy's location and game plan. Your fort situates you higher than ground level, giving you an overview of the unfolding battle and the positions of your competitors.
Building a quick fort is a straightforward process but requires speed and precision. The first step is laying down four walls, forming a closed square around you. Then, inside this box, you need to add stairs. The stairs elevate you, enhancing your viewing range and offering a platform to return fire. To cap it off, do not forget to add a roof on top to secure yourself from attacks from above.
It is essential to practice this technique under low-pressure conditions. Doing so will allow you to enhance your building speed, reducing the time it takes to create a fort when you're in the heart of the battle. Your goal should be to construct the fort so swiftly that it becomes second nature. The quick fort, given its utility and ease of construction, can be your reliable ally in the unpredictable and volatile world of Fortnite.
2. Ramp Rush
Ramp rushing is an offensive building technique employed to close the gap between you and your enemy. It involves building ramp structures towards the enemy; the height advantage can help you gain better aim. However, it's crucial to reinforce your ramps with walls to prevent the enemy from shooting down your structure. Remember, building with wooden materials may be quicker but also less durable than stone or metal, so choose your materials wisely depending on the situation.
3. Double Ramping
Double ramping takes ramp rushing to the next level by adding an extra layer of protection. This implies building two ramps parallel to each other, reinforced by walls for better defense. This strategy allows you to gain both height and pressure on your opponents while minimizing your own risks. Double ramping can consume more materials compared to a single ramp rush, but the additional safety it provides is often worth the expenditure.
4. Waterfalling
Waterfalling is a crucial skill when you need to descend from great heights quickly and safely. This technique involves building ramps or floors beneath you as you fall, mitigating fall damage. Beginners may struggle with this technique as it requires precise timing and fast reactions. However, mastering waterfalling can be a literal lifesaver in many Fortnite engagements.
5. Pyramid and Cone Jumps
Pyramid or cone jumps provide a sneaky way of outsmarting and outrunning your opponents by confusing them with unexpected moves. A cone jump involves creating a pyramid structure over your ramp and then jumping on the pyramid, hence breaking the linear direction of your ramp rush. This tactic is extremely useful when you want to shift direction quickly without sacrificing safety or height advantage.
6. High Ground Retake
High Ground Retake is the art of stealing the high-ground advantage from your opponent through strategic building. This technique involves several steps, including building ramps above you, boxing yourself in, and constructing a staircase to ascend further. This technique may seem complex at first, but mastering it can provide a significant advantage, especially in late-game build fights.
Conclusion
Advanced building techniques in Fortnite Battle Royale are game-changing skills that separate average players from pros. Implementing these methods into your gaming strategy can elevate your attack and defense skills. This will always keep you one pace ahead of your competitors. Bear in mind that to excel as a professional architect in Fortnite, continuous practice, endurance, and tactical cognition are essential. Enjoy assembling and conquering!
Tips & Guides
Fortnite: Building Techniques for Winning More Battles
Fortnite Battle Royale stands out from the crowd of online multiplayer games due to its distinctive building mechanics. This wildly popular game has captivated players worldwide, offering a unique blend of shooter and builder gameplay styles. Instead of simply relying on finding the perfect weapon to take out your opponents, Fortnite adds an extra layer of strategy by enabling players to construct various structures in the gaming landscape.
Building in Fortnite serves several tactical purposes: it can provide defenses to shield you from enemy attacks, form offensive platforms from which to stage your assaults, and aid in quick movements across the map. A simple wooden wall or towering fortress can mean the difference between victory and defeat. This game element goes far beyond mere survival; It takes on a crucial part in orchestrating your comprehensive combat tactics.
At first glance, the art of building in Fortnite might seem straightforward - you just need to select the right materials and start constructing, right? However, the intricacies lie in the execution. Effective building requires a keen sense of timing, a high degree of precision, and, most importantly, strategic thinking. The layout structure, the choice of materials, and even the decision of when and where to build - these are all factors that contribute to your overall gameplay.
By refining your building techniques, you can significantly improve your survival chances in the game. A player skilled in building can quickly create structures to outmaneuver opponents, gaining the upper hand in firefights and increasing their odds of emerging victorious. Mastering diverse building strategies allows you to adapt to any situation you encounter, turning potential threats into opportunities for victory.
In the proceeding paragraphs, we shall delve into six advanced building methods to improve your gameplay. By implementing these techniques, you can elevate your Fortnite skills to the next level, ensuring that you always have a few tricks up your sleeve for your next battle.
1. Quick Fort Building
The art of building in Fortnite commences with understanding the nuts and bolts of constructing a simple 1x1 fort. As a straightforward and basic building technique, quick fort building serves as your entry point into the realm of Fortnite construction strategies. Its objective is to provide players with a swift and easy solution to defend against enemy fire and gain an advantageous position in battle.
As the name suggests, the 1x1 fort is a compact structure, serving as a protective shell against enemy attacks. The beauty of this quick fort lies in its simplicity and efficiency. When you find yourself in the thick of battle with bullets flying around, this structure can provide you with the much-needed protection to shield yourself from direct hits.
The 1x1 fort is not just about defense; it provides an excellent vantage point to observe the battlefield and spot adversaries. From the safety of your fort, you can gather crucial information about the enemy's location and game plan. Your fort situates you higher than ground level, giving you an overview of the unfolding battle and the positions of your competitors.
Building a quick fort is a straightforward process but requires speed and precision. The first step is laying down four walls, forming a closed square around you. Then, inside this box, you need to add stairs. The stairs elevate you, enhancing your viewing range and offering a platform to return fire. To cap it off, do not forget to add a roof on top to secure yourself from attacks from above.
It is essential to practice this technique under low-pressure conditions. Doing so will allow you to enhance your building speed, reducing the time it takes to create a fort when you're in the heart of the battle. Your goal should be to construct the fort so swiftly that it becomes second nature. The quick fort, given its utility and ease of construction, can be your reliable ally in the unpredictable and volatile world of Fortnite.
2. Ramp Rush
Ramp rushing is an offensive building technique employed to close the gap between you and your enemy. It involves building ramp structures towards the enemy; the height advantage can help you gain better aim. However, it's crucial to reinforce your ramps with walls to prevent the enemy from shooting down your structure. Remember, building with wooden materials may be quicker but also less durable than stone or metal, so choose your materials wisely depending on the situation.
3. Double Ramping
Double ramping takes ramp rushing to the next level by adding an extra layer of protection. This implies building two ramps parallel to each other, reinforced by walls for better defense. This strategy allows you to gain both height and pressure on your opponents while minimizing your own risks. Double ramping can consume more materials compared to a single ramp rush, but the additional safety it provides is often worth the expenditure.
4. Waterfalling
Waterfalling is a crucial skill when you need to descend from great heights quickly and safely. This technique involves building ramps or floors beneath you as you fall, mitigating fall damage. Beginners may struggle with this technique as it requires precise timing and fast reactions. However, mastering waterfalling can be a literal lifesaver in many Fortnite engagements.
5. Pyramid and Cone Jumps
Pyramid or cone jumps provide a sneaky way of outsmarting and outrunning your opponents by confusing them with unexpected moves. A cone jump involves creating a pyramid structure over your ramp and then jumping on the pyramid, hence breaking the linear direction of your ramp rush. This tactic is extremely useful when you want to shift direction quickly without sacrificing safety or height advantage.
6. High Ground Retake
High Ground Retake is the art of stealing the high-ground advantage from your opponent through strategic building. This technique involves several steps, including building ramps above you, boxing yourself in, and constructing a staircase to ascend further. This technique may seem complex at first, but mastering it can provide a significant advantage, especially in late-game build fights.
Conclusion
Advanced building techniques in Fortnite Battle Royale are game-changing skills that separate average players from pros. Implementing these methods into your gaming strategy can elevate your attack and defense skills. This will always keep you one pace ahead of your competitors. Bear in mind that to excel as a professional architect in Fortnite, continuous practice, endurance, and tactical cognition are essential. Enjoy assembling and conquering!
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-08-06
Ethan Blackstone
2024-08-06
-
![Character Guide: Exploring the Champions of League of Legends Character Guide: Exploring the Champions of League of Legends]() Tips & Guides
Character Guide: Exploring the Champions of League of Legends
The world of gaming is brimming with numerous enthralling experiences, but few can hold a candle to the captivating scenarios laid out in the landscape of League of Legends (LoL). Its widespread acceptance among gaming enthusiasts worldwide and the electrifying gameplay that keeps players on the edge of their seats are largely attributed to its diverse lineup of champions.
From their distinctive abilities to their individual strategic significance, each champion in LoL adds a new dimension to the gameplay. They each possess unique abilities that can be wielded in the game, laying the foundation for an endlessly versatile variety of dynamics in each battle. With each of them fulfilling unique roles that they're tailored for, champions bring specific tactics and strategies to the table, making the gameplay ever-engrossing.
As you get accustomed to the thrilling realm of LoL, an in-depth knowledge of the champions becomes indispensable. This comprehensive guide is designed to provide you with a deeper understanding of the champions, shedding light on their unique abilities, roles, and tactical uses. Furthermore, we'll delve into the various categories champions fall into and the strategic value each holds in the game.
But awareness cannot replace skill. The actual challenge lies in mastering these champions. Every champion requires a different approach and strategy, and understanding alone won't quite cut it. So, we intend to provide tips on mastering them as well, ensuring you can take full advantage of the potential each champion holds.
Understanding the Unique Abilities of Champions
In the exhilarating world of League of Legends, each champion brings a unique personality to the battlefield. And the key factor defining this personality is the distinct set of abilities that each champion possesses. It's these special abilities that carve out the champion's playstyle, laying the groundwork for their approach and tactics when venturing into the battlefield.
The abilities of champions demonstrate a diverse range, each serving different purposes in the match. They are typically categorized as 'Passive,' 'Q,' 'W,' 'E,' and 'Ultimate.' Understanding these categories is critical to comprehending a champion's capabilities and knowing how to strategize effectively during the game.
The 'Passive' ability is a champion's fundamental attribute, which is inherently enabled during the game. It does not require any command to activate and remains operational, emphasizing the inherent nature or the core strength of the champion throughout.
The 'Q,' 'W,' and 'E' signify the basic abilities that every champion possesses. These abilities play a significant role during the fiercely fought battles. Choose the right moments to deploy and upgrade these abilities, for they hold the potential to shift the balance of the game. The upgrade of these abilities happens during the course of the match, progressively increasing the champion's power and tactics.
Above all, we have the 'Ultimate' ability - the ace up the champion's sleeve. This ability is the champion's strongest asset and, thus, is available only after reaching a particular level. Unleashing the Ultimate ability can turn the tide of the match, making it a valuable weapon to wield at the right moment.
Roles of Champions in Gameplay
While each champion in League of Legends brings unique abilities to the table, they are also defined by the roles they play within the gaming environment. These roles, distinguished by a versatile range of objectives and skills, are crucial to understanding and utilizing the champions to their fullest potential. The primary roles we encounter within the game are 'Attack Damage Carry (ADC),' 'Support,' 'Mid,' 'Top,' and 'Jungle.'
The ADC, or 'Attack Damage Carry,' embodies a powerful figure in the gaming field. Often paired with the Support, their task is to deal notable damage, especially as the game reaches its later stages. Their power grows gradually through the game, and they are the cornerstone of the team's offensive strategies when they reach their peak power level at the end of the game.
The 'Support' champions, as the name aptly suggests, are the team's backbone. Their primary objective is to assist the team in a multitude of ways, but often, their prime responsibility lies in safeguarding the ADC. They contain and mitigate threats to the ADC, enabling them to wreak havoc upon opposing teams unhindered.
'Mid' champions take charge of the mid-lane, a position characterized by independent gameplay. They typically involve champions capable of handling themselves solo, holding the lane steady. The mid-champions can often shift the dynamics of the game through their individual performance in the mid-lane.
'Top' champions, akin to the stalwart defenders in a team, operate largely in isolation from the team. The characteristic feature of their gameplay is their gritty resilience and the ability to soak up damage. Their hardiness allows them to withstand substantial onslaughts, making them formidable opponents in their own right.
Last but hardly least, 'Jungle' champions, much like wildcards in a set, operate without being tied down to a particular lane. They wander the areas between lanes, aptly known as the "jungle," rendering assistance where needed. Their role is fluid and often involves counteracting enemy strategies, providing Support, and seizing opportunities across the game map.
Classification of Champions
Further, champions are classified based on their specific strengths and playing style. The classifications are 'Tank,' 'Mage,' 'Fighter,' 'Assassin,' 'Marksman,' and 'Support.' Tank champions have high durability and crowd control abilities, mages are magic damage dealers, and fighters are versatile champions who can both deal and take damage. Assassins specialize in damaging specific targets, marksman champions deal consistent damage from a range, and support champions have abilities to protect and enhance their team.
Getting to Grips with Strategizing
Understanding the facets of champions is not enough; knowing how to use them strategically is key to mastering League of Legends. Each champion is unique, and mastering them requires understanding their strengths and weaknesses. Players have to customize their gameplay according to the champion they use and adapt to their chosen champion's abilities. A strategic approach to each champion's abilities will significantly enhance your game.
Tips to Master Champions
Mastering a champion requires understanding their abilities and also their roles in the game. Start with understanding the champion's abilities and how you can use them during gameplay. Use tutorials and guides to understand how to play the champion efficiently. Practice using the abilities of the champion in various situations during the game. Try to learn one champion at a time and understand all loopholes and gameplay strategies with that champion before moving to the next.
Final Words
League of Legends champions, with their diverse abilities and roles, add significant strategic depth to the gameplay. Regardless if you are an experienced gamer wanting to boost your skills or a beginner eager to dip your toes, grasping the complexities and variety of these champions will prove valuable. Remember, the key to mastering any champion is through understanding, strategic gameplay, and practice. So, dive into the captivating world of LoL and embrace the exciting diversity offered by its champions!
Tips & Guides
Character Guide: Exploring the Champions of League of Legends
The world of gaming is brimming with numerous enthralling experiences, but few can hold a candle to the captivating scenarios laid out in the landscape of League of Legends (LoL). Its widespread acceptance among gaming enthusiasts worldwide and the electrifying gameplay that keeps players on the edge of their seats are largely attributed to its diverse lineup of champions.
From their distinctive abilities to their individual strategic significance, each champion in LoL adds a new dimension to the gameplay. They each possess unique abilities that can be wielded in the game, laying the foundation for an endlessly versatile variety of dynamics in each battle. With each of them fulfilling unique roles that they're tailored for, champions bring specific tactics and strategies to the table, making the gameplay ever-engrossing.
As you get accustomed to the thrilling realm of LoL, an in-depth knowledge of the champions becomes indispensable. This comprehensive guide is designed to provide you with a deeper understanding of the champions, shedding light on their unique abilities, roles, and tactical uses. Furthermore, we'll delve into the various categories champions fall into and the strategic value each holds in the game.
But awareness cannot replace skill. The actual challenge lies in mastering these champions. Every champion requires a different approach and strategy, and understanding alone won't quite cut it. So, we intend to provide tips on mastering them as well, ensuring you can take full advantage of the potential each champion holds.
Understanding the Unique Abilities of Champions
In the exhilarating world of League of Legends, each champion brings a unique personality to the battlefield. And the key factor defining this personality is the distinct set of abilities that each champion possesses. It's these special abilities that carve out the champion's playstyle, laying the groundwork for their approach and tactics when venturing into the battlefield.
The abilities of champions demonstrate a diverse range, each serving different purposes in the match. They are typically categorized as 'Passive,' 'Q,' 'W,' 'E,' and 'Ultimate.' Understanding these categories is critical to comprehending a champion's capabilities and knowing how to strategize effectively during the game.
The 'Passive' ability is a champion's fundamental attribute, which is inherently enabled during the game. It does not require any command to activate and remains operational, emphasizing the inherent nature or the core strength of the champion throughout.
The 'Q,' 'W,' and 'E' signify the basic abilities that every champion possesses. These abilities play a significant role during the fiercely fought battles. Choose the right moments to deploy and upgrade these abilities, for they hold the potential to shift the balance of the game. The upgrade of these abilities happens during the course of the match, progressively increasing the champion's power and tactics.
Above all, we have the 'Ultimate' ability - the ace up the champion's sleeve. This ability is the champion's strongest asset and, thus, is available only after reaching a particular level. Unleashing the Ultimate ability can turn the tide of the match, making it a valuable weapon to wield at the right moment.
Roles of Champions in Gameplay
While each champion in League of Legends brings unique abilities to the table, they are also defined by the roles they play within the gaming environment. These roles, distinguished by a versatile range of objectives and skills, are crucial to understanding and utilizing the champions to their fullest potential. The primary roles we encounter within the game are 'Attack Damage Carry (ADC),' 'Support,' 'Mid,' 'Top,' and 'Jungle.'
The ADC, or 'Attack Damage Carry,' embodies a powerful figure in the gaming field. Often paired with the Support, their task is to deal notable damage, especially as the game reaches its later stages. Their power grows gradually through the game, and they are the cornerstone of the team's offensive strategies when they reach their peak power level at the end of the game.
The 'Support' champions, as the name aptly suggests, are the team's backbone. Their primary objective is to assist the team in a multitude of ways, but often, their prime responsibility lies in safeguarding the ADC. They contain and mitigate threats to the ADC, enabling them to wreak havoc upon opposing teams unhindered.
'Mid' champions take charge of the mid-lane, a position characterized by independent gameplay. They typically involve champions capable of handling themselves solo, holding the lane steady. The mid-champions can often shift the dynamics of the game through their individual performance in the mid-lane.
'Top' champions, akin to the stalwart defenders in a team, operate largely in isolation from the team. The characteristic feature of their gameplay is their gritty resilience and the ability to soak up damage. Their hardiness allows them to withstand substantial onslaughts, making them formidable opponents in their own right.
Last but hardly least, 'Jungle' champions, much like wildcards in a set, operate without being tied down to a particular lane. They wander the areas between lanes, aptly known as the "jungle," rendering assistance where needed. Their role is fluid and often involves counteracting enemy strategies, providing Support, and seizing opportunities across the game map.
Classification of Champions
Further, champions are classified based on their specific strengths and playing style. The classifications are 'Tank,' 'Mage,' 'Fighter,' 'Assassin,' 'Marksman,' and 'Support.' Tank champions have high durability and crowd control abilities, mages are magic damage dealers, and fighters are versatile champions who can both deal and take damage. Assassins specialize in damaging specific targets, marksman champions deal consistent damage from a range, and support champions have abilities to protect and enhance their team.
Getting to Grips with Strategizing
Understanding the facets of champions is not enough; knowing how to use them strategically is key to mastering League of Legends. Each champion is unique, and mastering them requires understanding their strengths and weaknesses. Players have to customize their gameplay according to the champion they use and adapt to their chosen champion's abilities. A strategic approach to each champion's abilities will significantly enhance your game.
Tips to Master Champions
Mastering a champion requires understanding their abilities and also their roles in the game. Start with understanding the champion's abilities and how you can use them during gameplay. Use tutorials and guides to understand how to play the champion efficiently. Practice using the abilities of the champion in various situations during the game. Try to learn one champion at a time and understand all loopholes and gameplay strategies with that champion before moving to the next.
Final Words
League of Legends champions, with their diverse abilities and roles, add significant strategic depth to the gameplay. Regardless if you are an experienced gamer wanting to boost your skills or a beginner eager to dip your toes, grasping the complexities and variety of these champions will prove valuable. Remember, the key to mastering any champion is through understanding, strategic gameplay, and practice. So, dive into the captivating world of LoL and embrace the exciting diversity offered by its champions!
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-07-23
Ethan Blackstone
2024-07-23
-
![Six Steps to Safeguarding Your Digital Identity Six Steps to Safeguarding Your Digital Identity]() Tips & Guides
Six Steps to Safeguarding Your Digital Identity
In today's interconnected world, each data breach chips away at our digital privacy. Consider the notable breach at AT&T, which exposed Social Security numbers and other sensitive personal information, making identity theft a significant threat. Following this incident, the proportion of users with compromised Social Security numbers in our databases skyrocketed from less than 1 percent to nearly 15 percent. The risks are exacerbated when such sensitive information becomes publicly accessible on the internet, not just on the dark web, which requires special software to access. These exposures increase the likelihood of misuse and emphasize the necessity of protecting our digital identities.
The Threat of Identity Theft
The most pressing threat from compromised data is identity theft. Malicious actors can access email, bank, and credit card accounts to impersonate victims. This can involve resetting passwords and taking control of phone numbers to bypass text message confirmations. Furthermore, armed with personal details, thieves might take out loans or credit cards in your name, a common and damaging form of identity theft. The danger extends beyond online fraud; stolen information can lead to physical crimes, putting victims at severe risk. Thus, it is vital to take robust measures to protect against these escalating threats.
1. Use Multi-Factor Authentication Everywhere
Implementing multi-factor authentication (MFA) ubiquitously is paramount in reducing the likelihood of account breaches. Some sources suggest that accounts with MFA are 99.9 percent less likely to be compromised. By requiring additional verification steps, such as codes sent via text, email, or USB authenticator keys, MFA significantly enhances account protection and guards against compromised credentials.
2. Manage Password Risk
Ensure the security of your key online and financial accounts by using distinct, robust, and lengthy passwords. Strive for a minimum of 15 characters, incorporating a blend of uppercase and lowercase letters, numbers, and symbols. Utilize password managers to safely store and handle these intricate passwords, as they can also generate strong passwords for you. Furthermore, consider creating a separate "junk" email for non-essential sign-ups, enhancing security and reducing the potential fallout from data breaches on your primary accounts.
3. Use Protection Across Your Devices
Utilize trusted antivirus (AV) software on both desktop and mobile devices. Many people overlook the importance of AV on their phones, yet these devices often store credit card information and provide access to key accounts. Comprehensive AV protection across all devices is crucial for safeguarding sensitive data.
4. Secure Your Surfing
Be mindful of the information you share online and with whom. Use incognito mode when possible, and provide false information where appropriate. A secondary email address, along with an alternate name, date of birth, and security question answers, can further protect your primary accounts. Additionally, when using public Wi-Fi or even at home, a virtual private network (VPN) can mask your location and encrypt data shared on the local network.
5. Regularly Monitor
Continually monitor your online accounts and finances for suspicious activity. Identity Theft Protection services can help keep your data secure by scanning databases for any instances of your email address being linked to data breaches and alerting you to potential security risks. These services provide an efficient way to stay informed about the status of your personal information.
6. Stay Vigilant
Remain alert to phishing and social engineering schemes, including deceptive emails or calls. Verify suspicious communications by contacting the company or organization directly through their official website, avoiding links or contact information provided in unsolicited messages. Reflect on whether you initiated the contact or if someone reached out to you, and proceed with caution if it’s the latter. Despite best efforts, scams can still occur. Promptly reacting to data breaches can prevent further damage and monetary loss. Identifying and addressing online weak spots, such as predictable passwords or a lack of MFA, is essential for robust identity protection.
Adopting a careful and thorough strategy for safeguarding your identity ensures that even if your information is breached, you have preemptive steps implemented to shield your confidential data. These actions help defend your online presence against cyber hazards, offering reassurance in an ever-more connected world.
Tips & Guides
Six Steps to Safeguarding Your Digital Identity
In today's interconnected world, each data breach chips away at our digital privacy. Consider the notable breach at AT&T, which exposed Social Security numbers and other sensitive personal information, making identity theft a significant threat. Following this incident, the proportion of users with compromised Social Security numbers in our databases skyrocketed from less than 1 percent to nearly 15 percent. The risks are exacerbated when such sensitive information becomes publicly accessible on the internet, not just on the dark web, which requires special software to access. These exposures increase the likelihood of misuse and emphasize the necessity of protecting our digital identities.
The Threat of Identity Theft
The most pressing threat from compromised data is identity theft. Malicious actors can access email, bank, and credit card accounts to impersonate victims. This can involve resetting passwords and taking control of phone numbers to bypass text message confirmations. Furthermore, armed with personal details, thieves might take out loans or credit cards in your name, a common and damaging form of identity theft. The danger extends beyond online fraud; stolen information can lead to physical crimes, putting victims at severe risk. Thus, it is vital to take robust measures to protect against these escalating threats.
1. Use Multi-Factor Authentication Everywhere
Implementing multi-factor authentication (MFA) ubiquitously is paramount in reducing the likelihood of account breaches. Some sources suggest that accounts with MFA are 99.9 percent less likely to be compromised. By requiring additional verification steps, such as codes sent via text, email, or USB authenticator keys, MFA significantly enhances account protection and guards against compromised credentials.
2. Manage Password Risk
Ensure the security of your key online and financial accounts by using distinct, robust, and lengthy passwords. Strive for a minimum of 15 characters, incorporating a blend of uppercase and lowercase letters, numbers, and symbols. Utilize password managers to safely store and handle these intricate passwords, as they can also generate strong passwords for you. Furthermore, consider creating a separate "junk" email for non-essential sign-ups, enhancing security and reducing the potential fallout from data breaches on your primary accounts.
3. Use Protection Across Your Devices
Utilize trusted antivirus (AV) software on both desktop and mobile devices. Many people overlook the importance of AV on their phones, yet these devices often store credit card information and provide access to key accounts. Comprehensive AV protection across all devices is crucial for safeguarding sensitive data.
4. Secure Your Surfing
Be mindful of the information you share online and with whom. Use incognito mode when possible, and provide false information where appropriate. A secondary email address, along with an alternate name, date of birth, and security question answers, can further protect your primary accounts. Additionally, when using public Wi-Fi or even at home, a virtual private network (VPN) can mask your location and encrypt data shared on the local network.
5. Regularly Monitor
Continually monitor your online accounts and finances for suspicious activity. Identity Theft Protection services can help keep your data secure by scanning databases for any instances of your email address being linked to data breaches and alerting you to potential security risks. These services provide an efficient way to stay informed about the status of your personal information.
6. Stay Vigilant
Remain alert to phishing and social engineering schemes, including deceptive emails or calls. Verify suspicious communications by contacting the company or organization directly through their official website, avoiding links or contact information provided in unsolicited messages. Reflect on whether you initiated the contact or if someone reached out to you, and proceed with caution if it’s the latter. Despite best efforts, scams can still occur. Promptly reacting to data breaches can prevent further damage and monetary loss. Identifying and addressing online weak spots, such as predictable passwords or a lack of MFA, is essential for robust identity protection.
Adopting a careful and thorough strategy for safeguarding your identity ensures that even if your information is breached, you have preemptive steps implemented to shield your confidential data. These actions help defend your online presence against cyber hazards, offering reassurance in an ever-more connected world.
![Latanskiy Nick Latanskiy Nick]() Latanskiy Nick
2024-05-27
Latanskiy Nick
2024-05-27
-
![Roblox: Active Peroxide Codes Roblox: Active Peroxide Codes]() Tips & Guides
Roblox: Active Peroxide Codes
Roblox games like Peroxide occasionally release active codes that give you free rewards, but they can be hard to use without the right context. Inspired by the iconic Bleach series, Peroxide gives you in-game resources through codes provided by the developers. With enough materials, you can buy important items that may help you overcome various struggles throughout your sword-swinging adventure.
Similar to Anime Showdown codes for Roblox, you have to redeem codes before they expire in the future. The timing of when a code expires depends on the developers of Peroxide, but usually, a code only lasts for a few weeks or a month at most. The faster you activate a code phrase, the faster you can claim its free rewards without having to worry about saving it for later.
If you want to know whether certain codes are active or expired, check out the official Discord for Peroxide. This server will also help you see when the developers release new codes you can activate.
How To Use Peroxide Codes In Roblox
Follow Instructions From The Settings
After you start your journey in Peroxide, you can use codes by completing the tutorial and accessing the Settings icon in the top left corner of your screen. Finishing the introduction of the game allows you to start adjusting Settings, where codes can also be activated. Go to the "Settings" tab of Peroxide, where you can see a large blank space with the words "Code Here" that you can click on to get started.
Enter a code phrase into the blank space's text box, but make sure the code still works and doesn't have any grammatical errors. Even one number or letter out of place will be enough to prevent the code from working, causing you to lose out on many rewards. Always make sure to double-check how you've inputted codes before trying to activate them, as many phrases can only be used once by one player.
In a sharp similarity to other Bleach-inspired games like Soul Wars in Roblox, the codes you redeem offer a type of currency called Product Essence in Peroxide. This resource can be collected and taken to the character Kisuke and spent on rerolls for every path available in the game. You can find this NPC in The City, an area you may be familiar with after playing through the tutorial.
Product Essence can also be spent on cosmetic items for your character, giving you new ways to adjust your look as you play. Other items, slots, and accessories are also tied to Product Essence, reflecting how the material is at the core of Peroxide's gameplay. Those looking to explore everything this game has to offer will want to farm as much Essence as they can through codes right as the tutorial finishes.
Every Currently Active Peroxide Code
Share Rewards Across All Saved Slots
Every save slot you have will share Product Essence in one large pool, which prevents you from having to grind on multiple slots for more currency. However, keep in mind that this single collection of Essence can be spent quickly as a result, so you need to plan carefully for what you buy. Once again, codes can only be redeemed once per account, limiting the total Essence you can get at a time before new phrases drop.
Multiple accounts can be made to use a Peroxide active code more than once, but the Product Essence you receive can only be used on the account that redeemed the resources.
As you can see in the above video by YouTube creator Corgi, the message "Already Used Code" will pop up in Peroxide if you have already used a phrase on your account. Even with earned Robux in Roblox, you will be unable to get more of this currency for free until more codes are active. For now, the codes available in the game are:
Active Code
Rewards
SkibiShutdown
30 Product Essence
GokuDayCodeSuper2
15 Product Essence
310KLikesHappyWeekend
25 Product Essence
230MVisitsCodeCritters
25 Product Essence
sorry4thebugs
25 Product Essence
220MVisitsArrancarTerrorism
30 Product Essence
AlvinAndTheChipmunks
30 Product Essence
FusionHoldingUsHostageUpdateIsComing
25 Product Essence
EclipseDontBurnUrEyes
15 Product Essence
330kLikesSorryLate
35 Product Essence
20BILLIONTIRLLCOINDDOIFDSUPERNOTSCAMCODE
Random Amount of Product Essence
TwoTrillionAprilPECode
2 Trillion Product Essence
ShutdownToFixNPCsAgain
25 Product Essence
210MVisitsAwesome
30 Product Essence
PeroxideAnniPE
50 Product Essence
UnluckyBruhxide
50 Product Essence
290kLikesLOOLOLOL
30 Product Essence
200MVisitsAwesome
25 Product Essence
ValentinesDayButNoValentines
45 Product Essence
FusionStopGamblingWorkOnTheGame
25 Product Essence
FusionForgotHowToShutdown
Random amount of Product Essence
190mVisitsThanks
30 Product Essence
ThanksForPingingAhmed
25 Product Essence
280kLikesThankYouForYourSupport
25 Product Essence
180mVistsTrollDelay
20 Product Essence
CodeCrittersVsBugFixers
20 Product Essence
CodeCrittersVsBugFixersPart2
15 Product Essence
StopListeningToTrialMods
25 Product Essence
HappyNewYearJoMamaJoeBiden12121
20 Product Essence
Chungsmas
30 Product Essence
170mVisitsGuys
15 Product Essence
270kLikesOhHowJolly
15 Product Essence
FBBossIncident
15 Product Essence
FBUpdate
15 Product Essence, 1 Slot
How To Check If Codes Have Expired
Look At Multiple Sources
Although simply entering a code and its failure to work could tell you whether it has expired or not, there are some situations where a code not working suddenly activates. To avoid confusion, the best way to see if a code has expired is to check how long it has been operating or see what dates other players report using it. Oftentimes, some codes that others claim to work have long since expired following the phrase's release.
Unfortunately, the developers of Peroxide have not updated many of the codes on their social sites with expiration dates. Unlike many of the most popular Roblox games on the platform right now, it can be hard to tell which codes are working at any moment. Even from the list provided above, there may be some phrases that have expired in the months following this time of writing.
You can always message other players to make sure a certain code does or does not work, but you should always try inputting a phrase multiple times when you get stuck. After a few attempts, accept that one code may be lost and move on to the next one. Figuring out how to use codes for Peroxide in Roblox may cause some struggles here and there if you don't follow the right steps as you go.
Tips & Guides
Roblox: Active Peroxide Codes
Roblox games like Peroxide occasionally release active codes that give you free rewards, but they can be hard to use without the right context. Inspired by the iconic Bleach series, Peroxide gives you in-game resources through codes provided by the developers. With enough materials, you can buy important items that may help you overcome various struggles throughout your sword-swinging adventure.
Similar to Anime Showdown codes for Roblox, you have to redeem codes before they expire in the future. The timing of when a code expires depends on the developers of Peroxide, but usually, a code only lasts for a few weeks or a month at most. The faster you activate a code phrase, the faster you can claim its free rewards without having to worry about saving it for later.
If you want to know whether certain codes are active or expired, check out the official Discord for Peroxide. This server will also help you see when the developers release new codes you can activate.
How To Use Peroxide Codes In Roblox
Follow Instructions From The Settings
After you start your journey in Peroxide, you can use codes by completing the tutorial and accessing the Settings icon in the top left corner of your screen. Finishing the introduction of the game allows you to start adjusting Settings, where codes can also be activated. Go to the "Settings" tab of Peroxide, where you can see a large blank space with the words "Code Here" that you can click on to get started.
Enter a code phrase into the blank space's text box, but make sure the code still works and doesn't have any grammatical errors. Even one number or letter out of place will be enough to prevent the code from working, causing you to lose out on many rewards. Always make sure to double-check how you've inputted codes before trying to activate them, as many phrases can only be used once by one player.
In a sharp similarity to other Bleach-inspired games like Soul Wars in Roblox, the codes you redeem offer a type of currency called Product Essence in Peroxide. This resource can be collected and taken to the character Kisuke and spent on rerolls for every path available in the game. You can find this NPC in The City, an area you may be familiar with after playing through the tutorial.
Product Essence can also be spent on cosmetic items for your character, giving you new ways to adjust your look as you play. Other items, slots, and accessories are also tied to Product Essence, reflecting how the material is at the core of Peroxide's gameplay. Those looking to explore everything this game has to offer will want to farm as much Essence as they can through codes right as the tutorial finishes.
Every Currently Active Peroxide Code
Share Rewards Across All Saved Slots
Every save slot you have will share Product Essence in one large pool, which prevents you from having to grind on multiple slots for more currency. However, keep in mind that this single collection of Essence can be spent quickly as a result, so you need to plan carefully for what you buy. Once again, codes can only be redeemed once per account, limiting the total Essence you can get at a time before new phrases drop.
Multiple accounts can be made to use a Peroxide active code more than once, but the Product Essence you receive can only be used on the account that redeemed the resources.
As you can see in the above video by YouTube creator Corgi, the message "Already Used Code" will pop up in Peroxide if you have already used a phrase on your account. Even with earned Robux in Roblox, you will be unable to get more of this currency for free until more codes are active. For now, the codes available in the game are:
Active Code
Rewards
SkibiShutdown
30 Product Essence
GokuDayCodeSuper2
15 Product Essence
310KLikesHappyWeekend
25 Product Essence
230MVisitsCodeCritters
25 Product Essence
sorry4thebugs
25 Product Essence
220MVisitsArrancarTerrorism
30 Product Essence
AlvinAndTheChipmunks
30 Product Essence
FusionHoldingUsHostageUpdateIsComing
25 Product Essence
EclipseDontBurnUrEyes
15 Product Essence
330kLikesSorryLate
35 Product Essence
20BILLIONTIRLLCOINDDOIFDSUPERNOTSCAMCODE
Random Amount of Product Essence
TwoTrillionAprilPECode
2 Trillion Product Essence
ShutdownToFixNPCsAgain
25 Product Essence
210MVisitsAwesome
30 Product Essence
PeroxideAnniPE
50 Product Essence
UnluckyBruhxide
50 Product Essence
290kLikesLOOLOLOL
30 Product Essence
200MVisitsAwesome
25 Product Essence
ValentinesDayButNoValentines
45 Product Essence
FusionStopGamblingWorkOnTheGame
25 Product Essence
FusionForgotHowToShutdown
Random amount of Product Essence
190mVisitsThanks
30 Product Essence
ThanksForPingingAhmed
25 Product Essence
280kLikesThankYouForYourSupport
25 Product Essence
180mVistsTrollDelay
20 Product Essence
CodeCrittersVsBugFixers
20 Product Essence
CodeCrittersVsBugFixersPart2
15 Product Essence
StopListeningToTrialMods
25 Product Essence
HappyNewYearJoMamaJoeBiden12121
20 Product Essence
Chungsmas
30 Product Essence
170mVisitsGuys
15 Product Essence
270kLikesOhHowJolly
15 Product Essence
FBBossIncident
15 Product Essence
FBUpdate
15 Product Essence, 1 Slot
How To Check If Codes Have Expired
Look At Multiple Sources
Although simply entering a code and its failure to work could tell you whether it has expired or not, there are some situations where a code not working suddenly activates. To avoid confusion, the best way to see if a code has expired is to check how long it has been operating or see what dates other players report using it. Oftentimes, some codes that others claim to work have long since expired following the phrase's release.
Unfortunately, the developers of Peroxide have not updated many of the codes on their social sites with expiration dates. Unlike many of the most popular Roblox games on the platform right now, it can be hard to tell which codes are working at any moment. Even from the list provided above, there may be some phrases that have expired in the months following this time of writing.
You can always message other players to make sure a certain code does or does not work, but you should always try inputting a phrase multiple times when you get stuck. After a few attempts, accept that one code may be lost and move on to the next one. Figuring out how to use codes for Peroxide in Roblox may cause some struggles here and there if you don't follow the right steps as you go.
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-05-24
Ethan Blackstone
2024-05-24

![CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025 CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025]() News
CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025
In 2021, Radical Fish Games initially introduced a new action RPG titled Project Terra. Now, they have officially named it Alabaster Dawn and announced that it will be available in Steam Early Access in late 2025.
The narrative centers around Juno, referred to as the “Outcast Chosen.” She awakens to find herself in a devastated world and embarks on a quest to revive humanity while confronting the enigmatic Nyx, who seems to be linked to the calamity that has befallen civilization. Fans of CrossCode will recognize familiar elements in the combat mechanics, world layout, and platforming aspects. The traditional four elemental forces return, but players now have access to eight distinct weapons.
Each of the four elements corresponds to two different weapons, allowing for a flexible combat experience. Additionally, the game will feature Combat Arts, which offers a range of techniques to use in battles, along with brand-new Divine Arts. Participants will be able to explore the expansive terrain, collect an assortment of precious Stones, obtain resources for upgrades, and discover culinary formulas that enable them to create dishes providing short-term advantages.
While Alabaster Dawn does not have a specific release date set yet, it has been confirmed for future availability on consoles and PC, creating excitement within the gaming community.
News
CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025
In 2021, Radical Fish Games initially introduced a new action RPG titled Project Terra. Now, they have officially named it Alabaster Dawn and announced that it will be available in Steam Early Access in late 2025.
The narrative centers around Juno, referred to as the “Outcast Chosen.” She awakens to find herself in a devastated world and embarks on a quest to revive humanity while confronting the enigmatic Nyx, who seems to be linked to the calamity that has befallen civilization. Fans of CrossCode will recognize familiar elements in the combat mechanics, world layout, and platforming aspects. The traditional four elemental forces return, but players now have access to eight distinct weapons.
Each of the four elements corresponds to two different weapons, allowing for a flexible combat experience. Additionally, the game will feature Combat Arts, which offers a range of techniques to use in battles, along with brand-new Divine Arts. Participants will be able to explore the expansive terrain, collect an assortment of precious Stones, obtain resources for upgrades, and discover culinary formulas that enable them to create dishes providing short-term advantages.
While Alabaster Dawn does not have a specific release date set yet, it has been confirmed for future availability on consoles and PC, creating excitement within the gaming community.
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-08-12
Ethan Blackstone
2024-08-12
![The Last of Us Part II: In-Depth Character Analysis and Storyline Exploration The Last of Us Part II: In-Depth Character Analysis and Storyline Exploration]() Editor’s Choice
The Last of Us Part II: In-Depth Character Analysis and Storyline Exploration
The Last of Us Part II is an action-adventure video game that has gained significant popularity since its inception. Developed with immense creative prowess by Naughty Dog and published by the renowned Sony Interactive Entertainment, this video game has managed to carve a niche for itself in the competitive world of gaming. The distinct element that elevates this game's renown is its remarkable gameplay that enthralls both veteran game enthusiasts and fledgling players in equal measure.
The gaming encounter takes place in a world devastated by a catastrophic event, creating an enthralling canvas for the gameplay. However, it's not just the high-octane action sequences that make this game stand out. The heart of The Last of Us Part II lies in its deep storytelling, which proves to be just as, if not more, gripping as its action.
The depth of the characters in this game is truly commendable. The creators focused on building characters that are both relatable and complex, thereby ensuring the gamers' emotional investment in the plot. Alongside the main characters, the minor characters have also been carefully crafted, resulting in a realistic and immersive gaming experience.
Another important aspect that elevates The Last of Us Part II to a new level is its intricately woven plot. The complexity and layers of the story intrigue gamers, prompting them to delve deeper into the game's universe. It is this combination of deep characters and a well-crafted plot that provides the game its unique brand of strength and appeal.
In this article, we aim to delve further into the game's universe. We will be exploring the game's main characters, their development throughout the story, and the nuanced storyline that keeps the players hooked. By understanding these aspects in more depth, we can appreciate the ingenuity and hard work behind this successful game.
Main Characters and Character Development
The Last of Us Part II centers its narrative largely around two characters, Ellie and Abby. These individuals aren't mere characters in the gaming world, but rather, they are the backbone of this sequel, playing integral roles in driving the game's complex storyline. Their well-crafted persona and emotional depth bring a level of realness to the game that is rare to find, offering players the opportunity to delve deeper into their motives, thoughts, and actions.
Breaking away from the traditional approach of its predecessor, The Last of Us Part II takes a bold step in storytelling by providing a dual perspective in its narrative. This unique spin allows the players to experience the story from both Ellie's and Abby's points of view, lending much-needed depth to the storyline. It also highlights the subjectivity of human perception and experience as the same event unfolds differently in each character's gameplay, hence leaving the players with a broader outlook and understanding of the story.
The characters, Ellie and Abby, undergo elaborate character arcs throughout the game. They evolve tremendously; their growth is evident in their changing ideologies, decisions, and varying responses to the challenges they confront. By focusing on their character development, the game manages to convey the profound impacts of their life experiences and challenges faced in the post-apocalyptic world on their personalities.
Lastly, the game navigates through the complexities of Ellie and Abby's actions and emotions. It unearths the reasons behind their decisions, their conflicting emotions, and their struggle with their past and present. This exploration of complexity drives home the point that the characters aren't merely heroes or villains but complex individuals caught in a world where survival takes precedence over everything else.
Ellie: The Haunted Protagonist
Ellie, a nineteen-year-old survivor, sets out on a journey of retribution when a tragedy befalls her peaceful life in the post-apocalyptic world. Her character undergoes layers of transformation, moving from a carefree teenager to a revenge-driven individual. Her decisions, guided by pain and rage, paint a heart-wrenching picture of human vulnerability and resilience.
Abby: The Conflicted Antagonist
Abby's character challenges conventional villain templates. She evolves from a character initially perceived as ruthless to revealing her humane side shadowed by her past. Abby's quest for redemption, contrasted with her violent actions, incites conflicting emotions among players, thus enriching the narrative.
Secondary Characters: Their Impact and Role
Several secondary characters play crucial roles across the game, aiding and influencing the main characters' journey in profound ways. Key characters include Joel, Dina, and Isaac.
Joel: The Lingering Spirit
While the game starts with Joel's brutal end, his influence persists throughout the narrative. His actions in the prequel lay the groundwork for the events in The Last of Us Part II, leaving Ellie and Abby to suffer the repercussions of his choices.
Dina: Ellie's Anchor
Dina, a key ally and love interest of Ellie, provides solace and helps Ellie retain her humanity. Her character demonstrates the power of love and friendship in extreme circumstances and the consequences of their loss.
Isaac: The Cold Strategist
Isaac, the strategic leader of the Washington Liberation Front, plays an essential role in the war between factions. He illustrates the dehumanizing effects of long-term conflict and the cost of dogmatism.
Plot Analysis: The Multifaceted Storyline
The Last of Us Part II weaves an intricate tale revolving around both its hero and villain, probing profound undertones of existence, vengeance, affection, and atonement.
Survival and Revenge
The gaming narrative portrays the brutal truths of a world that has undergone an apocalypse, wherein the battle for survival is an unending challenge. Revenge emerges as a driving force, coloring the decisions and actions of the main characters while underlining the damaging effects of this dangerous pursuit.
Love and Redemption
Balancing the bleak aspects of the storyline are themes of love and redemption. These themes explore how love can act as a stabilizing influence and how redemption might be possible even in the most despairing circumstances. They add emotional depth and intricacy to the narrative.
Controversial Storytelling and Player Interpretations
The Last of Us Part II has incited polarizing reactions among players due to its unconventional storytelling and character development. Contemporary thematic exploration and unexpected character arcs have led to various interpretations and theories among the fanbase.
Conclusion: Assessing the Narrative Impact
The Last of Us Part II offers a highly immersive experience through compelling characters and a thought-provoking storyline. Its characters challenge traditional boundaries, growing and evolving through personal losses and wins. The multifaceted narrative blends elements of survival, revenge, love, and redemption, invoking strong emotions and prompting players to delve deeper. Despite its polarizing reception, the game ultimately solidifies its standing as a profound exploration of human nature in extreme circumstances.
Editor’s Choice
The Last of Us Part II: In-Depth Character Analysis and Storyline Exploration
The Last of Us Part II is an action-adventure video game that has gained significant popularity since its inception. Developed with immense creative prowess by Naughty Dog and published by the renowned Sony Interactive Entertainment, this video game has managed to carve a niche for itself in the competitive world of gaming. The distinct element that elevates this game's renown is its remarkable gameplay that enthralls both veteran game enthusiasts and fledgling players in equal measure.
The gaming encounter takes place in a world devastated by a catastrophic event, creating an enthralling canvas for the gameplay. However, it's not just the high-octane action sequences that make this game stand out. The heart of The Last of Us Part II lies in its deep storytelling, which proves to be just as, if not more, gripping as its action.
The depth of the characters in this game is truly commendable. The creators focused on building characters that are both relatable and complex, thereby ensuring the gamers' emotional investment in the plot. Alongside the main characters, the minor characters have also been carefully crafted, resulting in a realistic and immersive gaming experience.
Another important aspect that elevates The Last of Us Part II to a new level is its intricately woven plot. The complexity and layers of the story intrigue gamers, prompting them to delve deeper into the game's universe. It is this combination of deep characters and a well-crafted plot that provides the game its unique brand of strength and appeal.
In this article, we aim to delve further into the game's universe. We will be exploring the game's main characters, their development throughout the story, and the nuanced storyline that keeps the players hooked. By understanding these aspects in more depth, we can appreciate the ingenuity and hard work behind this successful game.
Main Characters and Character Development
The Last of Us Part II centers its narrative largely around two characters, Ellie and Abby. These individuals aren't mere characters in the gaming world, but rather, they are the backbone of this sequel, playing integral roles in driving the game's complex storyline. Their well-crafted persona and emotional depth bring a level of realness to the game that is rare to find, offering players the opportunity to delve deeper into their motives, thoughts, and actions.
Breaking away from the traditional approach of its predecessor, The Last of Us Part II takes a bold step in storytelling by providing a dual perspective in its narrative. This unique spin allows the players to experience the story from both Ellie's and Abby's points of view, lending much-needed depth to the storyline. It also highlights the subjectivity of human perception and experience as the same event unfolds differently in each character's gameplay, hence leaving the players with a broader outlook and understanding of the story.
The characters, Ellie and Abby, undergo elaborate character arcs throughout the game. They evolve tremendously; their growth is evident in their changing ideologies, decisions, and varying responses to the challenges they confront. By focusing on their character development, the game manages to convey the profound impacts of their life experiences and challenges faced in the post-apocalyptic world on their personalities.
Lastly, the game navigates through the complexities of Ellie and Abby's actions and emotions. It unearths the reasons behind their decisions, their conflicting emotions, and their struggle with their past and present. This exploration of complexity drives home the point that the characters aren't merely heroes or villains but complex individuals caught in a world where survival takes precedence over everything else.
Ellie: The Haunted Protagonist
Ellie, a nineteen-year-old survivor, sets out on a journey of retribution when a tragedy befalls her peaceful life in the post-apocalyptic world. Her character undergoes layers of transformation, moving from a carefree teenager to a revenge-driven individual. Her decisions, guided by pain and rage, paint a heart-wrenching picture of human vulnerability and resilience.
Abby: The Conflicted Antagonist
Abby's character challenges conventional villain templates. She evolves from a character initially perceived as ruthless to revealing her humane side shadowed by her past. Abby's quest for redemption, contrasted with her violent actions, incites conflicting emotions among players, thus enriching the narrative.
Secondary Characters: Their Impact and Role
Several secondary characters play crucial roles across the game, aiding and influencing the main characters' journey in profound ways. Key characters include Joel, Dina, and Isaac.
Joel: The Lingering Spirit
While the game starts with Joel's brutal end, his influence persists throughout the narrative. His actions in the prequel lay the groundwork for the events in The Last of Us Part II, leaving Ellie and Abby to suffer the repercussions of his choices.
Dina: Ellie's Anchor
Dina, a key ally and love interest of Ellie, provides solace and helps Ellie retain her humanity. Her character demonstrates the power of love and friendship in extreme circumstances and the consequences of their loss.
Isaac: The Cold Strategist
Isaac, the strategic leader of the Washington Liberation Front, plays an essential role in the war between factions. He illustrates the dehumanizing effects of long-term conflict and the cost of dogmatism.
Plot Analysis: The Multifaceted Storyline
The Last of Us Part II weaves an intricate tale revolving around both its hero and villain, probing profound undertones of existence, vengeance, affection, and atonement.
Survival and Revenge
The gaming narrative portrays the brutal truths of a world that has undergone an apocalypse, wherein the battle for survival is an unending challenge. Revenge emerges as a driving force, coloring the decisions and actions of the main characters while underlining the damaging effects of this dangerous pursuit.
Love and Redemption
Balancing the bleak aspects of the storyline are themes of love and redemption. These themes explore how love can act as a stabilizing influence and how redemption might be possible even in the most despairing circumstances. They add emotional depth and intricacy to the narrative.
Controversial Storytelling and Player Interpretations
The Last of Us Part II has incited polarizing reactions among players due to its unconventional storytelling and character development. Contemporary thematic exploration and unexpected character arcs have led to various interpretations and theories among the fanbase.
Conclusion: Assessing the Narrative Impact
The Last of Us Part II offers a highly immersive experience through compelling characters and a thought-provoking storyline. Its characters challenge traditional boundaries, growing and evolving through personal losses and wins. The multifaceted narrative blends elements of survival, revenge, love, and redemption, invoking strong emotions and prompting players to delve deeper. Despite its polarizing reception, the game ultimately solidifies its standing as a profound exploration of human nature in extreme circumstances.
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-08-11
Ethan Blackstone
2024-08-11
![Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO]() News
Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO
Despite its lackluster reception, Battlefield 2042 hasn't deterred EA from its commitment to the franchise. The company is channeling considerable resources into the next installment, with several of its studios collaborating on the project. Although specific details remain sparse, EA's CEO Andrew Wilson recently shared insights about what lies ahead for the Battlefield series.
During a quarterly earnings call, Wilson characterized the forthcoming game as one of EA’s most ambitious endeavors to date. He expressed confidence in the development team, stating that their goal is to create an immersive Battlefield experience that excites the player community. The enthusiasm around the project, according to Wilson, signals strong support for the team’s direction.
An array of studios is contributing to the Battlefield effort. Lead developer DICE is at the forefront, while Criterion Games is set to handle the single-player campaign after the dissolution of Ridgeline Games earlier this year. Additionally, the acclaimed Motive Studio is assembling a new team to support the game's development.
According to earlier reports, the upcoming Battlefield title is on track for release in October 2025. Meanwhile, Ripple Effect Studios is believed to be crafting a separate free-to-play battle royale experience within the franchise, further expanding its offerings.
News
Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO
Despite its lackluster reception, Battlefield 2042 hasn't deterred EA from its commitment to the franchise. The company is channeling considerable resources into the next installment, with several of its studios collaborating on the project. Although specific details remain sparse, EA's CEO Andrew Wilson recently shared insights about what lies ahead for the Battlefield series.
During a quarterly earnings call, Wilson characterized the forthcoming game as one of EA’s most ambitious endeavors to date. He expressed confidence in the development team, stating that their goal is to create an immersive Battlefield experience that excites the player community. The enthusiasm around the project, according to Wilson, signals strong support for the team’s direction.
An array of studios is contributing to the Battlefield effort. Lead developer DICE is at the forefront, while Criterion Games is set to handle the single-player campaign after the dissolution of Ridgeline Games earlier this year. Additionally, the acclaimed Motive Studio is assembling a new team to support the game's development.
According to earlier reports, the upcoming Battlefield title is on track for release in October 2025. Meanwhile, Ripple Effect Studios is believed to be crafting a separate free-to-play battle royale experience within the franchise, further expanding its offerings.
![Ava Reynolds Ava Reynolds]() Ava Reynolds
2024-08-07
Ava Reynolds
2024-08-07
![Fortnite: Building Techniques for Winning More Battles Fortnite: Building Techniques for Winning More Battles]() Tips & Guides
Fortnite: Building Techniques for Winning More Battles
Fortnite Battle Royale stands out from the crowd of online multiplayer games due to its distinctive building mechanics. This wildly popular game has captivated players worldwide, offering a unique blend of shooter and builder gameplay styles. Instead of simply relying on finding the perfect weapon to take out your opponents, Fortnite adds an extra layer of strategy by enabling players to construct various structures in the gaming landscape.
Building in Fortnite serves several tactical purposes: it can provide defenses to shield you from enemy attacks, form offensive platforms from which to stage your assaults, and aid in quick movements across the map. A simple wooden wall or towering fortress can mean the difference between victory and defeat. This game element goes far beyond mere survival; It takes on a crucial part in orchestrating your comprehensive combat tactics.
At first glance, the art of building in Fortnite might seem straightforward - you just need to select the right materials and start constructing, right? However, the intricacies lie in the execution. Effective building requires a keen sense of timing, a high degree of precision, and, most importantly, strategic thinking. The layout structure, the choice of materials, and even the decision of when and where to build - these are all factors that contribute to your overall gameplay.
By refining your building techniques, you can significantly improve your survival chances in the game. A player skilled in building can quickly create structures to outmaneuver opponents, gaining the upper hand in firefights and increasing their odds of emerging victorious. Mastering diverse building strategies allows you to adapt to any situation you encounter, turning potential threats into opportunities for victory.
In the proceeding paragraphs, we shall delve into six advanced building methods to improve your gameplay. By implementing these techniques, you can elevate your Fortnite skills to the next level, ensuring that you always have a few tricks up your sleeve for your next battle.
1. Quick Fort Building
The art of building in Fortnite commences with understanding the nuts and bolts of constructing a simple 1x1 fort. As a straightforward and basic building technique, quick fort building serves as your entry point into the realm of Fortnite construction strategies. Its objective is to provide players with a swift and easy solution to defend against enemy fire and gain an advantageous position in battle.
As the name suggests, the 1x1 fort is a compact structure, serving as a protective shell against enemy attacks. The beauty of this quick fort lies in its simplicity and efficiency. When you find yourself in the thick of battle with bullets flying around, this structure can provide you with the much-needed protection to shield yourself from direct hits.
The 1x1 fort is not just about defense; it provides an excellent vantage point to observe the battlefield and spot adversaries. From the safety of your fort, you can gather crucial information about the enemy's location and game plan. Your fort situates you higher than ground level, giving you an overview of the unfolding battle and the positions of your competitors.
Building a quick fort is a straightforward process but requires speed and precision. The first step is laying down four walls, forming a closed square around you. Then, inside this box, you need to add stairs. The stairs elevate you, enhancing your viewing range and offering a platform to return fire. To cap it off, do not forget to add a roof on top to secure yourself from attacks from above.
It is essential to practice this technique under low-pressure conditions. Doing so will allow you to enhance your building speed, reducing the time it takes to create a fort when you're in the heart of the battle. Your goal should be to construct the fort so swiftly that it becomes second nature. The quick fort, given its utility and ease of construction, can be your reliable ally in the unpredictable and volatile world of Fortnite.
2. Ramp Rush
Ramp rushing is an offensive building technique employed to close the gap between you and your enemy. It involves building ramp structures towards the enemy; the height advantage can help you gain better aim. However, it's crucial to reinforce your ramps with walls to prevent the enemy from shooting down your structure. Remember, building with wooden materials may be quicker but also less durable than stone or metal, so choose your materials wisely depending on the situation.
3. Double Ramping
Double ramping takes ramp rushing to the next level by adding an extra layer of protection. This implies building two ramps parallel to each other, reinforced by walls for better defense. This strategy allows you to gain both height and pressure on your opponents while minimizing your own risks. Double ramping can consume more materials compared to a single ramp rush, but the additional safety it provides is often worth the expenditure.
4. Waterfalling
Waterfalling is a crucial skill when you need to descend from great heights quickly and safely. This technique involves building ramps or floors beneath you as you fall, mitigating fall damage. Beginners may struggle with this technique as it requires precise timing and fast reactions. However, mastering waterfalling can be a literal lifesaver in many Fortnite engagements.
5. Pyramid and Cone Jumps
Pyramid or cone jumps provide a sneaky way of outsmarting and outrunning your opponents by confusing them with unexpected moves. A cone jump involves creating a pyramid structure over your ramp and then jumping on the pyramid, hence breaking the linear direction of your ramp rush. This tactic is extremely useful when you want to shift direction quickly without sacrificing safety or height advantage.
6. High Ground Retake
High Ground Retake is the art of stealing the high-ground advantage from your opponent through strategic building. This technique involves several steps, including building ramps above you, boxing yourself in, and constructing a staircase to ascend further. This technique may seem complex at first, but mastering it can provide a significant advantage, especially in late-game build fights.
Conclusion
Advanced building techniques in Fortnite Battle Royale are game-changing skills that separate average players from pros. Implementing these methods into your gaming strategy can elevate your attack and defense skills. This will always keep you one pace ahead of your competitors. Bear in mind that to excel as a professional architect in Fortnite, continuous practice, endurance, and tactical cognition are essential. Enjoy assembling and conquering!
Tips & Guides
Fortnite: Building Techniques for Winning More Battles
Fortnite Battle Royale stands out from the crowd of online multiplayer games due to its distinctive building mechanics. This wildly popular game has captivated players worldwide, offering a unique blend of shooter and builder gameplay styles. Instead of simply relying on finding the perfect weapon to take out your opponents, Fortnite adds an extra layer of strategy by enabling players to construct various structures in the gaming landscape.
Building in Fortnite serves several tactical purposes: it can provide defenses to shield you from enemy attacks, form offensive platforms from which to stage your assaults, and aid in quick movements across the map. A simple wooden wall or towering fortress can mean the difference between victory and defeat. This game element goes far beyond mere survival; It takes on a crucial part in orchestrating your comprehensive combat tactics.
At first glance, the art of building in Fortnite might seem straightforward - you just need to select the right materials and start constructing, right? However, the intricacies lie in the execution. Effective building requires a keen sense of timing, a high degree of precision, and, most importantly, strategic thinking. The layout structure, the choice of materials, and even the decision of when and where to build - these are all factors that contribute to your overall gameplay.
By refining your building techniques, you can significantly improve your survival chances in the game. A player skilled in building can quickly create structures to outmaneuver opponents, gaining the upper hand in firefights and increasing their odds of emerging victorious. Mastering diverse building strategies allows you to adapt to any situation you encounter, turning potential threats into opportunities for victory.
In the proceeding paragraphs, we shall delve into six advanced building methods to improve your gameplay. By implementing these techniques, you can elevate your Fortnite skills to the next level, ensuring that you always have a few tricks up your sleeve for your next battle.
1. Quick Fort Building
The art of building in Fortnite commences with understanding the nuts and bolts of constructing a simple 1x1 fort. As a straightforward and basic building technique, quick fort building serves as your entry point into the realm of Fortnite construction strategies. Its objective is to provide players with a swift and easy solution to defend against enemy fire and gain an advantageous position in battle.
As the name suggests, the 1x1 fort is a compact structure, serving as a protective shell against enemy attacks. The beauty of this quick fort lies in its simplicity and efficiency. When you find yourself in the thick of battle with bullets flying around, this structure can provide you with the much-needed protection to shield yourself from direct hits.
The 1x1 fort is not just about defense; it provides an excellent vantage point to observe the battlefield and spot adversaries. From the safety of your fort, you can gather crucial information about the enemy's location and game plan. Your fort situates you higher than ground level, giving you an overview of the unfolding battle and the positions of your competitors.
Building a quick fort is a straightforward process but requires speed and precision. The first step is laying down four walls, forming a closed square around you. Then, inside this box, you need to add stairs. The stairs elevate you, enhancing your viewing range and offering a platform to return fire. To cap it off, do not forget to add a roof on top to secure yourself from attacks from above.
It is essential to practice this technique under low-pressure conditions. Doing so will allow you to enhance your building speed, reducing the time it takes to create a fort when you're in the heart of the battle. Your goal should be to construct the fort so swiftly that it becomes second nature. The quick fort, given its utility and ease of construction, can be your reliable ally in the unpredictable and volatile world of Fortnite.
2. Ramp Rush
Ramp rushing is an offensive building technique employed to close the gap between you and your enemy. It involves building ramp structures towards the enemy; the height advantage can help you gain better aim. However, it's crucial to reinforce your ramps with walls to prevent the enemy from shooting down your structure. Remember, building with wooden materials may be quicker but also less durable than stone or metal, so choose your materials wisely depending on the situation.
3. Double Ramping
Double ramping takes ramp rushing to the next level by adding an extra layer of protection. This implies building two ramps parallel to each other, reinforced by walls for better defense. This strategy allows you to gain both height and pressure on your opponents while minimizing your own risks. Double ramping can consume more materials compared to a single ramp rush, but the additional safety it provides is often worth the expenditure.
4. Waterfalling
Waterfalling is a crucial skill when you need to descend from great heights quickly and safely. This technique involves building ramps or floors beneath you as you fall, mitigating fall damage. Beginners may struggle with this technique as it requires precise timing and fast reactions. However, mastering waterfalling can be a literal lifesaver in many Fortnite engagements.
5. Pyramid and Cone Jumps
Pyramid or cone jumps provide a sneaky way of outsmarting and outrunning your opponents by confusing them with unexpected moves. A cone jump involves creating a pyramid structure over your ramp and then jumping on the pyramid, hence breaking the linear direction of your ramp rush. This tactic is extremely useful when you want to shift direction quickly without sacrificing safety or height advantage.
6. High Ground Retake
High Ground Retake is the art of stealing the high-ground advantage from your opponent through strategic building. This technique involves several steps, including building ramps above you, boxing yourself in, and constructing a staircase to ascend further. This technique may seem complex at first, but mastering it can provide a significant advantage, especially in late-game build fights.
Conclusion
Advanced building techniques in Fortnite Battle Royale are game-changing skills that separate average players from pros. Implementing these methods into your gaming strategy can elevate your attack and defense skills. This will always keep you one pace ahead of your competitors. Bear in mind that to excel as a professional architect in Fortnite, continuous practice, endurance, and tactical cognition are essential. Enjoy assembling and conquering!
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-08-06
Ethan Blackstone
2024-08-06
![Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges” Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges”]() News
Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges”
Marvel Rivals is shaping up to be an exciting entry into the hero shooter genre, thanks in part to its well-established branding and the unique capabilities it brings to the table. The game boasts an impressive lineup of playable characters, each equipped with diverse moves and skills. However, this variety has presented some hurdles for the development team at NetEase Games.
In a recent discussion with GamingBolt, the developers revealed that balancing the experience while ensuring every character feels distinct has been a significant challenge—especially concerning melee-heavy heroes like Thor, Spider-Man, and the Incredible Hulk. If not properly handled, the dynamic of close-quarters combat could lead to chaotic gameplay that might detract from the enjoyment.
The developers articulated their struggle, emphasizing that crafting a diverse set of melee combatants was a top priority. They noted that mishandling these characters could result in battles lacking substance, ultimately compromising the gaming experience.
Yet, the unique abilities of the Marvel roster also presented exciting opportunities for the developers. They explained how the Hulk's impressive leaping ability was designed to impact aerial foes, adding an interesting layer to his play style. Venom's symbiotic traits were expanded to allow for mid-range attacks, while Spider-Man’s agility enables fluid transitions between melee and ranged encounters.
By focusing on each hero's strengths, the team aims to create a captivating gameplay experience that highlights each character’s unique mechanics.
Marvel Rivals is currently under development for PS5, Xbox Series X/S, and PC, with no confirmed release date available at this time.
News
Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges”
Marvel Rivals is shaping up to be an exciting entry into the hero shooter genre, thanks in part to its well-established branding and the unique capabilities it brings to the table. The game boasts an impressive lineup of playable characters, each equipped with diverse moves and skills. However, this variety has presented some hurdles for the development team at NetEase Games.
In a recent discussion with GamingBolt, the developers revealed that balancing the experience while ensuring every character feels distinct has been a significant challenge—especially concerning melee-heavy heroes like Thor, Spider-Man, and the Incredible Hulk. If not properly handled, the dynamic of close-quarters combat could lead to chaotic gameplay that might detract from the enjoyment.
The developers articulated their struggle, emphasizing that crafting a diverse set of melee combatants was a top priority. They noted that mishandling these characters could result in battles lacking substance, ultimately compromising the gaming experience.
Yet, the unique abilities of the Marvel roster also presented exciting opportunities for the developers. They explained how the Hulk's impressive leaping ability was designed to impact aerial foes, adding an interesting layer to his play style. Venom's symbiotic traits were expanded to allow for mid-range attacks, while Spider-Man’s agility enables fluid transitions between melee and ranged encounters.
By focusing on each hero's strengths, the team aims to create a captivating gameplay experience that highlights each character’s unique mechanics.
Marvel Rivals is currently under development for PS5, Xbox Series X/S, and PC, with no confirmed release date available at this time.
![Latanskiy Nick Latanskiy Nick]() Latanskiy Nick
2024-08-05
Latanskiy Nick
2024-08-05
![Character Guide: Exploring the Champions of League of Legends Character Guide: Exploring the Champions of League of Legends]() Tips & Guides
Character Guide: Exploring the Champions of League of Legends
The world of gaming is brimming with numerous enthralling experiences, but few can hold a candle to the captivating scenarios laid out in the landscape of League of Legends (LoL). Its widespread acceptance among gaming enthusiasts worldwide and the electrifying gameplay that keeps players on the edge of their seats are largely attributed to its diverse lineup of champions.
From their distinctive abilities to their individual strategic significance, each champion in LoL adds a new dimension to the gameplay. They each possess unique abilities that can be wielded in the game, laying the foundation for an endlessly versatile variety of dynamics in each battle. With each of them fulfilling unique roles that they're tailored for, champions bring specific tactics and strategies to the table, making the gameplay ever-engrossing.
As you get accustomed to the thrilling realm of LoL, an in-depth knowledge of the champions becomes indispensable. This comprehensive guide is designed to provide you with a deeper understanding of the champions, shedding light on their unique abilities, roles, and tactical uses. Furthermore, we'll delve into the various categories champions fall into and the strategic value each holds in the game.
But awareness cannot replace skill. The actual challenge lies in mastering these champions. Every champion requires a different approach and strategy, and understanding alone won't quite cut it. So, we intend to provide tips on mastering them as well, ensuring you can take full advantage of the potential each champion holds.
Understanding the Unique Abilities of Champions
In the exhilarating world of League of Legends, each champion brings a unique personality to the battlefield. And the key factor defining this personality is the distinct set of abilities that each champion possesses. It's these special abilities that carve out the champion's playstyle, laying the groundwork for their approach and tactics when venturing into the battlefield.
The abilities of champions demonstrate a diverse range, each serving different purposes in the match. They are typically categorized as 'Passive,' 'Q,' 'W,' 'E,' and 'Ultimate.' Understanding these categories is critical to comprehending a champion's capabilities and knowing how to strategize effectively during the game.
The 'Passive' ability is a champion's fundamental attribute, which is inherently enabled during the game. It does not require any command to activate and remains operational, emphasizing the inherent nature or the core strength of the champion throughout.
The 'Q,' 'W,' and 'E' signify the basic abilities that every champion possesses. These abilities play a significant role during the fiercely fought battles. Choose the right moments to deploy and upgrade these abilities, for they hold the potential to shift the balance of the game. The upgrade of these abilities happens during the course of the match, progressively increasing the champion's power and tactics.
Above all, we have the 'Ultimate' ability - the ace up the champion's sleeve. This ability is the champion's strongest asset and, thus, is available only after reaching a particular level. Unleashing the Ultimate ability can turn the tide of the match, making it a valuable weapon to wield at the right moment.
Roles of Champions in Gameplay
While each champion in League of Legends brings unique abilities to the table, they are also defined by the roles they play within the gaming environment. These roles, distinguished by a versatile range of objectives and skills, are crucial to understanding and utilizing the champions to their fullest potential. The primary roles we encounter within the game are 'Attack Damage Carry (ADC),' 'Support,' 'Mid,' 'Top,' and 'Jungle.'
The ADC, or 'Attack Damage Carry,' embodies a powerful figure in the gaming field. Often paired with the Support, their task is to deal notable damage, especially as the game reaches its later stages. Their power grows gradually through the game, and they are the cornerstone of the team's offensive strategies when they reach their peak power level at the end of the game.
The 'Support' champions, as the name aptly suggests, are the team's backbone. Their primary objective is to assist the team in a multitude of ways, but often, their prime responsibility lies in safeguarding the ADC. They contain and mitigate threats to the ADC, enabling them to wreak havoc upon opposing teams unhindered.
'Mid' champions take charge of the mid-lane, a position characterized by independent gameplay. They typically involve champions capable of handling themselves solo, holding the lane steady. The mid-champions can often shift the dynamics of the game through their individual performance in the mid-lane.
'Top' champions, akin to the stalwart defenders in a team, operate largely in isolation from the team. The characteristic feature of their gameplay is their gritty resilience and the ability to soak up damage. Their hardiness allows them to withstand substantial onslaughts, making them formidable opponents in their own right.
Last but hardly least, 'Jungle' champions, much like wildcards in a set, operate without being tied down to a particular lane. They wander the areas between lanes, aptly known as the "jungle," rendering assistance where needed. Their role is fluid and often involves counteracting enemy strategies, providing Support, and seizing opportunities across the game map.
Classification of Champions
Further, champions are classified based on their specific strengths and playing style. The classifications are 'Tank,' 'Mage,' 'Fighter,' 'Assassin,' 'Marksman,' and 'Support.' Tank champions have high durability and crowd control abilities, mages are magic damage dealers, and fighters are versatile champions who can both deal and take damage. Assassins specialize in damaging specific targets, marksman champions deal consistent damage from a range, and support champions have abilities to protect and enhance their team.
Getting to Grips with Strategizing
Understanding the facets of champions is not enough; knowing how to use them strategically is key to mastering League of Legends. Each champion is unique, and mastering them requires understanding their strengths and weaknesses. Players have to customize their gameplay according to the champion they use and adapt to their chosen champion's abilities. A strategic approach to each champion's abilities will significantly enhance your game.
Tips to Master Champions
Mastering a champion requires understanding their abilities and also their roles in the game. Start with understanding the champion's abilities and how you can use them during gameplay. Use tutorials and guides to understand how to play the champion efficiently. Practice using the abilities of the champion in various situations during the game. Try to learn one champion at a time and understand all loopholes and gameplay strategies with that champion before moving to the next.
Final Words
League of Legends champions, with their diverse abilities and roles, add significant strategic depth to the gameplay. Regardless if you are an experienced gamer wanting to boost your skills or a beginner eager to dip your toes, grasping the complexities and variety of these champions will prove valuable. Remember, the key to mastering any champion is through understanding, strategic gameplay, and practice. So, dive into the captivating world of LoL and embrace the exciting diversity offered by its champions!
Tips & Guides
Character Guide: Exploring the Champions of League of Legends
The world of gaming is brimming with numerous enthralling experiences, but few can hold a candle to the captivating scenarios laid out in the landscape of League of Legends (LoL). Its widespread acceptance among gaming enthusiasts worldwide and the electrifying gameplay that keeps players on the edge of their seats are largely attributed to its diverse lineup of champions.
From their distinctive abilities to their individual strategic significance, each champion in LoL adds a new dimension to the gameplay. They each possess unique abilities that can be wielded in the game, laying the foundation for an endlessly versatile variety of dynamics in each battle. With each of them fulfilling unique roles that they're tailored for, champions bring specific tactics and strategies to the table, making the gameplay ever-engrossing.
As you get accustomed to the thrilling realm of LoL, an in-depth knowledge of the champions becomes indispensable. This comprehensive guide is designed to provide you with a deeper understanding of the champions, shedding light on their unique abilities, roles, and tactical uses. Furthermore, we'll delve into the various categories champions fall into and the strategic value each holds in the game.
But awareness cannot replace skill. The actual challenge lies in mastering these champions. Every champion requires a different approach and strategy, and understanding alone won't quite cut it. So, we intend to provide tips on mastering them as well, ensuring you can take full advantage of the potential each champion holds.
Understanding the Unique Abilities of Champions
In the exhilarating world of League of Legends, each champion brings a unique personality to the battlefield. And the key factor defining this personality is the distinct set of abilities that each champion possesses. It's these special abilities that carve out the champion's playstyle, laying the groundwork for their approach and tactics when venturing into the battlefield.
The abilities of champions demonstrate a diverse range, each serving different purposes in the match. They are typically categorized as 'Passive,' 'Q,' 'W,' 'E,' and 'Ultimate.' Understanding these categories is critical to comprehending a champion's capabilities and knowing how to strategize effectively during the game.
The 'Passive' ability is a champion's fundamental attribute, which is inherently enabled during the game. It does not require any command to activate and remains operational, emphasizing the inherent nature or the core strength of the champion throughout.
The 'Q,' 'W,' and 'E' signify the basic abilities that every champion possesses. These abilities play a significant role during the fiercely fought battles. Choose the right moments to deploy and upgrade these abilities, for they hold the potential to shift the balance of the game. The upgrade of these abilities happens during the course of the match, progressively increasing the champion's power and tactics.
Above all, we have the 'Ultimate' ability - the ace up the champion's sleeve. This ability is the champion's strongest asset and, thus, is available only after reaching a particular level. Unleashing the Ultimate ability can turn the tide of the match, making it a valuable weapon to wield at the right moment.
Roles of Champions in Gameplay
While each champion in League of Legends brings unique abilities to the table, they are also defined by the roles they play within the gaming environment. These roles, distinguished by a versatile range of objectives and skills, are crucial to understanding and utilizing the champions to their fullest potential. The primary roles we encounter within the game are 'Attack Damage Carry (ADC),' 'Support,' 'Mid,' 'Top,' and 'Jungle.'
The ADC, or 'Attack Damage Carry,' embodies a powerful figure in the gaming field. Often paired with the Support, their task is to deal notable damage, especially as the game reaches its later stages. Their power grows gradually through the game, and they are the cornerstone of the team's offensive strategies when they reach their peak power level at the end of the game.
The 'Support' champions, as the name aptly suggests, are the team's backbone. Their primary objective is to assist the team in a multitude of ways, but often, their prime responsibility lies in safeguarding the ADC. They contain and mitigate threats to the ADC, enabling them to wreak havoc upon opposing teams unhindered.
'Mid' champions take charge of the mid-lane, a position characterized by independent gameplay. They typically involve champions capable of handling themselves solo, holding the lane steady. The mid-champions can often shift the dynamics of the game through their individual performance in the mid-lane.
'Top' champions, akin to the stalwart defenders in a team, operate largely in isolation from the team. The characteristic feature of their gameplay is their gritty resilience and the ability to soak up damage. Their hardiness allows them to withstand substantial onslaughts, making them formidable opponents in their own right.
Last but hardly least, 'Jungle' champions, much like wildcards in a set, operate without being tied down to a particular lane. They wander the areas between lanes, aptly known as the "jungle," rendering assistance where needed. Their role is fluid and often involves counteracting enemy strategies, providing Support, and seizing opportunities across the game map.
Classification of Champions
Further, champions are classified based on their specific strengths and playing style. The classifications are 'Tank,' 'Mage,' 'Fighter,' 'Assassin,' 'Marksman,' and 'Support.' Tank champions have high durability and crowd control abilities, mages are magic damage dealers, and fighters are versatile champions who can both deal and take damage. Assassins specialize in damaging specific targets, marksman champions deal consistent damage from a range, and support champions have abilities to protect and enhance their team.
Getting to Grips with Strategizing
Understanding the facets of champions is not enough; knowing how to use them strategically is key to mastering League of Legends. Each champion is unique, and mastering them requires understanding their strengths and weaknesses. Players have to customize their gameplay according to the champion they use and adapt to their chosen champion's abilities. A strategic approach to each champion's abilities will significantly enhance your game.
Tips to Master Champions
Mastering a champion requires understanding their abilities and also their roles in the game. Start with understanding the champion's abilities and how you can use them during gameplay. Use tutorials and guides to understand how to play the champion efficiently. Practice using the abilities of the champion in various situations during the game. Try to learn one champion at a time and understand all loopholes and gameplay strategies with that champion before moving to the next.
Final Words
League of Legends champions, with their diverse abilities and roles, add significant strategic depth to the gameplay. Regardless if you are an experienced gamer wanting to boost your skills or a beginner eager to dip your toes, grasping the complexities and variety of these champions will prove valuable. Remember, the key to mastering any champion is through understanding, strategic gameplay, and practice. So, dive into the captivating world of LoL and embrace the exciting diversity offered by its champions!
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-07-23
Ethan Blackstone
2024-07-23

![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-07-20
Ethan Blackstone
2024-07-20
![Latanskiy Nick Latanskiy Nick]() Latanskiy Nick
2024-05-30
Latanskiy Nick
2024-05-30
![Ava Reynolds Ava Reynolds]() Ava Reynolds
2024-05-30
Ava Reynolds
2024-05-30
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-05-30
Ethan Blackstone
2024-05-30
![Latanskiy Nick Latanskiy Nick]() Latanskiy Nick
2024-05-30
Latanskiy Nick
2024-05-30
![Ava Reynolds Ava Reynolds]() Ava Reynolds
2024-05-30
Ava Reynolds
2024-05-30
![CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025 CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025]() News
CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025
In 2021, Radical Fish Games initially introduced a new action RPG titled Project Terra. Now, they have officially named it Alabaster Dawn and announced that it will be available in Steam Early Access in late 2025.
The narrative centers around Juno, referred to as the “Outcast Chosen.” She awakens to find herself in a devastated world and embarks on a quest to revive humanity while confronting the enigmatic Nyx, who seems to be linked to the calamity that has befallen civilization. Fans of CrossCode will recognize familiar elements in the combat mechanics, world layout, and platforming aspects. The traditional four elemental forces return, but players now have access to eight distinct weapons.
Each of the four elements corresponds to two different weapons, allowing for a flexible combat experience. Additionally, the game will feature Combat Arts, which offers a range of techniques to use in battles, along with brand-new Divine Arts. Participants will be able to explore the expansive terrain, collect an assortment of precious Stones, obtain resources for upgrades, and discover culinary formulas that enable them to create dishes providing short-term advantages.
While Alabaster Dawn does not have a specific release date set yet, it has been confirmed for future availability on consoles and PC, creating excitement within the gaming community.
News
CrossCode Developer Announces Alabaster Dawn, Enters Early Access in Late 2025
In 2021, Radical Fish Games initially introduced a new action RPG titled Project Terra. Now, they have officially named it Alabaster Dawn and announced that it will be available in Steam Early Access in late 2025.
The narrative centers around Juno, referred to as the “Outcast Chosen.” She awakens to find herself in a devastated world and embarks on a quest to revive humanity while confronting the enigmatic Nyx, who seems to be linked to the calamity that has befallen civilization. Fans of CrossCode will recognize familiar elements in the combat mechanics, world layout, and platforming aspects. The traditional four elemental forces return, but players now have access to eight distinct weapons.
Each of the four elements corresponds to two different weapons, allowing for a flexible combat experience. Additionally, the game will feature Combat Arts, which offers a range of techniques to use in battles, along with brand-new Divine Arts. Participants will be able to explore the expansive terrain, collect an assortment of precious Stones, obtain resources for upgrades, and discover culinary formulas that enable them to create dishes providing short-term advantages.
While Alabaster Dawn does not have a specific release date set yet, it has been confirmed for future availability on consoles and PC, creating excitement within the gaming community.
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-08-12
Ethan Blackstone
2024-08-12
![Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO]() News
Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO
Despite its lackluster reception, Battlefield 2042 hasn't deterred EA from its commitment to the franchise. The company is channeling considerable resources into the next installment, with several of its studios collaborating on the project. Although specific details remain sparse, EA's CEO Andrew Wilson recently shared insights about what lies ahead for the Battlefield series.
During a quarterly earnings call, Wilson characterized the forthcoming game as one of EA’s most ambitious endeavors to date. He expressed confidence in the development team, stating that their goal is to create an immersive Battlefield experience that excites the player community. The enthusiasm around the project, according to Wilson, signals strong support for the team’s direction.
An array of studios is contributing to the Battlefield effort. Lead developer DICE is at the forefront, while Criterion Games is set to handle the single-player campaign after the dissolution of Ridgeline Games earlier this year. Additionally, the acclaimed Motive Studio is assembling a new team to support the game's development.
According to earlier reports, the upcoming Battlefield title is on track for release in October 2025. Meanwhile, Ripple Effect Studios is believed to be crafting a separate free-to-play battle royale experience within the franchise, further expanding its offerings.
News
Next Battlefield is “One of the Most Ambitious Projects in Our History” – EA CEO
Despite its lackluster reception, Battlefield 2042 hasn't deterred EA from its commitment to the franchise. The company is channeling considerable resources into the next installment, with several of its studios collaborating on the project. Although specific details remain sparse, EA's CEO Andrew Wilson recently shared insights about what lies ahead for the Battlefield series.
During a quarterly earnings call, Wilson characterized the forthcoming game as one of EA’s most ambitious endeavors to date. He expressed confidence in the development team, stating that their goal is to create an immersive Battlefield experience that excites the player community. The enthusiasm around the project, according to Wilson, signals strong support for the team’s direction.
An array of studios is contributing to the Battlefield effort. Lead developer DICE is at the forefront, while Criterion Games is set to handle the single-player campaign after the dissolution of Ridgeline Games earlier this year. Additionally, the acclaimed Motive Studio is assembling a new team to support the game's development.
According to earlier reports, the upcoming Battlefield title is on track for release in October 2025. Meanwhile, Ripple Effect Studios is believed to be crafting a separate free-to-play battle royale experience within the franchise, further expanding its offerings.
![Ava Reynolds Ava Reynolds]() Ava Reynolds
2024-08-07
Ava Reynolds
2024-08-07
![Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges” Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges”]() News
Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges”
Marvel Rivals is shaping up to be an exciting entry into the hero shooter genre, thanks in part to its well-established branding and the unique capabilities it brings to the table. The game boasts an impressive lineup of playable characters, each equipped with diverse moves and skills. However, this variety has presented some hurdles for the development team at NetEase Games.
In a recent discussion with GamingBolt, the developers revealed that balancing the experience while ensuring every character feels distinct has been a significant challenge—especially concerning melee-heavy heroes like Thor, Spider-Man, and the Incredible Hulk. If not properly handled, the dynamic of close-quarters combat could lead to chaotic gameplay that might detract from the enjoyment.
The developers articulated their struggle, emphasizing that crafting a diverse set of melee combatants was a top priority. They noted that mishandling these characters could result in battles lacking substance, ultimately compromising the gaming experience.
Yet, the unique abilities of the Marvel roster also presented exciting opportunities for the developers. They explained how the Hulk's impressive leaping ability was designed to impact aerial foes, adding an interesting layer to his play style. Venom's symbiotic traits were expanded to allow for mid-range attacks, while Spider-Man’s agility enables fluid transitions between melee and ranged encounters.
By focusing on each hero's strengths, the team aims to create a captivating gameplay experience that highlights each character’s unique mechanics.
Marvel Rivals is currently under development for PS5, Xbox Series X/S, and PC, with no confirmed release date available at this time.
News
Marvel Rivals Developer Says Designing Melee-Based Heroes Has Been “One of Our Greatest Challenges”
Marvel Rivals is shaping up to be an exciting entry into the hero shooter genre, thanks in part to its well-established branding and the unique capabilities it brings to the table. The game boasts an impressive lineup of playable characters, each equipped with diverse moves and skills. However, this variety has presented some hurdles for the development team at NetEase Games.
In a recent discussion with GamingBolt, the developers revealed that balancing the experience while ensuring every character feels distinct has been a significant challenge—especially concerning melee-heavy heroes like Thor, Spider-Man, and the Incredible Hulk. If not properly handled, the dynamic of close-quarters combat could lead to chaotic gameplay that might detract from the enjoyment.
The developers articulated their struggle, emphasizing that crafting a diverse set of melee combatants was a top priority. They noted that mishandling these characters could result in battles lacking substance, ultimately compromising the gaming experience.
Yet, the unique abilities of the Marvel roster also presented exciting opportunities for the developers. They explained how the Hulk's impressive leaping ability was designed to impact aerial foes, adding an interesting layer to his play style. Venom's symbiotic traits were expanded to allow for mid-range attacks, while Spider-Man’s agility enables fluid transitions between melee and ranged encounters.
By focusing on each hero's strengths, the team aims to create a captivating gameplay experience that highlights each character’s unique mechanics.
Marvel Rivals is currently under development for PS5, Xbox Series X/S, and PC, with no confirmed release date available at this time.
![Latanskiy Nick Latanskiy Nick]() Latanskiy Nick
2024-08-05
Latanskiy Nick
2024-08-05

![Out of the shadows and into the light: Embracing responsible AI practices amid bias and hallucinations Out of the shadows and into the light: Embracing responsible AI practices amid bias and hallucinations]() Editor’s Choice
Out of the shadows and into the light: Embracing responsible AI practices amid bias and hallucinations
The path to widespread AI is a bumpy one. While its potential to enhance consumer experiences and streamline business operations through personalization, autonomy, and decentralized reasoning is evident, the technology comes with inherent risks. AI can produce conclusions that aren’t true, spread misinformation and in some cases, perpetuate existing biases. This -- the darker side of AI’s impact -- can leave business leaders facing financial, legal, and reputational damage.
Lost in the Digital Dream
AI is prone to hallucinations. These are instances where models draw a conclusion that while coherent, are detached from reality or from the input’s context. Similar to a human hallucination, AI can experience a digital mirage, blurring the lines between what’s real and what’s not. For instance, ChatGPT’s earlier version once responded to a neuroscientist that the Golden Gate Bridge was moved across Egypt in 2016. Such imaginative and unexpected outputs serve as a reminder that AI’s conclusions are not immune to errors or misinterpretations.
But not all AI hallucinations will be this harmless. Businesses that rely on flawed AI outputs may be left with costly errors. In critical sectors like healthcare, this can quickly become a matter of life or death. Imagine a scenario where an AI system is designed to detect heart conditions. If the AI hallucinates a heartbeat irregularity, incorrect diagnosis could occur, resulting in unnecessary medical interventions and endangering patient safety.
Bias in AI Models
Problems also arise when AI models are based on biased datasets. Previously, Amazon used an AI-based recruitment tool to help hire employees. The AI tool had been trained on a data set that reflected historical and societal inequities which may exist even if normalized by removing those factors. Rather than helping to find the best candidates, the AI inadvertently discriminated against female applicants, systematically rejecting their resumes. Far from identifying the best candidates, the tool perpetuated existing inequities. This example highlights not only the reproduction of real-world biases in AI systems, but also the amplification of those biases, potentially worsening future outcomes. The absence of comprehensive regulations around AI can exacerbate these mistakes, leaving businesses without clear directives on prevention.
As a result of hallucinations and biases, businesses can face lawsuits for negligence or discrimination, resulting in fines. Financial losses may arise from erroneous decisions and missed opportunities, while an untrustworthy AI model can drive customers away. These issues could leave organizations deeming AI as too risky, abandoning projects they had planned. In cases where uses of AI would increase productivity, these projects being dropped might leave staff with extra work.
RAG to the Rescue
Despite the inherent challenges, AI offers significant opportunities for businesses. By adopting the appropriate tools, models, and best practices, companies can effectively address potential issues and fully leverage AI's capabilities. Techniques like retrieval-augmented generation (RAG) are instrumental in tackling problems related to bias, fairness, and hallucinations. RAG models integrate retrieval mechanisms that enable access to extensive, diverse, and pertinent data. Leveraging a wide array of sources helps these models reduce the impact of biases found in smaller or more restricted datasets.
RAG models also excel at generating responses that are grounded in verifiable information. This can eliminate AI hallucinations, providing data inputs that are enriched with context-specific information and retrieved from reliable sources. This means RAG models can be fine-tuned for specific tasks or use-cases, benefiting users by providing information that is unique to their situation. This is especially useful for businesses that don’t have the time or budget to retrain AI models with domain-specific datasets.
In the recruiting example above, RAG can help inform the model with newer hiring guidelines, HR policies and equal employment opportunity laws, ensuring a broad and balanced approach for all candidates to receive fair and equal treatment.
Practical Applications of RAG
Beyond retrieving relevant information, businesses also benefit from RAG models’ ability to generate a natural response. Interactions with these models will generally be more conversational and user friendly. This is particularly useful for customer facing applications. RAG models should form a key part of a modern data approach. To enhance their effectiveness, RAG models require access to real-time data to ensure that information is as fresh and as accurate as possible. They should also be paired with an operational data store that holds information in high-dimensional mathematical vectors. Models can therefore convert a user’s query into numerical vectors when asked, allowing the AI to respond to relevant text inquiries even if they don’t precisely match the original terms or phrases.
By using real-time data and databases that operate in vectors, AI model outputs remain up-to-date, reducing the risk of outdated information leading to hallucinations.
Heading Towards a Brighter Future
As we embark on the journey towards AI’s widespread adoption, organizations must be aware of the consequences of AI gone wrong. A comprehensive approach to AI is crucial. This paves the way for ethical, fair, and secure AI systems that enhance productivity and personalization without propagating misinformation. By prioritizing responsible AI practices, such as employing RAG models, businesses ensure AI remains a positive force in society, rather than something to be feared.
Editor’s Choice
Out of the shadows and into the light: Embracing responsible AI practices amid bias and hallucinations
The path to widespread AI is a bumpy one. While its potential to enhance consumer experiences and streamline business operations through personalization, autonomy, and decentralized reasoning is evident, the technology comes with inherent risks. AI can produce conclusions that aren’t true, spread misinformation and in some cases, perpetuate existing biases. This -- the darker side of AI’s impact -- can leave business leaders facing financial, legal, and reputational damage.
Lost in the Digital Dream
AI is prone to hallucinations. These are instances where models draw a conclusion that while coherent, are detached from reality or from the input’s context. Similar to a human hallucination, AI can experience a digital mirage, blurring the lines between what’s real and what’s not. For instance, ChatGPT’s earlier version once responded to a neuroscientist that the Golden Gate Bridge was moved across Egypt in 2016. Such imaginative and unexpected outputs serve as a reminder that AI’s conclusions are not immune to errors or misinterpretations.
But not all AI hallucinations will be this harmless. Businesses that rely on flawed AI outputs may be left with costly errors. In critical sectors like healthcare, this can quickly become a matter of life or death. Imagine a scenario where an AI system is designed to detect heart conditions. If the AI hallucinates a heartbeat irregularity, incorrect diagnosis could occur, resulting in unnecessary medical interventions and endangering patient safety.
Bias in AI Models
Problems also arise when AI models are based on biased datasets. Previously, Amazon used an AI-based recruitment tool to help hire employees. The AI tool had been trained on a data set that reflected historical and societal inequities which may exist even if normalized by removing those factors. Rather than helping to find the best candidates, the AI inadvertently discriminated against female applicants, systematically rejecting their resumes. Far from identifying the best candidates, the tool perpetuated existing inequities. This example highlights not only the reproduction of real-world biases in AI systems, but also the amplification of those biases, potentially worsening future outcomes. The absence of comprehensive regulations around AI can exacerbate these mistakes, leaving businesses without clear directives on prevention.
As a result of hallucinations and biases, businesses can face lawsuits for negligence or discrimination, resulting in fines. Financial losses may arise from erroneous decisions and missed opportunities, while an untrustworthy AI model can drive customers away. These issues could leave organizations deeming AI as too risky, abandoning projects they had planned. In cases where uses of AI would increase productivity, these projects being dropped might leave staff with extra work.
RAG to the Rescue
Despite the inherent challenges, AI offers significant opportunities for businesses. By adopting the appropriate tools, models, and best practices, companies can effectively address potential issues and fully leverage AI's capabilities. Techniques like retrieval-augmented generation (RAG) are instrumental in tackling problems related to bias, fairness, and hallucinations. RAG models integrate retrieval mechanisms that enable access to extensive, diverse, and pertinent data. Leveraging a wide array of sources helps these models reduce the impact of biases found in smaller or more restricted datasets.
RAG models also excel at generating responses that are grounded in verifiable information. This can eliminate AI hallucinations, providing data inputs that are enriched with context-specific information and retrieved from reliable sources. This means RAG models can be fine-tuned for specific tasks or use-cases, benefiting users by providing information that is unique to their situation. This is especially useful for businesses that don’t have the time or budget to retrain AI models with domain-specific datasets.
In the recruiting example above, RAG can help inform the model with newer hiring guidelines, HR policies and equal employment opportunity laws, ensuring a broad and balanced approach for all candidates to receive fair and equal treatment.
Practical Applications of RAG
Beyond retrieving relevant information, businesses also benefit from RAG models’ ability to generate a natural response. Interactions with these models will generally be more conversational and user friendly. This is particularly useful for customer facing applications. RAG models should form a key part of a modern data approach. To enhance their effectiveness, RAG models require access to real-time data to ensure that information is as fresh and as accurate as possible. They should also be paired with an operational data store that holds information in high-dimensional mathematical vectors. Models can therefore convert a user’s query into numerical vectors when asked, allowing the AI to respond to relevant text inquiries even if they don’t precisely match the original terms or phrases.
By using real-time data and databases that operate in vectors, AI model outputs remain up-to-date, reducing the risk of outdated information leading to hallucinations.
Heading Towards a Brighter Future
As we embark on the journey towards AI’s widespread adoption, organizations must be aware of the consequences of AI gone wrong. A comprehensive approach to AI is crucial. This paves the way for ethical, fair, and secure AI systems that enhance productivity and personalization without propagating misinformation. By prioritizing responsible AI practices, such as employing RAG models, businesses ensure AI remains a positive force in society, rather than something to be feared.
![Latanskiy Nick Latanskiy Nick]() Latanskiy Nick
2024-05-30
Latanskiy Nick
2024-05-30
![Compliance and Cybersecurity in the Age of AI Compliance and Cybersecurity in the Age of AI]() Editor’s Choice
Compliance and Cybersecurity in the Age of AI
Artificial Intelligence is dramatically transforming the business landscape. It streamlines operations, provides critical insights, and empowers businesses to make data-driven decisions efficiently. Utilizing machine learning, predictive analytics, and automation, AI aids in spotting trends, projecting sales, and optimizing supply chains. This results in heightened productivity and enhanced business performance. However, it does come with certain challenges.
Ransomware Threats and AI
We discussed the impact of AI on cybersecurity with Matt Hillary, Vice President of Security and CISO at Drata. According to Hillary, AI is significantly increasing the ransomware threat. Traditional strategies for propagating ransomware rely heavily on social engineering tactics such as phishing and exploiting weaknesses in externally accessible systems like Virtual Private Network (VPN) endpoints and exposed Remote Desktop Protocol (RDP). AI is enabling cyber attackers to produce highly sophisticated deceptive messages, making them more tempting to the unaware user.
Cybercriminals are leveraging AI to improve various facets of their activities, including reconnaissance and coding, which strengthens their exploitation vectors. By using AI, threat actors can efficiently analyze extensive datasets to identify weaknesses in an organization’s external systems and create tailored exploits, whether by exploiting known vulnerabilities or uncovering new ones.
Defensive and Preventative AI Solutions
On the flip side, AI is also enhancing defensive and preventative solutions in cybersecurity. AI-driven systems can sift through extensive datasets to identify patterns that signal potential cyber threats, such as malware, phishing schemes, and irregular network behavior. Large Language Models (LLMs) can identify indicators of compromise or other threats more quickly and accurately than traditional or manual review methods, allowing for a faster response and mitigation.
AI models can also review activities to understand the normal behavior of users and systems within a network, enabling them to detect deviations that may indicate a security incident. This method is especially useful for detecting insider threats and complex attacks that manage to bypass conventional signature-based detection systems.
Automating Governance and Compliance
AI tools have the potential to significantly enhance governance and compliance with evolving regulations and industry standards. By continuously monitoring systems and detecting anomalies, AI can respond to indicators of security incidents or misconfigurations that could result in non-compliance. These tools help organizations stay current and compliant by keeping up with evolving governance regulations in real-time.
Moreover, AI algorithms can analyze vast amounts of regulatory data, reducing the risk of human error associated with manual efforts. This leads to more accurate assessments of compliance status and reduces the likelihood of regulatory violations, providing a more robust compliance framework.
Best Practices for Protecting Against AI Threats
To protect against evolving AI threats, leaders should implement several practical and best practices. Comprehensive education for cybersecurity teams is crucial to effectively secure AI used by employees and AI integrated into existing platforms or systems. This education should cover not only the application but also the underlying technology driving AI capabilities.
Organizations should deploy phishing-resistant authentication methods to safeguard against phishing attacks targeting authentication tokens used for accessing environments. Additionally, policies, training, and automated mechanisms should be established to equip team members with the knowledge to defend against social engineering attacks.
Consistently strengthening the organization’s internet-facing perimeters and internal networks is essential to diminish the effectiveness of such attacks, ensuring a more secure environment against AI-driven threats.
Ethical Considerations and Practical Safety Actions
Ethical considerations are paramount when it comes to AI. Companies should establish governance structures and processes to oversee AI development, deployment, and usage. This includes appointing individuals or committees responsible for monitoring ethical compliance and ensuring alignment with organizational values. These governance structures should be extensively documented and understood across the organization.
Transparency is also crucial. Organizations should document AI algorithms, data sources, and decision-making processes, ensuring that stakeholders understand how AI systems make decisions and their potential impacts on individuals and society. At Drata, responsible AI principles have been developed to encourage robust, trusted, ethical governance while maintaining a strong security posture.
Key principles include privacy by design, which involves using anonymized datasets to safeguard privacy with strict access control and encryption protocols, alongside synthetic data generation to simulate compliance scenarios. Fairness and inclusivity are promoted by removing inherent biases through detailed curation and continuous monitoring of models to ensure no unfair outcomes. Safety and reliability are ensured through rigorous testing and 360-degree human oversight, providing users with total confidence in AI solutions.
The Future of AI Threats
The future holds both challenges and opportunities in the realm of AI threats. With increasing accessibility and potency of AI, malicious actors will inevitably exploit it to orchestrate highly targeted, automated, and elusive cyberattacks across multiple domains. These attacks will evolve in real-time, enabling them to evade traditional detection methods.
Additionally, the rise of AI-generated deep-fakes and misinformation poses significant threats to individuals, organizations, and the democratic process. Fake visuals, audio, and text are becoming increasingly sophisticated, making it difficult to distinguish between fact and fiction.
Advanced AI-Driven Security Solutions
Despite the challenges, the future of advanced AI-driven security solutions is promising. AI will bolster cybersecurity resilience through proactive threat intelligence, predictive analytics, and adaptive security controls. By using AI to foresee and adjust to emerging threats, organizations can maintain a proactive stance against cyber criminals, mitigating the impact of attacks.
Third-party risk management is also critical in addressing AI-powered vulnerabilities. Security teams need comprehensive tools for identifying, assessing, and continuously monitoring risks, integrating them with internal risk profiles. This holistic approach ensures a unified, clear view of potential exposures across the entire organization, effectively managing third-party risks associated with AI.
Editor’s Choice
Compliance and Cybersecurity in the Age of AI
Artificial Intelligence is dramatically transforming the business landscape. It streamlines operations, provides critical insights, and empowers businesses to make data-driven decisions efficiently. Utilizing machine learning, predictive analytics, and automation, AI aids in spotting trends, projecting sales, and optimizing supply chains. This results in heightened productivity and enhanced business performance. However, it does come with certain challenges.
Ransomware Threats and AI
We discussed the impact of AI on cybersecurity with Matt Hillary, Vice President of Security and CISO at Drata. According to Hillary, AI is significantly increasing the ransomware threat. Traditional strategies for propagating ransomware rely heavily on social engineering tactics such as phishing and exploiting weaknesses in externally accessible systems like Virtual Private Network (VPN) endpoints and exposed Remote Desktop Protocol (RDP). AI is enabling cyber attackers to produce highly sophisticated deceptive messages, making them more tempting to the unaware user.
Cybercriminals are leveraging AI to improve various facets of their activities, including reconnaissance and coding, which strengthens their exploitation vectors. By using AI, threat actors can efficiently analyze extensive datasets to identify weaknesses in an organization’s external systems and create tailored exploits, whether by exploiting known vulnerabilities or uncovering new ones.
Defensive and Preventative AI Solutions
On the flip side, AI is also enhancing defensive and preventative solutions in cybersecurity. AI-driven systems can sift through extensive datasets to identify patterns that signal potential cyber threats, such as malware, phishing schemes, and irregular network behavior. Large Language Models (LLMs) can identify indicators of compromise or other threats more quickly and accurately than traditional or manual review methods, allowing for a faster response and mitigation.
AI models can also review activities to understand the normal behavior of users and systems within a network, enabling them to detect deviations that may indicate a security incident. This method is especially useful for detecting insider threats and complex attacks that manage to bypass conventional signature-based detection systems.
Automating Governance and Compliance
AI tools have the potential to significantly enhance governance and compliance with evolving regulations and industry standards. By continuously monitoring systems and detecting anomalies, AI can respond to indicators of security incidents or misconfigurations that could result in non-compliance. These tools help organizations stay current and compliant by keeping up with evolving governance regulations in real-time.
Moreover, AI algorithms can analyze vast amounts of regulatory data, reducing the risk of human error associated with manual efforts. This leads to more accurate assessments of compliance status and reduces the likelihood of regulatory violations, providing a more robust compliance framework.
Best Practices for Protecting Against AI Threats
To protect against evolving AI threats, leaders should implement several practical and best practices. Comprehensive education for cybersecurity teams is crucial to effectively secure AI used by employees and AI integrated into existing platforms or systems. This education should cover not only the application but also the underlying technology driving AI capabilities.
Organizations should deploy phishing-resistant authentication methods to safeguard against phishing attacks targeting authentication tokens used for accessing environments. Additionally, policies, training, and automated mechanisms should be established to equip team members with the knowledge to defend against social engineering attacks.
Consistently strengthening the organization’s internet-facing perimeters and internal networks is essential to diminish the effectiveness of such attacks, ensuring a more secure environment against AI-driven threats.
Ethical Considerations and Practical Safety Actions
Ethical considerations are paramount when it comes to AI. Companies should establish governance structures and processes to oversee AI development, deployment, and usage. This includes appointing individuals or committees responsible for monitoring ethical compliance and ensuring alignment with organizational values. These governance structures should be extensively documented and understood across the organization.
Transparency is also crucial. Organizations should document AI algorithms, data sources, and decision-making processes, ensuring that stakeholders understand how AI systems make decisions and their potential impacts on individuals and society. At Drata, responsible AI principles have been developed to encourage robust, trusted, ethical governance while maintaining a strong security posture.
Key principles include privacy by design, which involves using anonymized datasets to safeguard privacy with strict access control and encryption protocols, alongside synthetic data generation to simulate compliance scenarios. Fairness and inclusivity are promoted by removing inherent biases through detailed curation and continuous monitoring of models to ensure no unfair outcomes. Safety and reliability are ensured through rigorous testing and 360-degree human oversight, providing users with total confidence in AI solutions.
The Future of AI Threats
The future holds both challenges and opportunities in the realm of AI threats. With increasing accessibility and potency of AI, malicious actors will inevitably exploit it to orchestrate highly targeted, automated, and elusive cyberattacks across multiple domains. These attacks will evolve in real-time, enabling them to evade traditional detection methods.
Additionally, the rise of AI-generated deep-fakes and misinformation poses significant threats to individuals, organizations, and the democratic process. Fake visuals, audio, and text are becoming increasingly sophisticated, making it difficult to distinguish between fact and fiction.
Advanced AI-Driven Security Solutions
Despite the challenges, the future of advanced AI-driven security solutions is promising. AI will bolster cybersecurity resilience through proactive threat intelligence, predictive analytics, and adaptive security controls. By using AI to foresee and adjust to emerging threats, organizations can maintain a proactive stance against cyber criminals, mitigating the impact of attacks.
Third-party risk management is also critical in addressing AI-powered vulnerabilities. Security teams need comprehensive tools for identifying, assessing, and continuously monitoring risks, integrating them with internal risk profiles. This holistic approach ensures a unified, clear view of potential exposures across the entire organization, effectively managing third-party risks associated with AI.
![Latanskiy Nick Latanskiy Nick]() Latanskiy Nick
2024-05-30
Latanskiy Nick
2024-05-30
![How to Fix the V Rising Authentication Error How to Fix the V Rising Authentication Error]() Editor’s Choice
How to Fix the V Rising Authentication Error
Even though V Rising was released after years of early access, players can still find errors in it. And some incredibly annoying ones can ruin your gaming experience. Therefore, we will tell you how to fix the Authentication Error in V Rising in this guide. After the full release, this error is quite rare in the game. However, if you notice it on your screen, you should not be upset, as there are several ways to get rid of it quickly.
Understanding the Authentication Error
First, you need to know that the Authentication Error in V Rising can happen for several reasons, namely problems with connecting to the server or the server being overloaded with players. As a result, all you can do is leave the game or return to the main menu. Fortunately, you can fix the Authentication Error in V Rising quickly by using one of the methods below:
Check Server Status
Like any other multiplayer game, V Rising sometimes may have server issues. To check this, you just need to visit the X page of the game. If the servers are down, you will have to wait for the developers to fix it. If there are no messages about server issues, then the problem is on your side.
Check the Server for Player Overload
Players just need to connect to another V Rising server to do this. Of course, your progress will stay in the new world. But if you can connect to it without the Authentication Error in V Rising, then you just have to wait until the number of players on your main server decreases.
Check Your Internet Connection
In rare cases, an Authentication Error may occur in V Rising due to a bad internet connection. To check this, you need to try running another online game. If no similar errors occur, move on to the following method.
Update or Reinstall V Rising
When developers release new patches, you should always update V Rising before starting the game. It will help you avoid plenty of errors and bugs. Another viable option is to reinstall the game. Even though this is a trivial and simple way, it often helps eliminate annoying problems, including Authentication Error in V Rising.
Steps to Ensure Smooth Gameplay
Ensuring smooth gameplay in V Rising involves more than just addressing the Authentication Error. Here are some additional steps to enhance your overall experience:
Optimize Game Settings
Adjusting in-game settings can significantly improve performance. Lowering the graphics quality, disabling unnecessary features, and tweaking network settings can contribute to a smoother experience. Also, regularly updating your graphics drivers can prevent crashes and errors.
Maintain a Stable Internet Connection
A stable internet connection is crucial for any online game. Ensure that your router firmware is updated, and consider using a wired connection for a more consistent network experience. Additionally, avoid bandwidth-heavy activities like streaming while gaming.
Regular System Maintenance
Regularly updating your operating system and drivers can prevent compatibility issues with V Rising. It’s also wise to perform routine system checks for malware and unnecessary background applications that may consume resources.
Community and Developer Support
Joining V Rising’s community forums and following developer updates can keep you informed about common issues and their fixes. Developers often release hotfixes and patches based on community feedback, so staying engaged can be beneficial.
When All Else Fails
If none of these methods work, all you can do is wait for the update from the developers. They still release patches with bug fixes from time to time. Patience is key, and keeping an eye on official announcements will keep you prepared for upcoming fixes.
Contacting Support
If you’ve exhausted all troubleshooting steps and still face the Authentication Error, consider reaching out to V Rising’s support team. Providing detailed information about your issue can expedite the resolution process.
Re-Evaluating Your Setup
Sometimes, persistent issues might indicate a deeper problem with your hardware or software setup. Re-evaluating your gaming setup, including hardware specifications and software configurations, might reveal underlying issues that need addressing.
Conclusion
While encountering the Authentication Error in V Rising can be frustrating, various strategies can help resolve the issue. By checking server status, ensuring a stable internet connection, updating the game, and maintaining your system, you can enhance your gaming experience. Remember, staying informed through community and developer channels is crucial for timely updates and fixes. If all else fails, reaching out to support and re-evaluating your setup may provide a solution. Happy gaming!
Editor’s Choice
How to Fix the V Rising Authentication Error
Even though V Rising was released after years of early access, players can still find errors in it. And some incredibly annoying ones can ruin your gaming experience. Therefore, we will tell you how to fix the Authentication Error in V Rising in this guide. After the full release, this error is quite rare in the game. However, if you notice it on your screen, you should not be upset, as there are several ways to get rid of it quickly.
Understanding the Authentication Error
First, you need to know that the Authentication Error in V Rising can happen for several reasons, namely problems with connecting to the server or the server being overloaded with players. As a result, all you can do is leave the game or return to the main menu. Fortunately, you can fix the Authentication Error in V Rising quickly by using one of the methods below:
Check Server Status
Like any other multiplayer game, V Rising sometimes may have server issues. To check this, you just need to visit the X page of the game. If the servers are down, you will have to wait for the developers to fix it. If there are no messages about server issues, then the problem is on your side.
Check the Server for Player Overload
Players just need to connect to another V Rising server to do this. Of course, your progress will stay in the new world. But if you can connect to it without the Authentication Error in V Rising, then you just have to wait until the number of players on your main server decreases.
Check Your Internet Connection
In rare cases, an Authentication Error may occur in V Rising due to a bad internet connection. To check this, you need to try running another online game. If no similar errors occur, move on to the following method.
Update or Reinstall V Rising
When developers release new patches, you should always update V Rising before starting the game. It will help you avoid plenty of errors and bugs. Another viable option is to reinstall the game. Even though this is a trivial and simple way, it often helps eliminate annoying problems, including Authentication Error in V Rising.
Steps to Ensure Smooth Gameplay
Ensuring smooth gameplay in V Rising involves more than just addressing the Authentication Error. Here are some additional steps to enhance your overall experience:
Optimize Game Settings
Adjusting in-game settings can significantly improve performance. Lowering the graphics quality, disabling unnecessary features, and tweaking network settings can contribute to a smoother experience. Also, regularly updating your graphics drivers can prevent crashes and errors.
Maintain a Stable Internet Connection
A stable internet connection is crucial for any online game. Ensure that your router firmware is updated, and consider using a wired connection for a more consistent network experience. Additionally, avoid bandwidth-heavy activities like streaming while gaming.
Regular System Maintenance
Regularly updating your operating system and drivers can prevent compatibility issues with V Rising. It’s also wise to perform routine system checks for malware and unnecessary background applications that may consume resources.
Community and Developer Support
Joining V Rising’s community forums and following developer updates can keep you informed about common issues and their fixes. Developers often release hotfixes and patches based on community feedback, so staying engaged can be beneficial.
When All Else Fails
If none of these methods work, all you can do is wait for the update from the developers. They still release patches with bug fixes from time to time. Patience is key, and keeping an eye on official announcements will keep you prepared for upcoming fixes.
Contacting Support
If you’ve exhausted all troubleshooting steps and still face the Authentication Error, consider reaching out to V Rising’s support team. Providing detailed information about your issue can expedite the resolution process.
Re-Evaluating Your Setup
Sometimes, persistent issues might indicate a deeper problem with your hardware or software setup. Re-evaluating your gaming setup, including hardware specifications and software configurations, might reveal underlying issues that need addressing.
Conclusion
While encountering the Authentication Error in V Rising can be frustrating, various strategies can help resolve the issue. By checking server status, ensuring a stable internet connection, updating the game, and maintaining your system, you can enhance your gaming experience. Remember, staying informed through community and developer channels is crucial for timely updates and fixes. If all else fails, reaching out to support and re-evaluating your setup may provide a solution. Happy gaming!
![Latanskiy Nick Latanskiy Nick]() Latanskiy Nick
2024-05-28
Latanskiy Nick
2024-05-28
![Character Guide: Exploring the Champions of League of Legends Character Guide: Exploring the Champions of League of Legends]() Tips & Guides
Character Guide: Exploring the Champions of League of Legends
The world of gaming is brimming with numerous enthralling experiences, but few can hold a candle to the captivating scenarios laid out in the landscape of League of Legends (LoL). Its widespread acceptance among gaming enthusiasts worldwide and the electrifying gameplay that keeps players on the edge of their seats are largely attributed to its diverse lineup of champions.
From their distinctive abilities to their individual strategic significance, each champion in LoL adds a new dimension to the gameplay. They each possess unique abilities that can be wielded in the game, laying the foundation for an endlessly versatile variety of dynamics in each battle. With each of them fulfilling unique roles that they're tailored for, champions bring specific tactics and strategies to the table, making the gameplay ever-engrossing.
As you get accustomed to the thrilling realm of LoL, an in-depth knowledge of the champions becomes indispensable. This comprehensive guide is designed to provide you with a deeper understanding of the champions, shedding light on their unique abilities, roles, and tactical uses. Furthermore, we'll delve into the various categories champions fall into and the strategic value each holds in the game.
But awareness cannot replace skill. The actual challenge lies in mastering these champions. Every champion requires a different approach and strategy, and understanding alone won't quite cut it. So, we intend to provide tips on mastering them as well, ensuring you can take full advantage of the potential each champion holds.
Understanding the Unique Abilities of Champions
In the exhilarating world of League of Legends, each champion brings a unique personality to the battlefield. And the key factor defining this personality is the distinct set of abilities that each champion possesses. It's these special abilities that carve out the champion's playstyle, laying the groundwork for their approach and tactics when venturing into the battlefield.
The abilities of champions demonstrate a diverse range, each serving different purposes in the match. They are typically categorized as 'Passive,' 'Q,' 'W,' 'E,' and 'Ultimate.' Understanding these categories is critical to comprehending a champion's capabilities and knowing how to strategize effectively during the game.
The 'Passive' ability is a champion's fundamental attribute, which is inherently enabled during the game. It does not require any command to activate and remains operational, emphasizing the inherent nature or the core strength of the champion throughout.
The 'Q,' 'W,' and 'E' signify the basic abilities that every champion possesses. These abilities play a significant role during the fiercely fought battles. Choose the right moments to deploy and upgrade these abilities, for they hold the potential to shift the balance of the game. The upgrade of these abilities happens during the course of the match, progressively increasing the champion's power and tactics.
Above all, we have the 'Ultimate' ability - the ace up the champion's sleeve. This ability is the champion's strongest asset and, thus, is available only after reaching a particular level. Unleashing the Ultimate ability can turn the tide of the match, making it a valuable weapon to wield at the right moment.
Roles of Champions in Gameplay
While each champion in League of Legends brings unique abilities to the table, they are also defined by the roles they play within the gaming environment. These roles, distinguished by a versatile range of objectives and skills, are crucial to understanding and utilizing the champions to their fullest potential. The primary roles we encounter within the game are 'Attack Damage Carry (ADC),' 'Support,' 'Mid,' 'Top,' and 'Jungle.'
The ADC, or 'Attack Damage Carry,' embodies a powerful figure in the gaming field. Often paired with the Support, their task is to deal notable damage, especially as the game reaches its later stages. Their power grows gradually through the game, and they are the cornerstone of the team's offensive strategies when they reach their peak power level at the end of the game.
The 'Support' champions, as the name aptly suggests, are the team's backbone. Their primary objective is to assist the team in a multitude of ways, but often, their prime responsibility lies in safeguarding the ADC. They contain and mitigate threats to the ADC, enabling them to wreak havoc upon opposing teams unhindered.
'Mid' champions take charge of the mid-lane, a position characterized by independent gameplay. They typically involve champions capable of handling themselves solo, holding the lane steady. The mid-champions can often shift the dynamics of the game through their individual performance in the mid-lane.
'Top' champions, akin to the stalwart defenders in a team, operate largely in isolation from the team. The characteristic feature of their gameplay is their gritty resilience and the ability to soak up damage. Their hardiness allows them to withstand substantial onslaughts, making them formidable opponents in their own right.
Last but hardly least, 'Jungle' champions, much like wildcards in a set, operate without being tied down to a particular lane. They wander the areas between lanes, aptly known as the "jungle," rendering assistance where needed. Their role is fluid and often involves counteracting enemy strategies, providing Support, and seizing opportunities across the game map.
Classification of Champions
Further, champions are classified based on their specific strengths and playing style. The classifications are 'Tank,' 'Mage,' 'Fighter,' 'Assassin,' 'Marksman,' and 'Support.' Tank champions have high durability and crowd control abilities, mages are magic damage dealers, and fighters are versatile champions who can both deal and take damage. Assassins specialize in damaging specific targets, marksman champions deal consistent damage from a range, and support champions have abilities to protect and enhance their team.
Getting to Grips with Strategizing
Understanding the facets of champions is not enough; knowing how to use them strategically is key to mastering League of Legends. Each champion is unique, and mastering them requires understanding their strengths and weaknesses. Players have to customize their gameplay according to the champion they use and adapt to their chosen champion's abilities. A strategic approach to each champion's abilities will significantly enhance your game.
Tips to Master Champions
Mastering a champion requires understanding their abilities and also their roles in the game. Start with understanding the champion's abilities and how you can use them during gameplay. Use tutorials and guides to understand how to play the champion efficiently. Practice using the abilities of the champion in various situations during the game. Try to learn one champion at a time and understand all loopholes and gameplay strategies with that champion before moving to the next.
Final Words
League of Legends champions, with their diverse abilities and roles, add significant strategic depth to the gameplay. Regardless if you are an experienced gamer wanting to boost your skills or a beginner eager to dip your toes, grasping the complexities and variety of these champions will prove valuable. Remember, the key to mastering any champion is through understanding, strategic gameplay, and practice. So, dive into the captivating world of LoL and embrace the exciting diversity offered by its champions!
Tips & Guides
Character Guide: Exploring the Champions of League of Legends
The world of gaming is brimming with numerous enthralling experiences, but few can hold a candle to the captivating scenarios laid out in the landscape of League of Legends (LoL). Its widespread acceptance among gaming enthusiasts worldwide and the electrifying gameplay that keeps players on the edge of their seats are largely attributed to its diverse lineup of champions.
From their distinctive abilities to their individual strategic significance, each champion in LoL adds a new dimension to the gameplay. They each possess unique abilities that can be wielded in the game, laying the foundation for an endlessly versatile variety of dynamics in each battle. With each of them fulfilling unique roles that they're tailored for, champions bring specific tactics and strategies to the table, making the gameplay ever-engrossing.
As you get accustomed to the thrilling realm of LoL, an in-depth knowledge of the champions becomes indispensable. This comprehensive guide is designed to provide you with a deeper understanding of the champions, shedding light on their unique abilities, roles, and tactical uses. Furthermore, we'll delve into the various categories champions fall into and the strategic value each holds in the game.
But awareness cannot replace skill. The actual challenge lies in mastering these champions. Every champion requires a different approach and strategy, and understanding alone won't quite cut it. So, we intend to provide tips on mastering them as well, ensuring you can take full advantage of the potential each champion holds.
Understanding the Unique Abilities of Champions
In the exhilarating world of League of Legends, each champion brings a unique personality to the battlefield. And the key factor defining this personality is the distinct set of abilities that each champion possesses. It's these special abilities that carve out the champion's playstyle, laying the groundwork for their approach and tactics when venturing into the battlefield.
The abilities of champions demonstrate a diverse range, each serving different purposes in the match. They are typically categorized as 'Passive,' 'Q,' 'W,' 'E,' and 'Ultimate.' Understanding these categories is critical to comprehending a champion's capabilities and knowing how to strategize effectively during the game.
The 'Passive' ability is a champion's fundamental attribute, which is inherently enabled during the game. It does not require any command to activate and remains operational, emphasizing the inherent nature or the core strength of the champion throughout.
The 'Q,' 'W,' and 'E' signify the basic abilities that every champion possesses. These abilities play a significant role during the fiercely fought battles. Choose the right moments to deploy and upgrade these abilities, for they hold the potential to shift the balance of the game. The upgrade of these abilities happens during the course of the match, progressively increasing the champion's power and tactics.
Above all, we have the 'Ultimate' ability - the ace up the champion's sleeve. This ability is the champion's strongest asset and, thus, is available only after reaching a particular level. Unleashing the Ultimate ability can turn the tide of the match, making it a valuable weapon to wield at the right moment.
Roles of Champions in Gameplay
While each champion in League of Legends brings unique abilities to the table, they are also defined by the roles they play within the gaming environment. These roles, distinguished by a versatile range of objectives and skills, are crucial to understanding and utilizing the champions to their fullest potential. The primary roles we encounter within the game are 'Attack Damage Carry (ADC),' 'Support,' 'Mid,' 'Top,' and 'Jungle.'
The ADC, or 'Attack Damage Carry,' embodies a powerful figure in the gaming field. Often paired with the Support, their task is to deal notable damage, especially as the game reaches its later stages. Their power grows gradually through the game, and they are the cornerstone of the team's offensive strategies when they reach their peak power level at the end of the game.
The 'Support' champions, as the name aptly suggests, are the team's backbone. Their primary objective is to assist the team in a multitude of ways, but often, their prime responsibility lies in safeguarding the ADC. They contain and mitigate threats to the ADC, enabling them to wreak havoc upon opposing teams unhindered.
'Mid' champions take charge of the mid-lane, a position characterized by independent gameplay. They typically involve champions capable of handling themselves solo, holding the lane steady. The mid-champions can often shift the dynamics of the game through their individual performance in the mid-lane.
'Top' champions, akin to the stalwart defenders in a team, operate largely in isolation from the team. The characteristic feature of their gameplay is their gritty resilience and the ability to soak up damage. Their hardiness allows them to withstand substantial onslaughts, making them formidable opponents in their own right.
Last but hardly least, 'Jungle' champions, much like wildcards in a set, operate without being tied down to a particular lane. They wander the areas between lanes, aptly known as the "jungle," rendering assistance where needed. Their role is fluid and often involves counteracting enemy strategies, providing Support, and seizing opportunities across the game map.
Classification of Champions
Further, champions are classified based on their specific strengths and playing style. The classifications are 'Tank,' 'Mage,' 'Fighter,' 'Assassin,' 'Marksman,' and 'Support.' Tank champions have high durability and crowd control abilities, mages are magic damage dealers, and fighters are versatile champions who can both deal and take damage. Assassins specialize in damaging specific targets, marksman champions deal consistent damage from a range, and support champions have abilities to protect and enhance their team.
Getting to Grips with Strategizing
Understanding the facets of champions is not enough; knowing how to use them strategically is key to mastering League of Legends. Each champion is unique, and mastering them requires understanding their strengths and weaknesses. Players have to customize their gameplay according to the champion they use and adapt to their chosen champion's abilities. A strategic approach to each champion's abilities will significantly enhance your game.
Tips to Master Champions
Mastering a champion requires understanding their abilities and also their roles in the game. Start with understanding the champion's abilities and how you can use them during gameplay. Use tutorials and guides to understand how to play the champion efficiently. Practice using the abilities of the champion in various situations during the game. Try to learn one champion at a time and understand all loopholes and gameplay strategies with that champion before moving to the next.
Final Words
League of Legends champions, with their diverse abilities and roles, add significant strategic depth to the gameplay. Regardless if you are an experienced gamer wanting to boost your skills or a beginner eager to dip your toes, grasping the complexities and variety of these champions will prove valuable. Remember, the key to mastering any champion is through understanding, strategic gameplay, and practice. So, dive into the captivating world of LoL and embrace the exciting diversity offered by its champions!
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-07-23
Ethan Blackstone
2024-07-23
![Six Steps to Safeguarding Your Digital Identity Six Steps to Safeguarding Your Digital Identity]() Tips & Guides
Six Steps to Safeguarding Your Digital Identity
In today's interconnected world, each data breach chips away at our digital privacy. Consider the notable breach at AT&T, which exposed Social Security numbers and other sensitive personal information, making identity theft a significant threat. Following this incident, the proportion of users with compromised Social Security numbers in our databases skyrocketed from less than 1 percent to nearly 15 percent. The risks are exacerbated when such sensitive information becomes publicly accessible on the internet, not just on the dark web, which requires special software to access. These exposures increase the likelihood of misuse and emphasize the necessity of protecting our digital identities.
The Threat of Identity Theft
The most pressing threat from compromised data is identity theft. Malicious actors can access email, bank, and credit card accounts to impersonate victims. This can involve resetting passwords and taking control of phone numbers to bypass text message confirmations. Furthermore, armed with personal details, thieves might take out loans or credit cards in your name, a common and damaging form of identity theft. The danger extends beyond online fraud; stolen information can lead to physical crimes, putting victims at severe risk. Thus, it is vital to take robust measures to protect against these escalating threats.
1. Use Multi-Factor Authentication Everywhere
Implementing multi-factor authentication (MFA) ubiquitously is paramount in reducing the likelihood of account breaches. Some sources suggest that accounts with MFA are 99.9 percent less likely to be compromised. By requiring additional verification steps, such as codes sent via text, email, or USB authenticator keys, MFA significantly enhances account protection and guards against compromised credentials.
2. Manage Password Risk
Ensure the security of your key online and financial accounts by using distinct, robust, and lengthy passwords. Strive for a minimum of 15 characters, incorporating a blend of uppercase and lowercase letters, numbers, and symbols. Utilize password managers to safely store and handle these intricate passwords, as they can also generate strong passwords for you. Furthermore, consider creating a separate "junk" email for non-essential sign-ups, enhancing security and reducing the potential fallout from data breaches on your primary accounts.
3. Use Protection Across Your Devices
Utilize trusted antivirus (AV) software on both desktop and mobile devices. Many people overlook the importance of AV on their phones, yet these devices often store credit card information and provide access to key accounts. Comprehensive AV protection across all devices is crucial for safeguarding sensitive data.
4. Secure Your Surfing
Be mindful of the information you share online and with whom. Use incognito mode when possible, and provide false information where appropriate. A secondary email address, along with an alternate name, date of birth, and security question answers, can further protect your primary accounts. Additionally, when using public Wi-Fi or even at home, a virtual private network (VPN) can mask your location and encrypt data shared on the local network.
5. Regularly Monitor
Continually monitor your online accounts and finances for suspicious activity. Identity Theft Protection services can help keep your data secure by scanning databases for any instances of your email address being linked to data breaches and alerting you to potential security risks. These services provide an efficient way to stay informed about the status of your personal information.
6. Stay Vigilant
Remain alert to phishing and social engineering schemes, including deceptive emails or calls. Verify suspicious communications by contacting the company or organization directly through their official website, avoiding links or contact information provided in unsolicited messages. Reflect on whether you initiated the contact or if someone reached out to you, and proceed with caution if it’s the latter. Despite best efforts, scams can still occur. Promptly reacting to data breaches can prevent further damage and monetary loss. Identifying and addressing online weak spots, such as predictable passwords or a lack of MFA, is essential for robust identity protection.
Adopting a careful and thorough strategy for safeguarding your identity ensures that even if your information is breached, you have preemptive steps implemented to shield your confidential data. These actions help defend your online presence against cyber hazards, offering reassurance in an ever-more connected world.
Tips & Guides
Six Steps to Safeguarding Your Digital Identity
In today's interconnected world, each data breach chips away at our digital privacy. Consider the notable breach at AT&T, which exposed Social Security numbers and other sensitive personal information, making identity theft a significant threat. Following this incident, the proportion of users with compromised Social Security numbers in our databases skyrocketed from less than 1 percent to nearly 15 percent. The risks are exacerbated when such sensitive information becomes publicly accessible on the internet, not just on the dark web, which requires special software to access. These exposures increase the likelihood of misuse and emphasize the necessity of protecting our digital identities.
The Threat of Identity Theft
The most pressing threat from compromised data is identity theft. Malicious actors can access email, bank, and credit card accounts to impersonate victims. This can involve resetting passwords and taking control of phone numbers to bypass text message confirmations. Furthermore, armed with personal details, thieves might take out loans or credit cards in your name, a common and damaging form of identity theft. The danger extends beyond online fraud; stolen information can lead to physical crimes, putting victims at severe risk. Thus, it is vital to take robust measures to protect against these escalating threats.
1. Use Multi-Factor Authentication Everywhere
Implementing multi-factor authentication (MFA) ubiquitously is paramount in reducing the likelihood of account breaches. Some sources suggest that accounts with MFA are 99.9 percent less likely to be compromised. By requiring additional verification steps, such as codes sent via text, email, or USB authenticator keys, MFA significantly enhances account protection and guards against compromised credentials.
2. Manage Password Risk
Ensure the security of your key online and financial accounts by using distinct, robust, and lengthy passwords. Strive for a minimum of 15 characters, incorporating a blend of uppercase and lowercase letters, numbers, and symbols. Utilize password managers to safely store and handle these intricate passwords, as they can also generate strong passwords for you. Furthermore, consider creating a separate "junk" email for non-essential sign-ups, enhancing security and reducing the potential fallout from data breaches on your primary accounts.
3. Use Protection Across Your Devices
Utilize trusted antivirus (AV) software on both desktop and mobile devices. Many people overlook the importance of AV on their phones, yet these devices often store credit card information and provide access to key accounts. Comprehensive AV protection across all devices is crucial for safeguarding sensitive data.
4. Secure Your Surfing
Be mindful of the information you share online and with whom. Use incognito mode when possible, and provide false information where appropriate. A secondary email address, along with an alternate name, date of birth, and security question answers, can further protect your primary accounts. Additionally, when using public Wi-Fi or even at home, a virtual private network (VPN) can mask your location and encrypt data shared on the local network.
5. Regularly Monitor
Continually monitor your online accounts and finances for suspicious activity. Identity Theft Protection services can help keep your data secure by scanning databases for any instances of your email address being linked to data breaches and alerting you to potential security risks. These services provide an efficient way to stay informed about the status of your personal information.
6. Stay Vigilant
Remain alert to phishing and social engineering schemes, including deceptive emails or calls. Verify suspicious communications by contacting the company or organization directly through their official website, avoiding links or contact information provided in unsolicited messages. Reflect on whether you initiated the contact or if someone reached out to you, and proceed with caution if it’s the latter. Despite best efforts, scams can still occur. Promptly reacting to data breaches can prevent further damage and monetary loss. Identifying and addressing online weak spots, such as predictable passwords or a lack of MFA, is essential for robust identity protection.
Adopting a careful and thorough strategy for safeguarding your identity ensures that even if your information is breached, you have preemptive steps implemented to shield your confidential data. These actions help defend your online presence against cyber hazards, offering reassurance in an ever-more connected world.
![Latanskiy Nick Latanskiy Nick]() Latanskiy Nick
2024-05-27
Latanskiy Nick
2024-05-27
![Roblox: Active Peroxide Codes Roblox: Active Peroxide Codes]() Tips & Guides
Roblox: Active Peroxide Codes
Roblox games like Peroxide occasionally release active codes that give you free rewards, but they can be hard to use without the right context. Inspired by the iconic Bleach series, Peroxide gives you in-game resources through codes provided by the developers. With enough materials, you can buy important items that may help you overcome various struggles throughout your sword-swinging adventure.
Similar to Anime Showdown codes for Roblox, you have to redeem codes before they expire in the future. The timing of when a code expires depends on the developers of Peroxide, but usually, a code only lasts for a few weeks or a month at most. The faster you activate a code phrase, the faster you can claim its free rewards without having to worry about saving it for later.
If you want to know whether certain codes are active or expired, check out the official Discord for Peroxide. This server will also help you see when the developers release new codes you can activate.
How To Use Peroxide Codes In Roblox
Follow Instructions From The Settings
After you start your journey in Peroxide, you can use codes by completing the tutorial and accessing the Settings icon in the top left corner of your screen. Finishing the introduction of the game allows you to start adjusting Settings, where codes can also be activated. Go to the "Settings" tab of Peroxide, where you can see a large blank space with the words "Code Here" that you can click on to get started.
Enter a code phrase into the blank space's text box, but make sure the code still works and doesn't have any grammatical errors. Even one number or letter out of place will be enough to prevent the code from working, causing you to lose out on many rewards. Always make sure to double-check how you've inputted codes before trying to activate them, as many phrases can only be used once by one player.
In a sharp similarity to other Bleach-inspired games like Soul Wars in Roblox, the codes you redeem offer a type of currency called Product Essence in Peroxide. This resource can be collected and taken to the character Kisuke and spent on rerolls for every path available in the game. You can find this NPC in The City, an area you may be familiar with after playing through the tutorial.
Product Essence can also be spent on cosmetic items for your character, giving you new ways to adjust your look as you play. Other items, slots, and accessories are also tied to Product Essence, reflecting how the material is at the core of Peroxide's gameplay. Those looking to explore everything this game has to offer will want to farm as much Essence as they can through codes right as the tutorial finishes.
Every Currently Active Peroxide Code
Share Rewards Across All Saved Slots
Every save slot you have will share Product Essence in one large pool, which prevents you from having to grind on multiple slots for more currency. However, keep in mind that this single collection of Essence can be spent quickly as a result, so you need to plan carefully for what you buy. Once again, codes can only be redeemed once per account, limiting the total Essence you can get at a time before new phrases drop.
Multiple accounts can be made to use a Peroxide active code more than once, but the Product Essence you receive can only be used on the account that redeemed the resources.
As you can see in the above video by YouTube creator Corgi, the message "Already Used Code" will pop up in Peroxide if you have already used a phrase on your account. Even with earned Robux in Roblox, you will be unable to get more of this currency for free until more codes are active. For now, the codes available in the game are:
Active Code
Rewards
SkibiShutdown
30 Product Essence
GokuDayCodeSuper2
15 Product Essence
310KLikesHappyWeekend
25 Product Essence
230MVisitsCodeCritters
25 Product Essence
sorry4thebugs
25 Product Essence
220MVisitsArrancarTerrorism
30 Product Essence
AlvinAndTheChipmunks
30 Product Essence
FusionHoldingUsHostageUpdateIsComing
25 Product Essence
EclipseDontBurnUrEyes
15 Product Essence
330kLikesSorryLate
35 Product Essence
20BILLIONTIRLLCOINDDOIFDSUPERNOTSCAMCODE
Random Amount of Product Essence
TwoTrillionAprilPECode
2 Trillion Product Essence
ShutdownToFixNPCsAgain
25 Product Essence
210MVisitsAwesome
30 Product Essence
PeroxideAnniPE
50 Product Essence
UnluckyBruhxide
50 Product Essence
290kLikesLOOLOLOL
30 Product Essence
200MVisitsAwesome
25 Product Essence
ValentinesDayButNoValentines
45 Product Essence
FusionStopGamblingWorkOnTheGame
25 Product Essence
FusionForgotHowToShutdown
Random amount of Product Essence
190mVisitsThanks
30 Product Essence
ThanksForPingingAhmed
25 Product Essence
280kLikesThankYouForYourSupport
25 Product Essence
180mVistsTrollDelay
20 Product Essence
CodeCrittersVsBugFixers
20 Product Essence
CodeCrittersVsBugFixersPart2
15 Product Essence
StopListeningToTrialMods
25 Product Essence
HappyNewYearJoMamaJoeBiden12121
20 Product Essence
Chungsmas
30 Product Essence
170mVisitsGuys
15 Product Essence
270kLikesOhHowJolly
15 Product Essence
FBBossIncident
15 Product Essence
FBUpdate
15 Product Essence, 1 Slot
How To Check If Codes Have Expired
Look At Multiple Sources
Although simply entering a code and its failure to work could tell you whether it has expired or not, there are some situations where a code not working suddenly activates. To avoid confusion, the best way to see if a code has expired is to check how long it has been operating or see what dates other players report using it. Oftentimes, some codes that others claim to work have long since expired following the phrase's release.
Unfortunately, the developers of Peroxide have not updated many of the codes on their social sites with expiration dates. Unlike many of the most popular Roblox games on the platform right now, it can be hard to tell which codes are working at any moment. Even from the list provided above, there may be some phrases that have expired in the months following this time of writing.
You can always message other players to make sure a certain code does or does not work, but you should always try inputting a phrase multiple times when you get stuck. After a few attempts, accept that one code may be lost and move on to the next one. Figuring out how to use codes for Peroxide in Roblox may cause some struggles here and there if you don't follow the right steps as you go.
Tips & Guides
Roblox: Active Peroxide Codes
Roblox games like Peroxide occasionally release active codes that give you free rewards, but they can be hard to use without the right context. Inspired by the iconic Bleach series, Peroxide gives you in-game resources through codes provided by the developers. With enough materials, you can buy important items that may help you overcome various struggles throughout your sword-swinging adventure.
Similar to Anime Showdown codes for Roblox, you have to redeem codes before they expire in the future. The timing of when a code expires depends on the developers of Peroxide, but usually, a code only lasts for a few weeks or a month at most. The faster you activate a code phrase, the faster you can claim its free rewards without having to worry about saving it for later.
If you want to know whether certain codes are active or expired, check out the official Discord for Peroxide. This server will also help you see when the developers release new codes you can activate.
How To Use Peroxide Codes In Roblox
Follow Instructions From The Settings
After you start your journey in Peroxide, you can use codes by completing the tutorial and accessing the Settings icon in the top left corner of your screen. Finishing the introduction of the game allows you to start adjusting Settings, where codes can also be activated. Go to the "Settings" tab of Peroxide, where you can see a large blank space with the words "Code Here" that you can click on to get started.
Enter a code phrase into the blank space's text box, but make sure the code still works and doesn't have any grammatical errors. Even one number or letter out of place will be enough to prevent the code from working, causing you to lose out on many rewards. Always make sure to double-check how you've inputted codes before trying to activate them, as many phrases can only be used once by one player.
In a sharp similarity to other Bleach-inspired games like Soul Wars in Roblox, the codes you redeem offer a type of currency called Product Essence in Peroxide. This resource can be collected and taken to the character Kisuke and spent on rerolls for every path available in the game. You can find this NPC in The City, an area you may be familiar with after playing through the tutorial.
Product Essence can also be spent on cosmetic items for your character, giving you new ways to adjust your look as you play. Other items, slots, and accessories are also tied to Product Essence, reflecting how the material is at the core of Peroxide's gameplay. Those looking to explore everything this game has to offer will want to farm as much Essence as they can through codes right as the tutorial finishes.
Every Currently Active Peroxide Code
Share Rewards Across All Saved Slots
Every save slot you have will share Product Essence in one large pool, which prevents you from having to grind on multiple slots for more currency. However, keep in mind that this single collection of Essence can be spent quickly as a result, so you need to plan carefully for what you buy. Once again, codes can only be redeemed once per account, limiting the total Essence you can get at a time before new phrases drop.
Multiple accounts can be made to use a Peroxide active code more than once, but the Product Essence you receive can only be used on the account that redeemed the resources.
As you can see in the above video by YouTube creator Corgi, the message "Already Used Code" will pop up in Peroxide if you have already used a phrase on your account. Even with earned Robux in Roblox, you will be unable to get more of this currency for free until more codes are active. For now, the codes available in the game are:
Active Code
Rewards
SkibiShutdown
30 Product Essence
GokuDayCodeSuper2
15 Product Essence
310KLikesHappyWeekend
25 Product Essence
230MVisitsCodeCritters
25 Product Essence
sorry4thebugs
25 Product Essence
220MVisitsArrancarTerrorism
30 Product Essence
AlvinAndTheChipmunks
30 Product Essence
FusionHoldingUsHostageUpdateIsComing
25 Product Essence
EclipseDontBurnUrEyes
15 Product Essence
330kLikesSorryLate
35 Product Essence
20BILLIONTIRLLCOINDDOIFDSUPERNOTSCAMCODE
Random Amount of Product Essence
TwoTrillionAprilPECode
2 Trillion Product Essence
ShutdownToFixNPCsAgain
25 Product Essence
210MVisitsAwesome
30 Product Essence
PeroxideAnniPE
50 Product Essence
UnluckyBruhxide
50 Product Essence
290kLikesLOOLOLOL
30 Product Essence
200MVisitsAwesome
25 Product Essence
ValentinesDayButNoValentines
45 Product Essence
FusionStopGamblingWorkOnTheGame
25 Product Essence
FusionForgotHowToShutdown
Random amount of Product Essence
190mVisitsThanks
30 Product Essence
ThanksForPingingAhmed
25 Product Essence
280kLikesThankYouForYourSupport
25 Product Essence
180mVistsTrollDelay
20 Product Essence
CodeCrittersVsBugFixers
20 Product Essence
CodeCrittersVsBugFixersPart2
15 Product Essence
StopListeningToTrialMods
25 Product Essence
HappyNewYearJoMamaJoeBiden12121
20 Product Essence
Chungsmas
30 Product Essence
170mVisitsGuys
15 Product Essence
270kLikesOhHowJolly
15 Product Essence
FBBossIncident
15 Product Essence
FBUpdate
15 Product Essence, 1 Slot
How To Check If Codes Have Expired
Look At Multiple Sources
Although simply entering a code and its failure to work could tell you whether it has expired or not, there are some situations where a code not working suddenly activates. To avoid confusion, the best way to see if a code has expired is to check how long it has been operating or see what dates other players report using it. Oftentimes, some codes that others claim to work have long since expired following the phrase's release.
Unfortunately, the developers of Peroxide have not updated many of the codes on their social sites with expiration dates. Unlike many of the most popular Roblox games on the platform right now, it can be hard to tell which codes are working at any moment. Even from the list provided above, there may be some phrases that have expired in the months following this time of writing.
You can always message other players to make sure a certain code does or does not work, but you should always try inputting a phrase multiple times when you get stuck. After a few attempts, accept that one code may be lost and move on to the next one. Figuring out how to use codes for Peroxide in Roblox may cause some struggles here and there if you don't follow the right steps as you go.
![Ethan Blackstone Ethan Blackstone]() Ethan Blackstone
2024-05-24
Ethan Blackstone
2024-05-24